Introduction
Key Management Systems (KMS) are security platforms designed to create, store, distribute, rotate, and manage cryptographic keys used for encrypting and decrypting sensitive data. These systems act as the backbone of modern encryption strategies, ensuring that data remains secure across cloud, on-premise, and hybrid environments.
In today’s digital ecosystem, where data breaches and cyberattacks are increasing, managing encryption keys securely is just as important as encryption itself. A weak or poorly managed key system can compromise even the strongest encryption.
Modern KMS platforms provide centralized key control, automated key rotation, hardware security integration, and compliance support for regulations like GDPR, HIPAA, and PCI-DSS.
Common use cases include:
- Cloud data encryption management
- Database and application encryption
- Secure API and microservices communication
- Compliance with security regulations
- Enterprise-wide key lifecycle management
Key evaluation criteria:
- Key lifecycle management (create, rotate, revoke)
- Security (HSM support, encryption standards)
- Cloud and hybrid compatibility
- Automation and policy control
- Integration with cloud and enterprise systems
- Audit logging and compliance support
- Performance and scalability
- Ease of use and API support
Best for: Enterprises, cloud-native applications, fintech, healthcare, and any organization handling sensitive encrypted data.
Not ideal for: Small applications with minimal encryption needs or systems without sensitive data handling requirements.
Key Trends in Key Management Systems
- Cloud-native KMS adoption across AWS, Azure, and GCP
- Hardware Security Modules (HSM) integration for maximum security
- Automated key rotation and lifecycle management
- Zero-trust security architecture integration
- API-first KMS platforms for DevOps workflows
- Multi-cloud and hybrid key management support
- Encryption-as-a-Service (EaaS) models
- Increased focus on compliance automation and auditability
- AI-driven anomaly detection in key usage patterns
- Separation of key ownership and data storage for security
How We Selected These Tools (Methodology)
- Strong enterprise adoption and cloud usage
- Support for full key lifecycle management
- Integration with major cloud and enterprise platforms
- Security certifications and compliance readiness
- Availability of HSM and encryption standards support
- Scalability for high-volume workloads
- API and automation capabilities
- Fit across SMB, mid-market, and enterprise
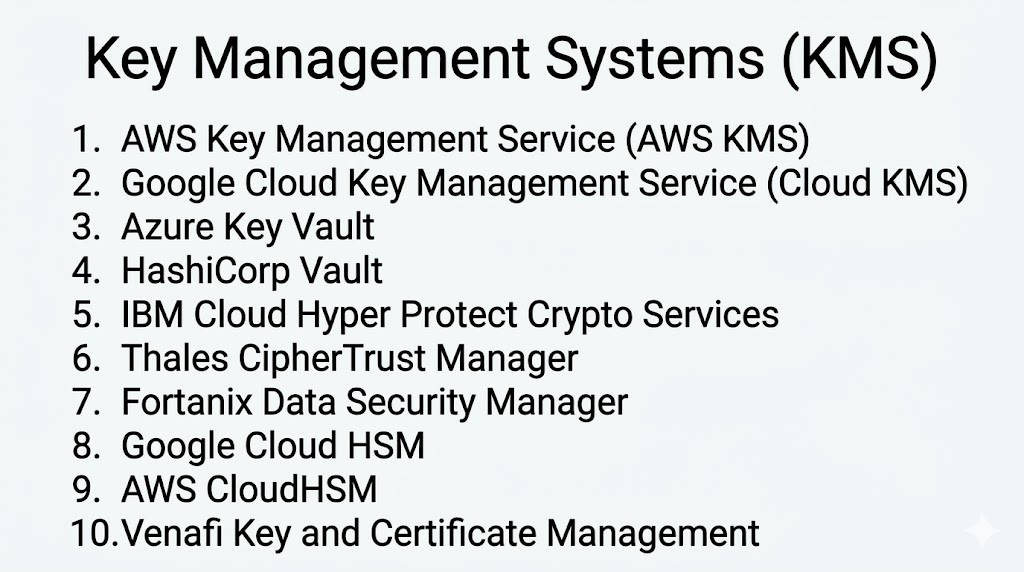
Top 10 Key Management Systems (KMS)
#1 — AWS Key Management Service (AWS KMS)
Short description: A fully managed AWS service that enables secure creation and control of encryption keys used across AWS services and applications.
Key Features
- Centralized key management
- Automatic key rotation
- Integration with AWS services
- IAM-based access control
- Audit logging via CloudTrail
Pros
- Deep AWS ecosystem integration
- Highly scalable and reliable
Cons
- AWS ecosystem dependency
- Limited portability outside AWS
Platforms / Deployment
Cloud
Security & Compliance
FIPS 140-2 validated encryption; Not publicly stated
Integrations & Ecosystem
- AWS services
- APIs
- Enterprise applications
Support & Community
Strong AWS enterprise support
#2 — Google Cloud Key Management Service
Short description: A cloud-native key management solution that allows organizations to manage cryptographic keys for Google Cloud services.
Key Features
- Centralized key control
- Automatic key rotation
- IAM-based access
- Audit logging
- Cloud-native encryption
Pros
- Strong Google Cloud integration
- Easy to deploy
Cons
- Limited outside GCP ecosystem
- Advanced features require setup
Platforms / Deployment
Cloud
Security & Compliance
Encryption standards compliant; Not publicly stated
Integrations & Ecosystem
- Google Cloud services
- APIs
- SaaS tools
Support & Community
Strong cloud support
#3 — Azure Key Vault
Short description: A Microsoft cloud service for securely storing and managing cryptographic keys, secrets, and certificates.
Key Features
- Key and secret storage
- Certificate management
- Role-based access control
- Logging and monitoring
- Integration with Azure services
Pros
- Strong Azure ecosystem integration
- Easy enterprise adoption
Cons
- Azure dependency
- Complexity in hybrid setups
Platforms / Deployment
Cloud
Security & Compliance
Encryption, RBAC; Not publicly stated
Integrations & Ecosystem
- Azure services
- Microsoft 365
- APIs
Support & Community
Enterprise-grade support
#4 — HashiCorp Vault
Short description: A powerful open-source and enterprise-grade system for managing secrets, encryption keys, and access control across environments.
Key Features
- Dynamic secrets generation
- Encryption-as-a-service
- Key lifecycle management
- Access control policies
- API-driven architecture
Pros
- Highly flexible and secure
- Multi-cloud support
Cons
- Requires technical expertise
- Complex setup
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Strong encryption standards; Not publicly stated
Integrations & Ecosystem
- Kubernetes
- Cloud platforms
- DevOps tools
Support & Community
Strong developer community
#5 — IBM Cloud Hyper Protect Crypto Services
Short description: A high-security key management service offering dedicated HSM-backed encryption key control.
Key Features
- Hardware-backed key storage
- Dedicated HSM integration
- Key lifecycle management
- Cloud encryption support
- Compliance tools
Pros
- High-level security with HSM
- Strong compliance support
Cons
- Complex setup
- Enterprise-focused
Platforms / Deployment
Cloud
Security & Compliance
HSM-based encryption; Not publicly stated
Integrations & Ecosystem
- IBM Cloud
- APIs
- Enterprise systems
Support & Community
Enterprise support
#6 — Thales CipherTrust Manager
Short description: An enterprise key management platform designed to centralize encryption key control across hybrid and multi-cloud environments.
Key Features
- Centralized key management
- Data encryption control
- Policy enforcement
- Audit logging
- Multi-cloud support
Pros
- Strong enterprise security
- Hybrid environment support
Cons
- High cost
- Complex deployment
Platforms / Deployment
Cloud / On-premise
Security & Compliance
FIPS-certified encryption; Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- Enterprise applications
- APIs
Support & Community
Strong enterprise support
#7 — Fortanix Data Security Manager
Short description: A unified data security platform offering encryption key management and confidential computing capabilities.
Key Features
- Key lifecycle management
- Encryption-as-a-service
- Multi-cloud support
- Confidential computing
- Policy-based access control
Pros
- Modern cloud-native design
- Strong security automation
Cons
- Enterprise pricing
- Requires onboarding
Platforms / Deployment
Cloud / Hybrid
Security & Compliance
Strong encryption standards; Not publicly stated
Integrations & Ecosystem
- APIs
- Cloud platforms
- Security tools
Support & Community
Enterprise support
#8 — Google Cloud HSM
Short description: A hardware-backed key management service providing high-security cryptographic operations within Google Cloud.
Key Features
- Hardware security module support
- Key storage and generation
- Encryption operations
- Cloud integration
- Audit logging
Pros
- High-level hardware security
- Strong compliance readiness
Cons
- Expensive
- Requires cloud expertise
Platforms / Deployment
Cloud
Security & Compliance
HSM-based security; Not publicly stated
Integrations & Ecosystem
- Google Cloud services
- APIs
- Enterprise systems
Support & Community
Strong enterprise support
#9 — AWS CloudHSM
Short description: A cloud-based hardware security module service that provides dedicated encryption key storage for AWS users.
Key Features
- Dedicated HSM instances
- Key generation and storage
- Strong encryption support
- AWS integration
- Compliance tools
Pros
- High security isolation
- AWS-native integration
Cons
- Complex setup
- Higher cost
Platforms / Deployment
Cloud
Security & Compliance
HSM-based encryption; Not publicly stated
Integrations & Ecosystem
- AWS services
- APIs
- Enterprise apps
Support & Community
Strong AWS support
#10 — Venafi Key and Certificate Management
Short description: A platform focused on managing encryption keys and digital certificates across enterprise environments.
Key Features
- Key lifecycle management
- Certificate management
- Policy automation
- Audit tracking
- Compliance reporting
Pros
- Strong certificate + key management
- Enterprise-grade automation
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Encryption, policy enforcement; Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- DevOps tools
- APIs
Support & Community
Enterprise support
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| AWS KMS | AWS users | Web | Cloud | Native AWS integration | N/A |
| Google KMS | GCP users | Web | Cloud | Cloud-native encryption | N/A |
| Azure Key Vault | Microsoft users | Web | Cloud | Secrets + keys | N/A |
| HashiCorp Vault | DevOps teams | Multi-OS | Cloud/On-prem | API-driven secrets | N/A |
| IBM Hyper Protect | High-security enterprise | Web | Cloud | HSM-backed security | N/A |
| Thales CipherTrust | Hybrid enterprise | Web | Cloud/On-prem | Multi-cloud control | N/A |
| Fortanix DSM | Cloud security | Web | Cloud/Hybrid | Confidential computing | N/A |
| Google Cloud HSM | High security | Web | Cloud | Hardware security | N/A |
| AWS CloudHSM | AWS enterprise | Web | Cloud | Dedicated HSM | N/A |
| Venafi | Certificate + key mgmt | Web | Cloud/On-prem | Policy automation | N/A |
Evaluation & Scoring of Key Management Systems
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| AWS KMS | 9 | 9 | 9 | 9 | 9 | 9 | 8 | 8.8 |
| Google KMS | 9 | 9 | 8 | 9 | 9 | 8 | 8 | 8.6 |
| Azure Key Vault | 9 | 9 | 9 | 9 | 9 | 9 | 8 | 8.8 |
| HashiCorp Vault | 9 | 7 | 9 | 10 | 9 | 8 | 8 | 8.5 |
| IBM Hyper Protect | 9 | 6 | 8 | 10 | 9 | 8 | 7 | 8.3 |
| Thales CipherTrust | 9 | 6 | 8 | 10 | 9 | 8 | 6 | 8.2 |
| Fortanix DSM | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.1 |
| Google HSM | 9 | 6 | 8 | 10 | 9 | 8 | 7 | 8.2 |
| AWS CloudHSM | 9 | 6 | 8 | 10 | 9 | 8 | 7 | 8.2 |
| Venafi | 9 | 6 | 8 | 9 | 8 | 8 | 7 | 8.0 |
How to interpret scores:
- 8.5+ → Best-in-class enterprise KMS
- 8–8.5 → Strong enterprise-grade tools
- Below 8 → Specialized or niche use cases
Which KMS Tool Is Right for You?
Solo / Freelancer
Basic cloud KMS like AWS KMS or Azure Key Vault
SMB
Cloud-native KMS solutions for simple encryption needs
Mid-Market
HashiCorp Vault or Fortanix for flexibility and control
Enterprise
Thales, IBM, AWS CloudHSM for advanced security
Budget vs Premium
- Budget → Cloud-native KMS
- Premium → HSM-based enterprise solutions
Feature Depth vs Ease of Use
- Cloud KMS → Easy setup
- Enterprise KMS → High security, complex setup
Integrations & Scalability
Choose tools that integrate with cloud, DevOps, and security stacks
Security & Compliance Needs
Highly regulated industries should prioritize HSM-backed systems
Frequently Asked Questions (FAQs)
1. What is a Key Management System (KMS)?
It is a platform used to create, store, and manage encryption keys securely.
2. Why is KMS important?
It ensures encrypted data remains secure by protecting encryption keys.
3. What is the difference between KMS and HSM?
KMS is software-based management; HSM provides hardware-backed security.
4. Are cloud KMS tools secure?
Yes, they use industry-standard encryption and access controls.
5. Can KMS work across multiple clouds?
Yes, tools like HashiCorp Vault support multi-cloud environments.
6. Do KMS tools support automation?
Yes, most platforms support automated key rotation and lifecycle management.
7. Are KMS tools required for compliance?
Yes, many regulations require proper key management for encryption.
8. Can KMS integrate with applications?
Yes, most provide APIs for integration with apps and services.
9. What industries use KMS tools?
Banking, healthcare, fintech, government, and cloud providers.
10. What are common mistakes in KMS usage?
Poor key rotation and weak access control policies.
Conclusion
Key Management Systems (KMS) are a critical foundation of modern cybersecurity, ensuring that encryption keys are securely managed throughout their lifecycle. Without proper key management, even the strongest encryption systems can become vulnerable. Modern KMS platforms offer automation, scalability, and integration with cloud ecosystems, making them essential for organizations handling sensitive data. From cloud-native solutions like AWS KMS to enterprise-grade HSM-backed systems like Thales and IBM, the market offers solutions for every scale and complexity. The right choice depends on your environment—cloud-first organizations benefit from native KMS tools, while enterprises with strict compliance requirements often rely on HSM-based systems. Instead of focusing only on features, organizations should evaluate security requirements, integration needs, and scalability before selecting a solution.