Introduction
Attack Surface Management (ASM) platforms help organizations discover, monitor, and manage all externally exposed digital assets that could be targeted by attackers. These tools continuously map an organization’s internet-facing infrastructure—including domains, IPs, cloud assets, APIs, and shadow IT—and identify potential security risks before they are exploited.
As organizations adopt cloud services, remote work, and third-party integrations, their attack surface expands rapidly and often becomes difficult to track. ASM platforms provide continuous visibility, risk prioritization, and automated monitoring to reduce blind spots and improve overall security posture.
Use Cases:
- Discovering unknown or shadow IT assets
- Monitoring exposed services and misconfigurations
- Identifying vulnerabilities in external-facing systems
- Managing third-party and vendor risks
- Supporting continuous security monitoring
What buyers should evaluate:
- Asset discovery accuracy and coverage
- Continuous monitoring capabilities
- Risk prioritization and scoring
- Integration with security tools (SIEM, SOAR, EDR)
- Ease of use and dashboard clarity
- Scalability across cloud and hybrid environments
- Automation and alerting features
- Compliance and reporting capabilities
Best for: Security teams, SOC analysts, enterprises, and organizations with large or dynamic digital footprints.
Not ideal for: Small organizations with limited external exposure or those relying only on internal security tools.
Key Trends in Attack Surface Management (ASM)
- Continuous discovery of external assets and shadow IT
- Integration with threat intelligence platforms
- AI-driven risk prioritization and scoring
- Expansion into cloud and multi-cloud environments
- Real-time monitoring and alerting
- Focus on third-party risk management
- Automation of remediation workflows
- Integration with DevSecOps processes
- Unified platforms combining ASM with vulnerability management
- Increased focus on external attack surface visibility
How We Selected These Tools (Methodology)
- Market adoption and recognition
- Depth of asset discovery capabilities
- Accuracy and reliability of monitoring
- Integration ecosystem strength
- Security and compliance features
- Scalability across environments
- Ease of use and onboarding
- Innovation in automation and analytics
- Customer fit across organization sizes
- Support and documentation quality
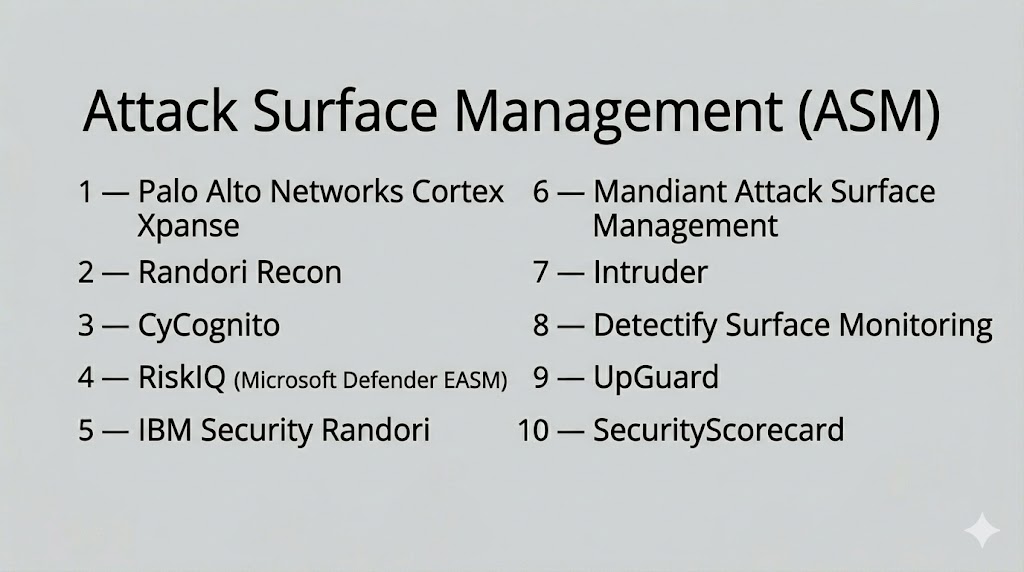
Top 10 Attack Surface Management (ASM) Tools
#1 — Palo Alto Networks Cortex Xpanse
Short description: A leading ASM platform that provides real-time visibility into external assets and continuously monitors for risks across global infrastructures.
Key Features
- Automated asset discovery
- Real-time monitoring
- Risk prioritization
- Cloud and network visibility
- Threat intelligence integration
Pros
- Highly accurate discovery
- Enterprise-grade scalability
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, RBAC, encryption
- Not publicly stated
Integrations & Ecosystem
Integrates with SIEM, SOAR, and cloud platforms.
- AWS, Azure
- Splunk
- ServiceNow
Support & Community
Enterprise support and detailed documentation.
#2 — Randori Recon
Short description: A platform focused on external attack surface discovery and risk prioritization based on attacker perspective.
Key Features
- External asset discovery
- Risk scoring
- Continuous monitoring
- Threat intelligence integration
- Attack simulation insights
Pros
- Attacker-centric approach
- Strong risk prioritization
Cons
- Limited internal visibility
- Requires tuning
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Security tools and APIs
Support & Community
Vendor support and onboarding resources.
#3 — CyCognito
Short description: An ASM platform that discovers unknown assets and assesses security risks across external infrastructures.
Key Features
- Asset discovery
- Risk assessment
- Continuous monitoring
- Automated alerts
- Security analytics
Pros
- Strong visibility into unknown assets
- Automated risk analysis
Cons
- Limited customization
- Learning curve
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- SIEM and security platforms
Support & Community
Good support and documentation.
#4 — Microsoft Defender EASM (RiskIQ)
Short description: A platform that provides visibility into external attack surfaces with integration into Microsoft security ecosystem.
Key Features
- Asset discovery
- Threat intelligence integration
- Risk monitoring
- Digital footprint mapping
- Analytics dashboards
Pros
- Strong Microsoft integration
- Comprehensive visibility
Cons
- Best suited for Microsoft environments
- Limited flexibility
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, RBAC
- Not publicly stated
Integrations & Ecosystem
- Microsoft security tools
Support & Community
Enterprise support and documentation.
#5 — IBM Security Randori
Short description: A platform that combines ASM with attack simulation to identify and prioritize exploitable risks.
Key Features
- Attack surface discovery
- Risk scoring
- Continuous monitoring
- Attack simulation
- Threat intelligence integration
Pros
- Combines ASM and simulation
- Strong analytics
Cons
- Complex setup
- Enterprise-focused pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- IBM security ecosystem
Support & Community
Professional support and documentation.
#6 — Mandiant Attack Surface Management
Short description: A platform delivering external visibility and threat intelligence to help organizations manage digital exposure.
Key Features
- Asset discovery
- Threat intelligence integration
- Risk monitoring
- Analytics dashboards
- Alerting system
Pros
- High-quality intelligence
- Strong analytics
Cons
- Premium pricing
- Limited customization
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Security tools and platforms
Support & Community
Enterprise support and expert insights.
#7 — Intruder
Short description: A user-friendly ASM and vulnerability scanning platform designed for SMBs and growing organizations.
Key Features
- Continuous scanning
- Risk prioritization
- Asset discovery
- Automated alerts
- Integration with cloud platforms
Pros
- Easy to use
- Suitable for SMBs
Cons
- Limited advanced features
- Smaller ecosystem
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- AWS, Azure
- Security tools
Support & Community
Responsive support and documentation.
#8 — Detectify Surface Monitoring
Short description: A platform focused on external attack surface monitoring with strong vulnerability detection capabilities.
Key Features
- Surface monitoring
- Vulnerability detection
- Asset discovery
- Automated alerts
- Analytics dashboards
Pros
- Strong detection capabilities
- Continuous monitoring
Cons
- Limited enterprise features
- Requires configuration
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Security tools and APIs
Support & Community
Good documentation and support.
#9 — UpGuard
Short description: A platform focused on external risk and vendor risk management alongside attack surface monitoring.
Key Features
- Attack surface monitoring
- Vendor risk management
- Risk scoring
- Continuous monitoring
- Reporting dashboards
Pros
- Strong third-party risk management
- Easy to use
Cons
- Limited advanced features
- Focused use case
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Security and compliance tools
Support & Community
Responsive support and onboarding.
#10 — SecurityScorecard
Short description: A platform that provides security ratings and visibility into external attack surfaces and third-party risks.
Key Features
- Security ratings
- Attack surface visibility
- Risk scoring
- Vendor risk monitoring
- Analytics dashboards
Pros
- Easy-to-understand ratings
- Strong vendor risk insights
Cons
- Limited deep technical analysis
- Focused on scoring
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Security tools and APIs
Support & Community
Enterprise support and documentation.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Cortex Xpanse | Enterprise | Web | Cloud | Real-time discovery | N/A |
| Randori Recon | Enterprise | Web | Cloud | Attacker view | N/A |
| CyCognito | Enterprise | Web | Cloud | Unknown asset discovery | N/A |
| Defender EASM | Enterprise | Web | Cloud | Microsoft integration | N/A |
| IBM Randori | Enterprise | Web | Cloud | Attack simulation | N/A |
| Mandiant ASM | Enterprise | Web | Cloud | Threat intelligence | N/A |
| Intruder | SMB | Web | Cloud | Ease of use | N/A |
| Detectify | SMB | Web | Cloud | Continuous monitoring | N/A |
| UpGuard | SMB/Enterprise | Web | Cloud | Vendor risk | N/A |
| SecurityScorecard | Enterprise | Web | Cloud | Security ratings | N/A |
Evaluation & Scoring of Attack Surface Management (ASM)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Cortex Xpanse | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Randori Recon | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
| CyCognito | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
| Defender EASM | 8 | 8 | 7 | 8 | 8 | 7 | 7 | 7.9 |
| IBM Randori | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
| Mandiant ASM | 9 | 7 | 7 | 8 | 9 | 8 | 7 | 8.1 |
| Intruder | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.3 |
| Detectify | 7 | 7 | 6 | 7 | 7 | 7 | 7 | 7.1 |
| UpGuard | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.3 |
| SecurityScorecard | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.3 |
Scores are comparative and reflect strengths across features, usability, integrations, and value. Higher scores indicate stronger enterprise readiness.
Which Attack Surface Management (ASM) Tool Is Right for You?
Solo / Freelancer
ASM tools are generally not required; basic monitoring tools are sufficient.
SMB
Intruder and Detectify provide easy deployment and essential features.
Mid-Market
CyCognito and Randori Recon offer balanced visibility and risk management.
Enterprise
Cortex Xpanse, Mandiant, and Microsoft Defender EASM provide advanced capabilities.
Budget vs Premium
Budget tools focus on monitoring; premium tools provide deeper insights and automation.
Feature Depth vs Ease of Use
Advanced tools require expertise; simpler tools enable faster adoption.
Integrations & Scalability
Ensure compatibility with your existing security stack.
Security & Compliance Needs
Select tools that align with compliance requirements.
Frequently Asked Questions (FAQs)
What is Attack Surface Management?
It is the process of discovering and monitoring all external digital assets to identify risks.
How does ASM differ from vulnerability scanning?
ASM focuses on asset discovery and exposure, while vulnerability scanning identifies specific weaknesses.
Is ASM necessary for small businesses?
It depends on external exposure and security requirements.
How often should ASM be performed?
Continuously, as new assets and risks emerge.
Can ASM tools integrate with other systems?
Yes, most integrate with SIEM, SOAR, and cloud platforms.
Do ASM tools provide real-time monitoring?
Yes, many platforms offer continuous monitoring and alerts.
What are common mistakes?
Ignoring shadow IT and failing to monitor external assets.
Are ASM tools secure?
Most include strong security features like MFA and encryption.
Can ASM scale with business growth?
Yes, these tools are designed for scalability.
What alternatives exist?
Alternatives include manual asset tracking and vulnerability scanning tools.
Conclusion
Attack Surface Management platforms are essential for modern cybersecurity strategies, providing continuous visibility into external assets and potential risks. They help organizations identify unknown exposures, reduce blind spots, and strengthen their overall security posture.
The right ASM tool depends on your organization’s size, complexity, and digital footprint. Enterprise organizations benefit from advanced platforms with deep analytics, while smaller teams should focus on ease of use and faster deployment.
It is important to evaluate asset discovery capabilities, integration support, and automation features before selecting a platform. Each tool offers unique strengths, and the best choice depends on your operational needs.
A practical approach is to shortlist a few tools, test them in real environments, and validate how well they align with your security workflows and infrastructure.