Introduction
Exposure Management Platforms help organizations identify, analyze, prioritize, and reduce cybersecurity risks across their entire digital environment. Unlike traditional tools that focus only on vulnerabilities, exposure management platforms provide a holistic view of risk, combining asset discovery, vulnerability data, misconfigurations, identity risks, and threat intelligence into a single framework.
These platforms go beyond simple scanning by continuously discovering assets, mapping attack paths, and prioritizing the most critical risks based on real-world exploitability. This approach helps organizations focus on what actually matters instead of trying to fix everything at once.
Use Cases:
- Identifying and prioritizing critical security exposures
- Correlating vulnerabilities with real attack paths
- Managing cloud, SaaS, and on-prem risk in one place
- Supporting continuous threat exposure management (CTEM)
- Improving remediation workflows and decision-making
What buyers should evaluate:
- Full attack surface visibility (internal + external)
- Risk-based prioritization capabilities
- Integration with security tools (SIEM, SOAR, EDR)
- Automation and remediation workflows
- Asset discovery accuracy
- Ease of use and reporting
- Scalability across hybrid/cloud environments
- Security and compliance features
Best for: Enterprises, security leaders, SOC teams, and organizations with complex cloud, SaaS, and hybrid environments.
Not ideal for: Small organizations with limited infrastructure or those only needing basic vulnerability scanning.
Key Trends in Exposure Management Platforms
- Shift from vulnerability management to risk-based exposure management
- Integration of ASM, CAASM, and threat intelligence into one platform
- AI-driven prioritization of exploitable risks
- Continuous discovery of assets across cloud and SaaS
- Attack path analysis instead of static vulnerability lists
- Integration with DevSecOps pipelines
- Automation of remediation workflows
- Unified dashboards for business risk visibility
- Expansion into identity and access exposure analysis
- Adoption of CTEM (Continuous Threat Exposure Management) frameworks
How We Selected These Tools (Methodology)
- Market adoption and enterprise usage
- Breadth of exposure visibility (cloud, SaaS, on-prem)
- Risk prioritization capabilities
- Integration ecosystem strength
- Security and compliance readiness
- Scalability and performance
- Ease of onboarding and usability
- Innovation in exposure analytics
- Customer fit across segments
- Support, documentation, and community
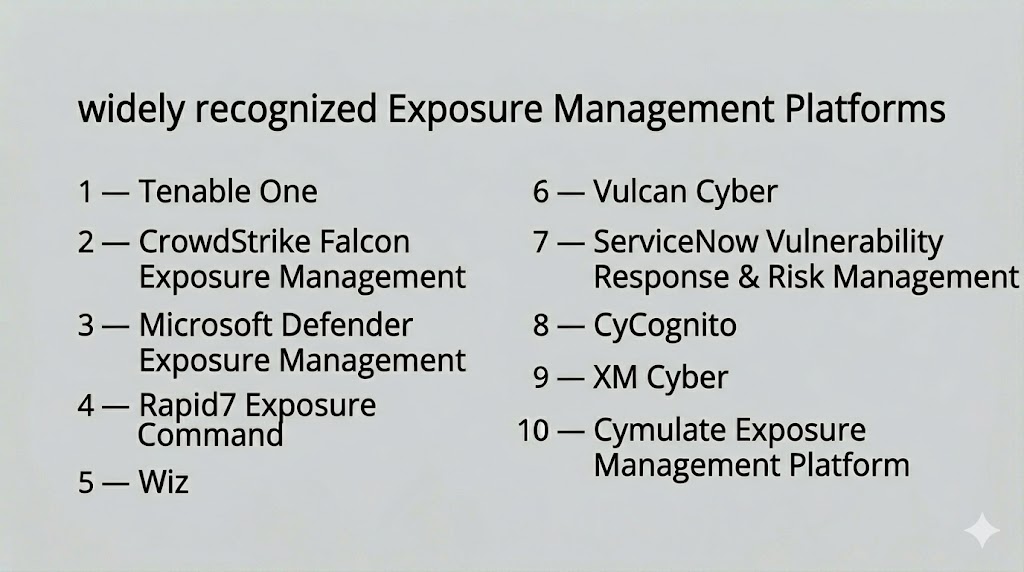
Top 10 Exposure Management Platforms
#1 — Tenable One (Exposure Management Platform)
Short description: A unified exposure management platform combining vulnerability management, attack surface visibility, and risk prioritization into a single system.
Key Features
- Unified exposure view across assets
- Risk-based prioritization
- Attack surface discovery
- Vulnerability management integration
- Analytics dashboards
- Continuous monitoring
Pros
- Strong integration of multiple security domains
- Comprehensive visibility
Cons
- Complex for beginners
- Enterprise pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, RBAC, encryption
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR, cloud platforms
- Vulnerability scanners
Support & Community
Enterprise support and detailed documentation.
#2 — CrowdStrike Falcon Exposure Management
Short description: A platform that combines endpoint, cloud, and identity data to provide real-time exposure insights and risk prioritization.
Key Features
- Real-time risk scoring
- Endpoint and cloud visibility
- Threat intelligence integration
- Automated workflows
- Asset discovery
Pros
- Strong real-time analytics
- Integrated ecosystem
Cons
- Requires Falcon platform
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, encryption
- Not publicly stated
Integrations & Ecosystem
- CrowdStrike ecosystem
- SIEM and cloud tools
Support & Community
Enterprise support and resources.
#3 — Microsoft Security Exposure Management (Defender Suite)
Short description: A platform providing unified exposure insights across endpoints, identities, and cloud environments within the Microsoft ecosystem.
Key Features
- Exposure scoring
- Asset visibility
- Risk prioritization
- Integration with Defender tools
- Threat intelligence
Pros
- Strong Microsoft integration
- Unified security visibility
Cons
- Limited outside Microsoft ecosystem
- Requires configuration
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, RBAC
- Not publicly stated
Integrations & Ecosystem
- Microsoft security stack
Support & Community
Enterprise-grade support.
#4 — Rapid7 Exposure Command
Short description: A platform focused on combining vulnerability data, threat intelligence, and asset visibility into actionable risk insights.
Key Features
- Risk prioritization
- Asset discovery
- Vulnerability correlation
- Attack path analysis
- Reporting dashboards
Pros
- Strong analytics
- Good integration capabilities
Cons
- Learning curve
- Requires tuning
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR, cloud platforms
Support & Community
Good documentation and support.
#5 — Wiz
Short description: A cloud-native exposure management platform that provides deep visibility into cloud risks and attack paths.
Key Features
- Cloud asset discovery
- Risk prioritization
- Attack path analysis
- Identity and access insights
- Data sensitivity mapping
Pros
- Strong cloud visibility
- Easy to deploy
Cons
- Cloud-focused
- Limited on-prem capabilities
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms and DevOps tools
Support & Community
Strong support and onboarding.
#6 — Vulcan Cyber
Short description: A risk-based vulnerability and exposure management platform that aggregates findings from multiple tools into prioritized actions.
Key Features
- Risk-based prioritization
- Integration with security tools
- Unified dashboards
- Workflow automation
- Reporting and analytics
Pros
- Strong aggregation capabilities
- Easy prioritization
Cons
- Depends on external tools
- Limited standalone scanning
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- SIEM, vulnerability scanners, cloud tools
Support & Community
Good support and documentation.
#7 — ServiceNow Vulnerability Response & Risk Management
Short description: A platform that integrates exposure management into IT workflows, enabling better risk prioritization and remediation tracking.
Key Features
- Risk-based vulnerability management
- Workflow automation
- Integration with ITSM
- Reporting dashboards
- Asset management
Pros
- Strong workflow integration
- Enterprise-ready
Cons
- Requires ServiceNow ecosystem
- Complex setup
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- ITSM, security tools
Support & Community
Enterprise support and training.
#8 — Picus Security
Short description: A platform that combines exposure management with breach and attack simulation for validation of security posture.
Key Features
- Attack simulation
- Risk validation
- Exposure prioritization
- Continuous testing
- Analytics dashboards
Pros
- Combines testing and exposure management
- Strong validation capabilities
Cons
- Requires expertise
- Niche use case
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security tools and platforms
Support & Community
Vendor support and documentation.
#9 — CyCognito
Short description: A platform that provides external exposure visibility and prioritizes risks based on attacker perspective.
Key Features
- Asset discovery
- Risk scoring
- Continuous monitoring
- Exposure analysis
- Threat intelligence integration
Pros
- Strong external visibility
- Automated discovery
Cons
- Limited internal coverage
- Learning curve
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- SIEM and security tools
Support & Community
Good documentation and support.
#10 — SentinelOne Singularity Platform
Short description: A platform that integrates endpoint security with exposure management capabilities for unified risk visibility.
Key Features
- Endpoint visibility
- Risk prioritization
- Threat detection
- Automated response
- Analytics dashboards
Pros
- Strong endpoint integration
- Real-time insights
Cons
- Focused on endpoint ecosystem
- Requires integration for full visibility
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Endpoint and cloud tools
Support & Community
Enterprise support and resources.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Tenable One | Enterprise | Web | Cloud | Unified exposure view | N/A |
| CrowdStrike Falcon | Enterprise | Web | Cloud | Real-time risk scoring | N/A |
| Microsoft Defender | Enterprise | Web | Cloud | Ecosystem integration | N/A |
| Rapid7 Exposure Command | Enterprise | Web | Cloud | Attack path analysis | N/A |
| Wiz | Cloud-first teams | Web | Cloud | Cloud risk visibility | N/A |
| Vulcan Cyber | Mid-market | Web | Cloud | Risk aggregation | N/A |
| ServiceNow | Enterprise | Web | Cloud | Workflow integration | N/A |
| Picus Security | Enterprise | Web | Cloud | Attack simulation | N/A |
| CyCognito | Enterprise | Web | Cloud | External visibility | N/A |
| SentinelOne | Enterprise | Web | Cloud | Endpoint integration | N/A |
Evaluation & Scoring of Exposure Management Platforms
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Tenable One | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| CrowdStrike | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Microsoft Defender | 8 | 8 | 7 | 8 | 8 | 7 | 7 | 7.9 |
| Rapid7 | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.9 |
| Wiz | 9 | 8 | 7 | 8 | 9 | 8 | 7 | 8.3 |
| Vulcan Cyber | 8 | 8 | 8 | 7 | 8 | 7 | 8 | 7.9 |
| ServiceNow | 8 | 7 | 7 | 8 | 8 | 8 | 7 | 7.8 |
| Picus | 7 | 7 | 7 | 7 | 7 | 7 | 7 | 7.0 |
| CyCognito | 8 | 7 | 7 | 7 | 8 | 7 | 7 | 7.6 |
| SentinelOne | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
Scores are comparative and reflect relative strengths across features, usability, integrations, and value. Higher scores indicate stronger enterprise readiness and broader exposure visibility.
Which Exposure Management Platform Is Right for You?
Solo / Freelancer
Exposure management platforms are generally unnecessary; basic security tools are sufficient.
SMB
Vulcan Cyber or simplified cloud tools provide manageable entry points.
Mid-Market
Rapid7 and Wiz offer balanced features and scalability.
Enterprise
Tenable One, CrowdStrike, and Microsoft Defender provide full exposure visibility.
Budget vs Premium
Budget tools focus on aggregation; premium tools provide deeper analytics and automation.
Feature Depth vs Ease of Use
Advanced platforms provide deeper insights but require training.
Integrations & Scalability
Choose tools that integrate with your full security stack.
Security & Compliance Needs
Ensure alignment with regulatory requirements and internal policies.
Frequently Asked Questions (FAQs)
What is Exposure Management?
Exposure management is the process of identifying, analyzing, and reducing all potential security risks across an organization’s environment.
How is it different from vulnerability management?
Vulnerability management focuses on known flaws, while exposure management includes misconfigurations, identity risks, and attack paths.
How is it different from ASM?
ASM focuses on discovering exposed assets, while exposure management prioritizes risk and remediation across the entire environment.
Why is exposure management important?
It helps reduce breach risk by focusing on exploitable threats rather than all vulnerabilities.
Do these platforms support cloud environments?
Yes, most platforms support cloud, SaaS, and hybrid environments.
Can exposure management automate remediation?
Many platforms provide automation features to accelerate remediation workflows.
Is exposure management continuous?
Yes, it is an ongoing process that adapts to changes in infrastructure and threats.
Who uses these platforms?
Security leaders, SOC teams, and IT teams use them to manage risk and prioritize actions.
What are common mistakes?
Trying to fix everything instead of prioritizing high-risk exposures.
Are these tools scalable?
Yes, they are designed for enterprise-scale environments and complex infrastructures.
Conclusion
Exposure Management Platforms represent the next evolution of cybersecurity by shifting focus from isolated vulnerabilities to holistic risk management. They provide organizations with a complete view of their attack surface, combining asset discovery, threat intelligence, and contextual prioritization into a unified framework.
These platforms help security teams move from reactive to proactive strategies by identifying the most critical exposures that attackers are likely to exploit. This reduces noise, improves efficiency, and enables faster remediation decisions.
Choosing the right platform depends on your organization’s complexity, existing tools, and security maturity. Enterprise environments benefit from integrated platforms, while smaller teams may prioritize ease of use and faster deployment.
The best approach is to shortlist a few platforms, test them in real environments, and validate how effectively they reduce risk across your infrastructure.