Introduction
Endpoint Detection & Response (EDR) is a cybersecurity solution designed to monitor, detect, investigate, and respond to suspicious activities across endpoints such as desktops, laptops, servers, and mobile devices. Unlike traditional antivirus software, EDR platforms provide real-time threat intelligence, automated responses, and forensic capabilities that empower organizations to proactively secure their digital assets.
EDR tools are critical for organizations aiming to maintain resilient security postures while ensuring business continuity.
Real-world use cases include:
- Detecting ransomware attempts before encryption spreads across the network
- Investigating suspicious user behavior on endpoints to prevent insider threats
- Rapidly isolating infected devices to minimize lateral movement
- Automating incident response workflows to reduce mean time to resolution
- Supporting compliance audits by tracking endpoint security activities
Key evaluation criteria for buyers:
- Threat detection capabilities (signature-based, behavioral, AI-driven)
- Response automation and orchestration
- Platform coverage (Windows, macOS, Linux, mobile)
- Cloud, on-premises, or hybrid deployment options
- Integration with SIEM, SOAR, and existing security stack
- Performance impact on endpoints
- Security and compliance certifications
- Ease of use and reporting dashboards
- Scalability and multi-tenant support
- Vendor support and community strength
Best for: IT security teams, SOC analysts, large enterprises, SMBs seeking robust endpoint visibility, and organizations needing regulatory compliance
Not ideal for: Solo users or small teams without complex endpoint environments; basic antivirus or cloud-native protection may suffice in low-risk scenarios
Key Trends in Endpoint Detection & Response (EDR)
- Increased adoption of AI and machine learning for predictive threat detection
- Integration with Extended Detection & Response (XDR) platforms for unified visibility
- Automated response and orchestration to reduce SOC workload
- Cloud-native deployments with hybrid endpoint coverage
- Enhanced behavioral analytics to detect insider threats and zero-day exploits
- Support for remote workforce and mobile endpoints
- Emphasis on compliance with SOC 2, ISO 27001, GDPR, and HIPAA
- Subscription-based pricing models for flexibility
- Interoperability with threat intelligence feeds and third-party APIs
- Lightweight agents with minimal endpoint performance impact
How We Selected These Tools (Methodology)
- Evaluated market adoption and presence across industries
- Assessed core EDR features including detection, response, and analytics
- Reviewed performance reliability signals from independent reports and user feedback
- Considered security posture, certifications, and compliance readiness
- Examined integrations with SIEM, SOAR, vulnerability management, and ITSM tools
- Analyzed customer fit across SMBs, mid-market, and enterprise environments
- Accounted for ease of deployment, agent footprint, and management dashboards
- Factored in vendor support, documentation, and community engagement
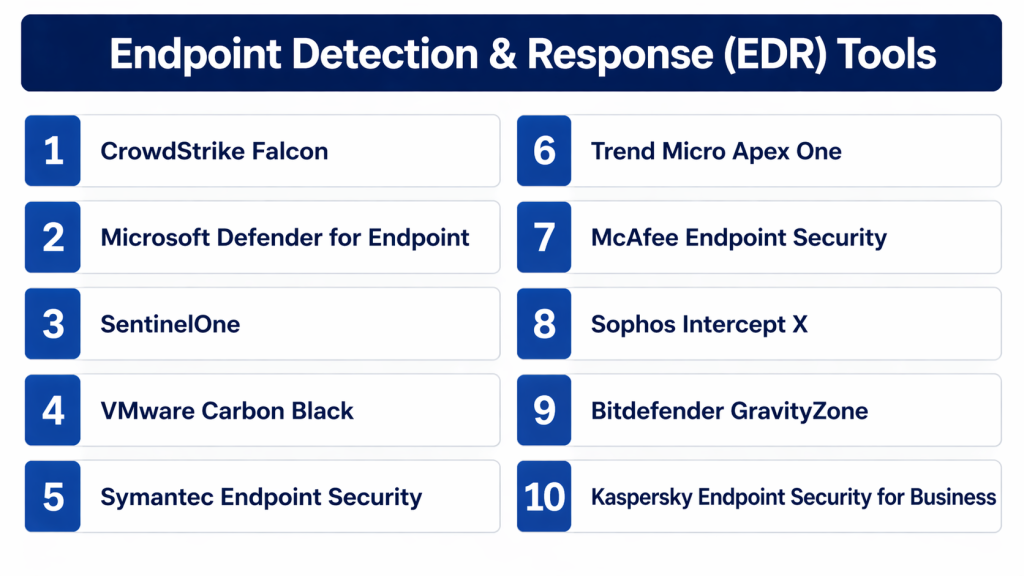
Top 10 Endpoint Detection & Response (EDR) Tools
#1 — CrowdStrike Falcon
Short description: Cloud-native EDR platform leveraging AI to detect threats across endpoints
Key Features
- Real-time threat intelligence and detection
- Behavioral analytics for unknown malware
- Automated threat response and quarantine
- Cloud-based management with zero on-premises infrastructure
- Lightweight agent with minimal performance impact
- Integration with SIEM and SOAR platforms
Pros
- Rapid deployment and scalable architecture
- Strong threat hunting and AI-driven analytics
Cons
- Premium pricing may deter SMB adoption
- Limited offline functionality for disconnected endpoints
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud
Security & Compliance
- SOC 2, ISO 27001
- SSO/SAML, MFA, RBAC, encryption
Integrations & Ecosystem
Integrates with SIEM, SOAR, ITSM, and vulnerability management platforms
- Splunk, ServiceNow, Microsoft Sentinel
- APIs for custom workflows
- Threat intelligence feed integration
Support & Community
Varies / Not publicly stated; extensive documentation and enterprise support tiers available
#2 — Microsoft Defender for Endpoint
Short description: Enterprise-focused EDR solution integrated with Microsoft 365 ecosystem
Key Features
- Endpoint behavioral sensors
- Automated investigation and remediation
- Threat analytics dashboard
- Integration with Microsoft security stack
- Vulnerability and configuration management
Pros
- Seamless integration with Windows devices and Azure
- Strong automation and investigation tools
Cons
- Limited support for non-Windows endpoints
- Some advanced features require higher licensing tiers
Platforms / Deployment
- Windows / macOS / Linux / iOS / Android
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, HIPAA, GDPR
- SSO/SAML, MFA, encryption
Integrations & Ecosystem
Integrates tightly with Microsoft 365, Azure Sentinel, and third-party SIEMs
- Azure Security Center
- Microsoft Graph API
- ServiceNow
Support & Community
Strong Microsoft support channels and community forums; documentation extensive
#3 — SentinelOne
Short description: Autonomous AI-driven EDR platform providing detection, prevention, and automated response
Key Features
- AI-powered static and behavioral analysis
- Automated remediation and rollback of affected endpoints
- Threat hunting and analytics
- Cloud and on-premises management
- Minimal agent footprint
Pros
- Rapid autonomous response
- Comprehensive endpoint coverage
Cons
- Some UI components may be complex for beginners
- Advanced analytics require higher-tier subscriptions
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- SSO/SAML, MFA, encryption
Integrations & Ecosystem
Supports SIEM, ITSM, and threat intelligence integrations
- Splunk, ServiceNow, Jira
- REST API for custom workflows
Support & Community
Documentation robust; 24/7 support and active community forums
#4 — VMware Carbon Black
Short description: Cloud-delivered EDR focusing on threat detection, behavioral analytics, and incident response
Key Features
- Continuous and centralized endpoint monitoring
- Behavioral threat detection
- Integration with VMware security ecosystem
- Automated containment and remediation
- Threat intelligence feed ingestion
Pros
- Strong analytics for complex attacks
- Flexible deployment options
Cons
- Can be resource-intensive on endpoints
- UI may require training for full utilization
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, RBAC, encryption
Integrations & Ecosystem
Integrates with SIEM, SOAR, and ITSM tools
- Splunk, ServiceNow, Elastic
- Carbon Black APIs
Support & Community
Enterprise-grade support and active community forums
#5 — Symantec Endpoint Security
Short description: EDR solution with advanced threat protection and centralized management
Key Features
- Malware and ransomware protection
- Behavioral analysis and threat detection
- Automated incident response
- Cloud and on-prem management
- Device control and firewall integration
Pros
- Well-known enterprise-grade solution
- Broad endpoint support
Cons
- Complexity in configuration
- Legacy interfaces in some modules
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
- SSO/SAML, encryption, RBAC
Integrations & Ecosystem
- SIEM integrations
- Broadcom API support
- ITSM connectivity
Support & Community
Robust enterprise support; extensive documentation and forums
#6 — Trend Micro Apex One
Short description: Unified endpoint security with EDR, AI threat detection, and automated remediation
Key Features
- Advanced threat detection and prevention
- Automated response workflows
- Centralized management console
- Behavioral and machine learning analytics
- Cloud and on-prem deployment flexibility
Pros
- Comprehensive threat protection
- Flexible deployment options
Cons
- May require tuning for optimal performance
- Reporting features are complex for beginners
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
- MFA, encryption, RBAC
Integrations & Ecosystem
- SIEM and ITSM integration
- APIs for automation
- Trend Micro threat intelligence feeds
Support & Community
Extensive documentation and enterprise support; moderate community presence
#7 — McAfee Endpoint Security
Short description: Enterprise EDR platform providing real-time threat detection, prevention, and automated remediation
Key Features
- Behavioral and signature-based detection
- Threat intelligence integration
- Automated remediation workflows
- Cloud-based management
- Endpoint firewall and device control
Pros
- Broad enterprise adoption
- Integrated threat intelligence
Cons
- Resource usage can affect endpoint performance
- User interface may be less intuitive
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, encryption, audit logs
Integrations & Ecosystem
- SIEM, ITSM, and threat intel feeds
- APIs for automation
- McAfee MVISION ecosystem
Support & Community
Varies; strong enterprise support and documentation
#8 — Sophos Intercept X
Short description: AI-powered endpoint protection with deep learning and threat prevention
Key Features
- Deep learning malware detection
- Ransomware protection with rollback
- Endpoint detection and response
- Exploit prevention and root cause analysis
- Cloud and on-prem management
Pros
- Strong AI-driven threat detection
- Minimal performance impact
Cons
- Reporting features can be complex
- Limited third-party integrations compared to competitors
Platforms / Deployment
- Windows / macOS / Linux / Android / iOS
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, encryption, RBAC
Integrations & Ecosystem
- SIEM integration
- Sophos Central API
- Threat intelligence feeds
Support & Community
Strong documentation and support; active community
#9 — Bitdefender GravityZone
Short description: Unified endpoint security platform combining AI-based EDR and advanced malware protection
Key Features
- AI-driven threat detection
- Endpoint risk analytics
- Automated remediation and isolation
- Cloud and on-prem management
- Minimal system footprint
Pros
- High detection accuracy
- Lightweight agents
Cons
- User interface may require training
- Integrations with third-party SIEMs limited
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, encryption
Integrations & Ecosystem
- APIs for custom workflows
- SIEM integrations
- Threat intelligence feeds
Support & Community
Enterprise support available; documentation robust
#10 — Kaspersky Endpoint Security for Business
Short description: EDR solution combining advanced threat detection and behavior analytics
Key Features
- Behavioral monitoring and analysis
- Automated threat response
- Ransomware protection
- Centralized management console
- Integration with SIEM and IT management tools
Pros
- Strong malware detection capabilities
- Detailed reporting and analytics
Cons
- Some regional deployment restrictions
- May require training for advanced features
Platforms / Deployment
- Windows / macOS / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- MFA, encryption, RBAC
Integrations & Ecosystem
- SIEM and ITSM integrations
- APIs for automation
- Threat intelligence feed support
Support & Community
Documentation comprehensive; enterprise support available
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| CrowdStrike Falcon | Enterprise / Mid-market | Windows, macOS, Linux, iOS, Android | Cloud | AI-powered threat detection | N/A |
| Microsoft Defender for Endpoint | Windows-heavy enterprises | Windows, macOS, Linux, iOS, Android | Cloud / Hybrid | Seamless Microsoft integration | N/A |
| SentinelOne | Autonomous AI-driven EDR | Windows, macOS, Linux | Cloud / Hybrid | Automated response | N/A |
| VMware Carbon Black | Enterprise / mid-market | Windows, macOS, Linux | Cloud / Hybrid | Behavioral analytics | N/A |
| Symantec Endpoint Security | Large enterprise | Windows, macOS, Linux | Cloud / Hybrid | Threat protection & device control | N/A |
| Trend Micro Apex One | Enterprise / SMB | Windows, macOS, Linux | Cloud / Hybrid | Machine learning detection | N/A |
| McAfee Endpoint Security | Enterprise | Windows, macOS, Linux | Cloud / Hybrid | Threat intelligence integration | N/A |
| Sophos Intercept X | AI-driven EDR | Windows, macOS, Linux, iOS, Android | Cloud / Hybrid | Deep learning malware detection | N/A |
| Bitdefender GravityZone | SMB / Mid-market | Windows, macOS, Linux | Cloud / Hybrid | Lightweight AI agents | N/A |
| Kaspersky Endpoint Security | Enterprise / SMB | Windows, macOS, Linux | Cloud / Hybrid | Threat intelligence + analytics | N/A |
Conclusion
Endpoint Detection & Response (EDR) is essential for modern cybersecurity, enabling organizations to detect, investigate, and respond to threats across all endpoints. AI-driven analytics, automated remediation, and cross-platform coverage allow IT teams to reduce risks, ensure compliance, and maintain operational continuity. The right EDR solution depends on organizational size, endpoint diversity, integration requirements, and compliance needs. Enterprises benefit from robust AI and automation features, while SMBs may prioritize cost-effective, easy-to-deploy solutions. A pilot test of two to three tools can help validate performance, integrations, and usability. By aligning EDR capabilities with business objectives, organizations can enhance security posture while optimizing efficiency. Ultimately, choosing the right tool is context-driven, reflecting specific security needs, risk tolerance, and available resources.