Introduction
Privileged Access Management (PAM) tools are cybersecurity solutions designed to control, monitor, and secure access to critical systems and high-level accounts within an organization. These “privileged accounts” include admin users, IT operators, DevOps engineers, and service accounts that have elevated permissions across systems.
If these accounts are compromised, attackers can gain full control over infrastructure, databases, cloud environments, and sensitive enterprise systems. PAM tools help prevent this by enforcing strict access controls, session monitoring, credential vaulting, and least-privilege principles.
In modern security architectures, PAM is a core pillar of Zero Trust security, ensuring that no user is trusted by default—even inside the network.
Why PAM matters today
- Protects high-value admin accounts from compromise
- Reduces insider threat risks
- Prevents lateral movement in cyberattacks
- Enforces least-privilege access models
- Strengthens compliance and audit readiness
- Secures hybrid and cloud environments
Common use cases
- Securing IT administrator access
- Managing cloud and infrastructure credentials
- Controlling database and server access
- Monitoring privileged user sessions
- Rotating and vaulting sensitive credentials
- Enforcing temporary elevated access
Key evaluation criteria
- Credential vaulting and rotation
- Session recording and monitoring
- Least privilege enforcement
- Just-in-time (JIT) access controls
- Multi-factor authentication support
- Cloud and hybrid deployment support
- Audit logs and compliance reporting
- Integration with IAM and SIEM tools
- API automation capabilities
- Scalability for enterprise environments
Best for:
PAM tools are best for enterprises, financial institutions, government organizations, cloud-native companies, and IT teams managing critical infrastructure systems.
Not ideal for:
They are less necessary for very small teams or environments without privileged administrative access complexity.
Key Trends in PAM Tools
- Adoption of Just-In-Time (JIT) privileged access
- Integration with Zero Trust architecture frameworks
- AI-based anomaly detection for privileged sessions
- Shift toward cloud-native PAM solutions
- Increased automation in credential rotation
- Session recording with behavioral analytics
- Expansion into DevOps and CI/CD environments
- Stronger API security and machine identity management
- Integration with Identity Governance (IGA) platforms
- Passwordless privileged access adoption
How We Selected These Tools (Methodology)
- Global enterprise adoption and usage
- Strength of privileged account security controls
- Credential vaulting and rotation capabilities
- Session monitoring and auditing depth
- Integration with IAM, SIEM, and cloud platforms
- Scalability across hybrid environments
- Compliance and governance readiness
- Automation and API capabilities
- Vendor maturity and reliability
- Real-world enterprise security effectiveness
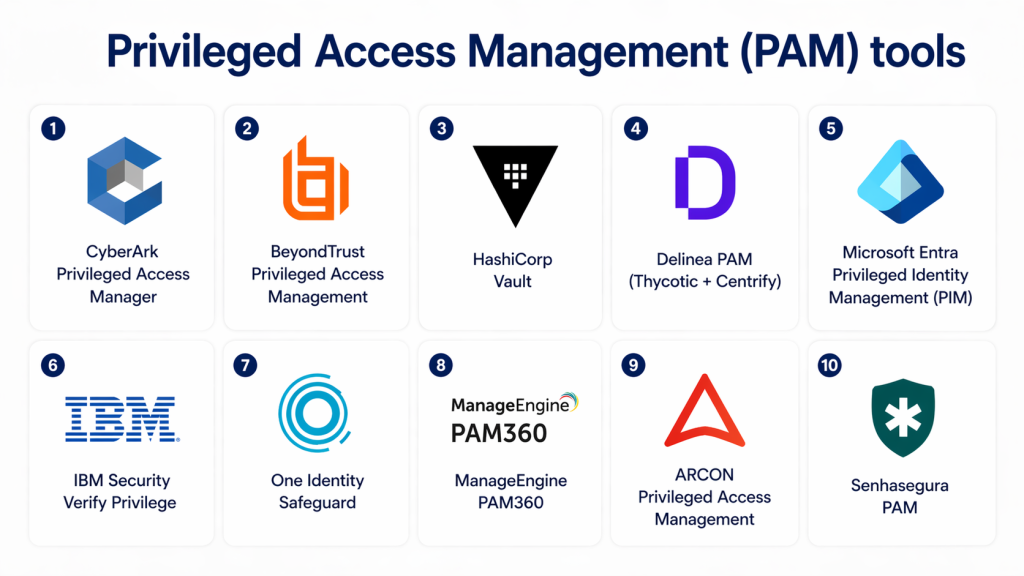
Top 10 Privileged Access Management (PAM) Tools
1 — CyberArk Privileged Access Manager
Short description:
CyberArk is one of the most widely adopted PAM platforms, focused on securing privileged credentials and controlling high-risk access across enterprise environments.
Key Features
- Secure credential vaulting
- Automatic password rotation
- Session recording and monitoring
- Just-in-time privileged access
- Least privilege enforcement
- Endpoint privilege security
- Threat analytics for privileged accounts
Pros
- Industry-leading PAM solution
- Strong enterprise security controls
- Deep compliance support
Cons
- Complex deployment
- Higher cost for smaller organizations
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Zero-trust architecture support
- MFA integration
- Detailed audit logging
Integrations & Ecosystem
- IAM platforms
- SIEM systems
- Cloud providers
- DevOps tools
Support & Community
Strong enterprise-grade global support.
2 — BeyondTrust Privileged Access Management
Short description:
BeyondTrust provides comprehensive PAM solutions with strong session control and credential security.
Key Features
- Password vaulting
- Session monitoring and recording
- Least privilege access control
- Endpoint privilege management
- Just-in-time access
- API-based automation
- Risk-based access policies
Pros
- Strong session control features
- Easy integration with IT systems
- Flexible deployment options
Cons
- UI complexity in large deployments
- Premium pricing
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- RBAC and MFA
- Audit logs
- Compliance reporting
Integrations & Ecosystem
- SIEM tools
- IAM platforms
- Cloud environments
- ITSM tools
Support & Community
Strong enterprise support ecosystem.
3 — HashiCorp Vault (PAM capabilities)
Short description:
HashiCorp Vault provides secrets management and privileged access control for modern infrastructure and DevOps environments.
Key Features
- Dynamic secrets generation
- Encryption-as-a-service
- Token-based authentication
- Secure credential storage
- API-driven access control
- Lease-based access expiration
- Cloud-native integration
Pros
- Strong DevOps integration
- Highly flexible and scalable
- API-first architecture
Cons
- Requires technical expertise
- Complex setup for beginners
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Encryption at rest and in transit
- Access policies
- Audit logging
Integrations & Ecosystem
- Kubernetes
- CI/CD pipelines
- Cloud providers
- DevOps tools
Support & Community
Strong open-source and enterprise support.
4 — Delinea PAM (Thycotic + Centrify)
Short description:
Delinea offers unified PAM solutions for securing privileged identities across hybrid environments.
Key Features
- Privileged account discovery
- Credential vaulting
- Session management
- Just-in-time access
- Role-based access control
- Password rotation automation
- Cloud and on-prem support
Pros
- Strong hybrid environment support
- Easy-to-use interface
- Good scalability
Cons
- Advanced features require configuration
- Enterprise pricing model
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- MFA support
- Audit logs
- Compliance reporting
Integrations & Ecosystem
- IAM systems
- SIEM tools
- Cloud platforms
- ITSM systems
Support & Community
Strong enterprise support.
5 — IBM Security Verify Privilege
Short description:
IBM PAM provides enterprise-grade privileged access security with identity governance integration.
Key Features
- Privileged session monitoring
- Credential vaulting
- Access governance
- Risk-based access control
- Identity lifecycle integration
- Automation policies
- Audit reporting
Pros
- Strong enterprise governance
- Deep integration with IBM ecosystem
- Advanced analytics
Cons
- Complex deployment
- Enterprise-focused pricing
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC and encryption
- Compliance-ready reporting
- Audit logs
Integrations & Ecosystem
- IBM security suite
- IAM systems
- SIEM tools
- Cloud platforms
Support & Community
Strong enterprise IBM support.
6 — One Identity Safeguard
Short description:
One Identity Safeguard provides secure privileged access management with strong session monitoring and governance.
Key Features
- Password vaulting
- Session recording
- Access request workflows
- Just-in-time access
- Privileged session analytics
- Risk-based controls
- Automated credential rotation
Pros
- Strong session visibility
- Good governance tools
- Scalable enterprise design
Cons
- Setup complexity
- Higher enterprise cost
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- MFA support
- Audit trails
- Encryption standards
Integrations & Ecosystem
- IAM systems
- SIEM platforms
- Cloud providers
- ITSM tools
Support & Community
Strong enterprise support.
7 — Microsoft Entra Privileged Identity Management (PIM)
Short description:
Microsoft Entra PIM provides just-in-time privileged access control within Microsoft environments.
Key Features
- Just-in-time privileged access
- Role activation workflows
- Access reviews
- Conditional access policies
- MFA enforcement
- Privileged role auditing
- Time-bound access control
Pros
- Deep Microsoft integration
- Strong cloud-native support
- Easy adoption in Azure environments
Cons
- Microsoft ecosystem dependency
- Limited multi-vendor flexibility
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Conditional access policies
- MFA enforcement
- Audit logging
Integrations & Ecosystem
- Microsoft Azure
- Microsoft 365
- Enterprise IAM systems
- Security tools
Support & Community
Strong Microsoft enterprise support.
8 — ARCON PAM
Short description:
ARCON provides enterprise PAM solutions with strong compliance and privileged session management capabilities.
Key Features
- Privileged account vaulting
- Session monitoring
- Access control policies
- Real-time session alerts
- Password rotation
- User activity tracking
- Compliance dashboards
Pros
- Strong compliance focus
- Good enterprise security coverage
- Flexible deployment
Cons
- Less global adoption than top vendors
- UI complexity
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- MFA and encryption
- Audit logs
- Compliance reporting
Integrations & Ecosystem
- IAM systems
- SIEM tools
- Enterprise applications
- APIs
Support & Community
Strong regional enterprise support.
9 — ManageEngine PAM360
Short description:
ManageEngine PAM360 provides centralized privileged access control and monitoring for enterprises and SMBs.
Key Features
- Password vaulting
- Session monitoring
- Privileged account discovery
- Access control policies
- Workflow-based approvals
- Credential rotation
- Reporting dashboards
Pros
- Cost-effective PAM solution
- Easy deployment
- Good SMB and mid-market fit
Cons
- Limited advanced enterprise analytics
- Less scalability than premium tools
Platforms / Deployment
- Cloud / On-prem
Security & Compliance
- RBAC support
- Audit logs
- Encryption
Integrations & Ecosystem
- ITSM tools
- SIEM platforms
- Cloud systems
- APIs
Support & Community
Good mid-market support.
10 — Senhasegura PAM
Short description:
Senhasegura provides enterprise PAM with strong session control and automation capabilities.
Key Features
- Credential vaulting
- Session recording
- Privileged access workflows
- Password rotation automation
- API access management
- Risk-based access control
- Compliance reporting
Pros
- Strong automation features
- Good enterprise scalability
- Comprehensive PAM coverage
Cons
- Smaller global ecosystem
- Learning curve for configuration
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Encryption support
- MFA integration
- Audit logs
Integrations & Ecosystem
- IAM systems
- SIEM tools
- Cloud platforms
- DevOps tools
Support & Community
Growing enterprise support base.
Comparison Table (Top 10)
| Tool | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| CyberArk | Enterprises | Multi | Hybrid | Industry-leading PAM | N/A |
| BeyondTrust | Enterprises | Multi | Hybrid | Strong session control | N/A |
| HashiCorp Vault | DevOps teams | Multi | Hybrid | API-first secrets mgmt | N/A |
| Delinea | Hybrid orgs | Multi | Hybrid | Unified PAM suite | N/A |
| IBM Verify Privilege | Large enterprises | Multi | Hybrid | Identity governance | N/A |
| One Identity | Enterprises | Multi | Hybrid | Session analytics | N/A |
| Microsoft PIM | Azure users | Microsoft | Cloud | JIT access control | N/A |
| ARCON PAM | Enterprises | Multi | Hybrid | Compliance focus | N/A |
| ManageEngine PAM360 | SMB/mid-market | Multi | Hybrid | Cost-effective PAM | N/A |
| Senhasegura | Enterprises | Multi | Hybrid | Automation-driven PAM | N/A |
Evaluation & Scoring of PAM Tools
| Tool | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Total |
|---|---|---|---|---|---|---|---|---|
| CyberArk | 10 | 7 | 10 | 10 | 9 | 9 | 7 | 8.8 |
| BeyondTrust | 9 | 8 | 9 | 10 | 9 | 9 | 8 | 8.8 |
| HashiCorp Vault | 9 | 6 | 10 | 10 | 9 | 8 | 9 | 8.6 |
| Delinea | 9 | 8 | 9 | 9 | 9 | 9 | 8 | 8.7 |
| IBM Verify | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.6 |
| One Identity | 9 | 7 | 9 | 9 | 9 | 9 | 7 | 8.5 |
| Microsoft PIM | 9 | 9 | 10 | 10 | 9 | 9 | 9 | 9.1 |
| ARCON | 8 | 7 | 8 | 9 | 8 | 8 | 8 | 8.1 |
| ManageEngine | 8 | 9 | 8 | 8 | 8 | 8 | 9 | 8.3 |
| Senhasegura | 8 | 7 | 8 | 9 | 8 | 8 | 8 | 8.1 |
Which PAM Tool Is Right for You?
SMB / Startups
- ManageEngine PAM360
- Senhasegura
- Delinea (light deployment)
Mid-Market
- BeyondTrust
- ManageEngine PAM360
- One Identity
Enterprise
- CyberArk
- Microsoft Entra PIM
- IBM Security Verify Privilege
- HashiCorp Vault (DevOps-heavy environments)
Frequently Asked Questions (FAQs)
1. What is PAM?
PAM (Privileged Access Management) is a security system that controls and monitors access to critical accounts and systems.
2. Why is PAM important?
Because privileged accounts have high-level access that can damage systems if compromised.
3. What is a privileged account?
It is an account with administrative or elevated permissions over systems or infrastructure.
4. Is PAM part of IAM?
Yes, PAM is a specialized part of Identity & Access Management.
5. Does PAM support cloud environments?
Yes, most modern PAM tools support cloud, on-prem, and hybrid systems.
6. What is just-in-time access?
It gives temporary privileged access only when needed, reducing risk.
7. Can PAM prevent insider threats?
Yes, it monitors and controls privileged user activity.
8. Is PAM difficult to implement?
Enterprise PAM tools can be complex, but SMB solutions are easier.
9. Does PAM record sessions?
Yes, most tools record and monitor privileged sessions for audit purposes.
10. Which industries use PAM most?
Banking, IT, healthcare, government, SaaS, and large enterprises.
Conclusion
Privileged Access Management (PAM) is a critical cybersecurity layer that protects the most sensitive access points in any organization. By controlling, monitoring, and securing privileged accounts, PAM reduces the risk of data breaches and insider threats.
From enterprise leaders like CyberArk and BeyondTrust to developer-focused solutions like HashiCorp Vault, each platform serves different levels of infrastructure complexity and security needs.
Choosing the right PAM solution depends on your architecture, compliance requirements, and operational scale. A strong PAM strategy ensures secure privileged access, reduced cyber risk, and full visibility into high-risk system activity.