Introduction
Database Security Tools are specialized platforms designed to protect databases from unauthorized access, data breaches, insider threats, and cyberattacks. Since databases store critical business data like customer records, financial information, and application data, they are one of the most targeted assets in any organization.
Modern database security tools go beyond simple access control. They provide real-time monitoring, encryption, vulnerability scanning, activity auditing, and threat detection to ensure complete protection across cloud and on-premise databases.
Common use cases include:
- Database activity monitoring (DAM)
- Data encryption at rest and in transit
- Privileged user access control
- SQL injection detection and prevention
- Compliance auditing (GDPR, HIPAA, PCI-DSS)
Key evaluation criteria:
- Real-time monitoring & alerts
- Data encryption capabilities
- Access control & privilege management
- Threat detection & anomaly analysis
- Database coverage (SQL, NoSQL, cloud DBs)
- Compliance reporting & auditing
- Performance impact on databases
- Ease of deployment & integration
Best for: Enterprises, banking systems, SaaS platforms, healthcare organizations, and any business handling sensitive structured data.
Not ideal for: Small applications with minimal sensitive data or non-production environments.
Key Trends in Database Security Tools
- AI-driven anomaly detection in database activity
- Zero Trust database access models
- Cloud-native database security platforms
- Real-time SQL injection detection and prevention
- Automated compliance reporting and auditing
- Database encryption becoming default standard
- Integration with SIEM and SOAR systems
- Privileged access management (PAM) integration
- Behavioral analytics for insider threat detection
- Unified data security platforms replacing point tools
How We Selected These Tools (Methodology)
- Strong enterprise adoption across industries
- Coverage of monitoring, encryption, and access control
- Support for cloud, on-premise, and hybrid databases
- Proven threat detection and anomaly monitoring capabilities
- Compliance readiness (GDPR, HIPAA, PCI-DSS)
- Integration with security ecosystems (SIEM, IAM)
- Scalability for large enterprise databases
- Ease of deployment and usability
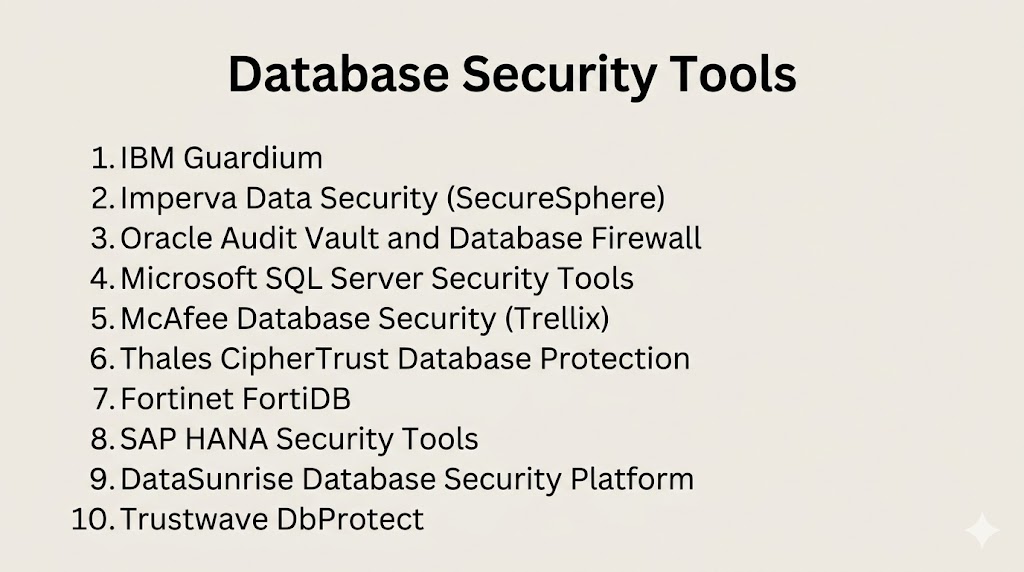
Top 10 Database Security Tools
#1 — IBM Guardium
Short description: A leading database security platform providing real-time monitoring, data protection, and compliance automation for enterprise databases.
Key Features
- Database activity monitoring (DAM)
- Real-time threat detection
- Data encryption and masking
- Compliance reporting
- Vulnerability assessment
Pros
- Enterprise-grade protection
- Strong compliance support
Cons
- Complex deployment
- High cost
Platforms / Deployment
Cloud / On-premise / Hybrid
Security & Compliance
Strong encryption, audit logs; Not publicly stated
Integrations & Ecosystem
- SIEM systems
- Databases (SQL/NoSQL)
- APIs
Support & Community
Enterprise-level support
#2 — Imperva Data Security (SecureSphere)
Short description: A comprehensive database security solution offering real-time monitoring, data protection, and threat prevention.
Key Features
- Database activity monitoring
- Threat detection
- Data masking
- Security analytics
- Compliance reporting
Pros
- Strong threat detection engine
- Broad database support
Cons
- Requires tuning
- Premium pricing
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Encryption, RBAC; Not publicly stated
Integrations & Ecosystem
- SIEM tools
- Databases
- Cloud platforms
Support & Community
Strong enterprise support
#3 — Oracle Audit Vault and Database Firewall
Short description: Oracle’s security solution for monitoring database activity and blocking unauthorized access attempts in real time.
Key Features
- Database activity monitoring
- Firewall protection
- Audit logging
- Compliance reporting
- Threat detection
Pros
- Deep Oracle DB integration
- Strong real-time protection
Cons
- Best for Oracle environments
- Limited flexibility outside Oracle
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Enterprise-grade encryption; Not publicly stated
Integrations & Ecosystem
- Oracle Database
- Enterprise systems
- APIs
Support & Community
Strong Oracle support
#4 — Microsoft SQL Server Security Tools
Short description: Built-in and extended security features within SQL Server for protecting databases from unauthorized access and vulnerabilities.
Key Features
- Role-based access control
- Transparent data encryption (TDE)
- Dynamic data masking
- Audit logs
- Threat detection
Pros
- Native SQL Server integration
- Easy to configure
Cons
- Limited to Microsoft ecosystem
- Requires SQL expertise
Platforms / Deployment
Windows / Cloud (Azure SQL)
Security & Compliance
Strong encryption and auditing; Not publicly stated
Integrations & Ecosystem
- Microsoft Azure
- Active Directory
- APIs
Support & Community
Strong Microsoft support
#5 — McAfee Database Security (Trellix)
Short description: A database protection platform focused on monitoring, vulnerability detection, and compliance enforcement.
Key Features
- Database activity monitoring
- Vulnerability assessment
- Real-time alerts
- Data protection
- Compliance tracking
Pros
- Strong enterprise security coverage
- Easy integration
Cons
- Complex setup
- UI improvements needed
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Encryption, audit logs; Not publicly stated
Integrations & Ecosystem
- SIEM systems
- Databases
- APIs
Support & Community
Enterprise support
#6 — Thales CipherTrust Database Protection
Short description: A data-centric security platform offering encryption, tokenization, and database protection.
Key Features
- Data encryption
- Tokenization
- Key management integration
- Database protection
- Policy enforcement
Pros
- Strong encryption capabilities
- Centralized data security
Cons
- Complex deployment
- High cost
Platforms / Deployment
Cloud / On-premise
Security & Compliance
FIPS-certified encryption; Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- Databases
- APIs
Support & Community
Strong enterprise support
#7 — Fortinet FortiDB
Short description: A database security and compliance solution offering monitoring, vulnerability assessment, and auditing.
Key Features
- Database activity monitoring
- Vulnerability scanning
- Audit logging
- Compliance reporting
- Real-time alerts
Pros
- Good Fortinet ecosystem integration
- Lightweight deployment
Cons
- Limited advanced analytics
- Smaller feature set
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Encryption; Not publicly stated
Integrations & Ecosystem
- Fortinet tools
- SIEM systems
- APIs
Support & Community
Good enterprise support
#8 — SAP HANA Security Tools
Short description: Built-in security features for SAP HANA databases to protect enterprise data and ensure compliance.
Key Features
- Role-based access control
- Data encryption
- Audit logging
- User authentication
- Compliance controls
Pros
- Deep SAP integration
- Strong enterprise governance
Cons
- SAP ecosystem dependency
- Complex configuration
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Enterprise encryption; Not publicly stated
Integrations & Ecosystem
- SAP ecosystem
- Enterprise systems
- APIs
Support & Community
Strong SAP support
#9 — DataSunrise Database Security Platform
Short description: A flexible database security platform offering real-time monitoring, masking, and compliance automation.
Key Features
- Database activity monitoring
- Data masking
- Threat detection
- Compliance automation
- Audit logs
Pros
- Easy multi-database support
- Strong compliance features
Cons
- Requires tuning
- Limited brand recognition
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Encryption; Not publicly stated
Integrations & Ecosystem
- Databases
- Cloud platforms
- APIs
Support & Community
Good support
#10 — Trustwave DbProtect
Short description: A database security solution providing monitoring, vulnerability management, and compliance reporting.
Key Features
- Database activity monitoring
- Vulnerability scanning
- Audit logging
- Compliance reporting
- Risk analysis
Pros
- Strong compliance focus
- Broad database support
Cons
- Complex setup
- UI limitations
Platforms / Deployment
Cloud / On-premise
Security & Compliance
Encryption; Not publicly stated
Integrations & Ecosystem
- SIEM tools
- Databases
- APIs
Support & Community
Enterprise support
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| IBM Guardium | Enterprise DB security | Multi | Cloud/On-prem | DAM + compliance | N/A |
| Imperva SecureSphere | Threat prevention | Multi | Cloud/On-prem | Real-time monitoring | N/A |
| Oracle Audit Vault | Oracle DB users | Multi | Cloud/On-prem | Oracle integration | N/A |
| SQL Server Tools | Microsoft users | Windows/Azure | Cloud/On-prem | Native security | N/A |
| McAfee DB Security | Enterprise monitoring | Multi | Cloud/On-prem | Vulnerability scanning | N/A |
| Thales CipherTrust | Data encryption | Multi | Cloud/On-prem | Tokenization | N/A |
| FortiDB | SMB/Enterprise | Multi | Cloud/On-prem | Lightweight security | N/A |
| SAP HANA Security | SAP users | Multi | Cloud/On-prem | SAP integration | N/A |
| DataSunrise | Multi-DB security | Multi | Cloud/On-prem | Data masking | N/A |
| Trustwave DbProtect | Compliance security | Multi | Cloud/On-prem | Audit + compliance | N/A |
Evaluation & Scoring of Database Security Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| IBM Guardium | 9 | 6 | 9 | 10 | 9 | 9 | 7 | 8.4 |
| Imperva | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.5 |
| Oracle AVDF | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.5 |
| SQL Server | 8 | 9 | 8 | 9 | 9 | 9 | 9 | 8.6 |
| McAfee DB Security | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| Thales CipherTrust | 9 | 6 | 9 | 10 | 9 | 9 | 7 | 8.4 |
| FortiDB | 7 | 8 | 7 | 8 | 8 | 8 | 8 | 7.8 |
| SAP HANA Security | 8 | 7 | 8 | 9 | 9 | 9 | 8 | 8.2 |
| DataSunrise | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.0 |
| Trustwave DbProtect | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 7.9 |
Which Database Security Tool Is Right for You?
Solo / Freelancer
Use built-in DB security features like SQL Server or basic cloud protections
SMB
FortiDB or DataSunrise for lightweight security
Mid-Market
Imperva or SAP HANA Security for balanced protection
Enterprise
IBM Guardium, Oracle AVDF, Thales CipherTrust for full-scale security
Budget vs Premium
- Budget → Built-in DB security tools
- Premium → Enterprise-grade monitoring platforms
Feature Depth vs Ease of Use
- Advanced tools → Deep visibility but complex
- Simple tools → Easy deployment but limited analytics
Integrations & Scalability
Choose tools compatible with SIEM, cloud, and enterprise DBs
Security & Compliance Needs
Highly regulated industries must prioritize audit logs, encryption, and monitoring
Frequently Asked Questions (FAQs)
1. What are Database Security Tools?
They are platforms that protect databases from unauthorized access, breaches, and attacks.
2. Why are they important?
Because databases store sensitive business and customer data that must be protected.
3. What do they monitor?
They monitor database activity, queries, access logs, and anomalies.
4. Do they support encryption?
Yes, most tools provide encryption for data at rest and in transit.
5. Are they required for compliance?
Yes, they help meet GDPR, HIPAA, PCI-DSS requirements.
6. Can they detect insider threats?
Yes, many tools use behavioral analytics to detect anomalies.
7. Do they work in the cloud?
Yes, most modern tools support cloud and hybrid environments.
8. Are they hard to implement?
Enterprise tools can be complex, but SMB tools are easier to deploy.
9. Do they slow down databases?
Some overhead exists, but optimized tools minimize impact.
10. Can they integrate with SIEM tools?
Yes, most integrate with SIEM and security ecosystems.
Conclusion
Database Security Tools are critical for protecting the most valuable asset in any organization—data. As cyber threats become more advanced, securing databases requires more than just passwords and firewalls. Modern solutions provide real-time monitoring, encryption, vulnerability detection, and compliance automation, making them essential for enterprises handling sensitive information. The right tool depends on your environment. Enterprises benefit from advanced platforms like IBM Guardium and Imperva, while smaller teams can rely on built-in database security features or lightweight tools. Ultimately, effective database security is not just about tools—it’s about continuous monitoring, strong policies, and layered defense strategies. By choosing the right platform, organizations can significantly reduce risk, improve compliance, and ensure long-term data protection.