Introduction
Identity & Access Management (IAM) platforms are security systems that control how users, devices, and applications authenticate and access digital resources. In simple terms, IAM ensures the right people get the right access to the right systems at the right time.
In modern enterprise environments, where users work across cloud applications, remote networks, and multiple devices, IAM has become a critical security foundation. It reduces the risk of unauthorized access, improves compliance, and strengthens overall cybersecurity posture.
IAM solutions are widely used to:
- Manage user identities across systems
- Control access to applications and data
- Enable Single Sign-On (SSO) across platforms
- Enforce Multi-Factor Authentication (MFA)
- Automate user provisioning and deprovisioning
- Support Zero Trust security models
Key evaluation criteria
Organizations typically evaluate:
- Authentication methods (SSO, MFA, passwordless)
- User lifecycle management (provisioning/deprovisioning)
- Directory integration capabilities
- Security policies and access controls
- Scalability for enterprise environments
- Integration with cloud and on-prem apps
- Compliance support (ISO, SOC, GDPR, etc.)
- Ease of deployment and administration
- API and automation support
- Reporting and audit capabilities
Best for:
IAM platforms are best for enterprises, SaaS companies, government organizations, and any business managing multiple users, applications, or sensitive data systems.
Not ideal for:
They may not be necessary for very small teams or standalone applications with minimal user management needs.
Key Trends in Identity & Access Management
- Shift toward passwordless authentication systems
- Strong adoption of Zero Trust Identity models
- AI-based risk-based authentication decisions
- Growth of decentralized identity systems
- Integration with cloud-native and hybrid environments
- Increased use of adaptive MFA (context-aware security)
- Identity governance automation and compliance tracking
- API-first IAM architectures
- Rise of identity-as-a-service (IDaaS) platforms
- Expansion of machine identity and workload identity management
How We Selected These Tools (Methodology)
- Global enterprise adoption and market presence
- Strength of authentication and authorization capabilities
- Support for modern security models (Zero Trust, MFA, SSO)
- Integration ecosystem maturity
- Cloud and hybrid deployment flexibility
- Compliance readiness and audit capabilities
- Automation and identity lifecycle management
- Scalability for large organizations
- Vendor reliability and platform maturity
- Real-world enterprise usage performance
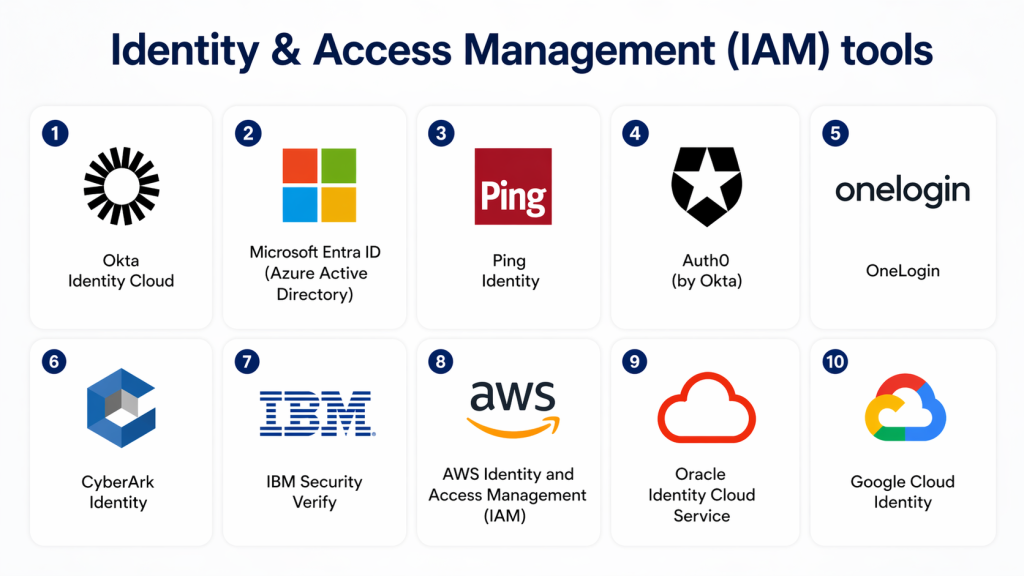
Top 10 Identity & Access Management (IAM) Platforms
1 — Okta Identity Cloud
Short description:
Okta is one of the most widely used IAM platforms, providing secure identity management, SSO, and MFA for cloud and enterprise applications.
Key Features
- Single Sign-On (SSO) across applications
- Multi-Factor Authentication (MFA)
- User lifecycle management
- Adaptive authentication
- API access management
- Identity federation
- Universal directory integration
Pros
- Strong cloud-native architecture
- Easy integration with SaaS apps
- Highly scalable
Cons
- Premium pricing
- Advanced customization requires expertise
Platforms / Deployment
- Cloud
Security & Compliance
- SOC 2 support
- MFA and encryption
- Audit logs and RBAC
Integrations & Ecosystem
- SaaS applications
- Cloud providers
- API gateways
- Security tools
Support & Community
Strong global enterprise support and developer ecosystem.
2 — Microsoft Entra ID (Azure Active Directory)
Short description:
Microsoft Entra ID provides identity management and access control deeply integrated into Microsoft ecosystems.
Key Features
- SSO across Microsoft and third-party apps
- Conditional access policies
- MFA and passwordless authentication
- Identity protection and risk detection
- Device-based access control
- User lifecycle management
- Hybrid identity support
Pros
- Deep Microsoft ecosystem integration
- Strong enterprise adoption
- Advanced security controls
Cons
- Complex for non-Microsoft environments
- Licensing complexity
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Enterprise-grade security controls
- Conditional access policies
- Audit and compliance reporting
Integrations & Ecosystem
- Microsoft 365
- Azure services
- Enterprise SaaS apps
- Security tools
Support & Community
Strong enterprise support from Microsoft ecosystem.
3 — Ping Identity
Short description:
Ping Identity provides flexible identity management solutions focused on enterprise-grade authentication and federation.
Key Features
- SSO and MFA support
- Identity federation
- API security and access control
- Adaptive authentication
- Directory integration
- Zero Trust identity support
- Identity orchestration
Pros
- Strong enterprise flexibility
- Good hybrid identity support
- Advanced authentication options
Cons
- Complex setup for beginners
- Higher enterprise cost
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- MFA and encryption
- Audit logs
- Compliance support
Integrations & Ecosystem
- Enterprise applications
- Cloud platforms
- API systems
- Security tools
Support & Community
Strong enterprise-focused support.
4 — Auth0 (by Okta)
Short description:
Auth0 is a developer-focused IAM platform that simplifies authentication and authorization for applications.
Key Features
- Authentication as a service
- SSO and MFA
- Social login integration
- Custom login flows
- API authentication
- Role-based access control
- Passwordless login
Pros
- Developer-friendly
- Fast integration
- Flexible authentication options
Cons
- Can become costly at scale
- Requires technical setup for customization
Platforms / Deployment
- Cloud
Security & Compliance
- Encryption and MFA
- SOC 2 compliance
- Secure token management
Integrations & Ecosystem
- Web and mobile apps
- APIs
- Cloud services
- Developer frameworks
Support & Community
Strong developer documentation and community support.
5 — OneLogin
Short description:
OneLogin provides cloud-based IAM solutions focused on simplifying access management and improving enterprise security.
Key Features
- SSO across applications
- MFA support
- Smart password management
- User provisioning automation
- Directory integration
- Risk-based authentication
- Cloud directory service
Pros
- Easy deployment
- Strong SSO capabilities
- Good SMB to mid-market fit
Cons
- Limited advanced enterprise customization
- Smaller ecosystem compared to competitors
Platforms / Deployment
- Cloud
Security & Compliance
- MFA and encryption
- Audit logs
- Compliance reporting
Integrations & Ecosystem
- SaaS applications
- Cloud platforms
- HR systems
- APIs
Support & Community
Good mid-market support coverage.
6 — CyberArk Identity
Short description:
CyberArk Identity focuses on privileged access management and secure identity governance for enterprises.
Key Features
- Privileged access control
- MFA and SSO
- Identity lifecycle management
- Adaptive authentication
- Secure password vaulting
- Session monitoring
- Access policy enforcement
Pros
- Strong privileged access security
- Enterprise-grade protection
- Excellent compliance support
Cons
- Complex implementation
- High cost for smaller organizations
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Strong compliance controls
- Encryption and RBAC
- Audit trails
Integrations & Ecosystem
- Security platforms
- Enterprise directories
- Cloud systems
- SIEM tools
Support & Community
Strong enterprise security support.
7 — IBM Security Verify
Short description:
IBM Security Verify provides identity governance, authentication, and access management for large enterprises.
Key Features
- SSO and MFA
- Identity governance and lifecycle management
- Risk-based authentication
- Access intelligence analytics
- Directory integration
- API security support
- User provisioning automation
Pros
- Strong enterprise identity governance
- Advanced analytics
- Scalable architecture
Cons
- Complex configuration
- Enterprise-focused pricing
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC and audit logs
- Encryption
- Compliance reporting
Integrations & Ecosystem
- IBM security suite
- Cloud platforms
- Enterprise applications
- API systems
Support & Community
Strong enterprise IBM support ecosystem.
8 — AWS IAM
Short description:
AWS Identity and Access Management provides fine-grained access control for AWS resources.
Key Features
- Granular permission policies
- Role-based access control
- Temporary credentials
- Multi-account access management
- Integration with AWS services
- Identity federation support
- Access auditing tools
Pros
- Deep AWS integration
- Highly granular control
- Scalable for cloud workloads
Cons
- AWS-specific usage
- Complex policy structure
Platforms / Deployment
- Cloud (AWS)
Security & Compliance
- IAM policies
- Encryption support
- Audit logging
Integrations & Ecosystem
- AWS services
- Cloud-native apps
- DevOps pipelines
- Security tools
Support & Community
Strong AWS documentation and support.
9 — Oracle Identity Cloud Service
Short description:
Oracle Identity Cloud Service provides enterprise identity management and access control for Oracle ecosystems.
Key Features
- SSO and MFA
- Identity lifecycle management
- User provisioning automation
- Role-based access control
- Adaptive authentication
- API security
- Directory integration
Pros
- Strong Oracle ecosystem integration
- Enterprise-grade security
- Good scalability
Cons
- Best within Oracle environments
- Complex configuration
Platforms / Deployment
- Cloud
Security & Compliance
- Encryption and RBAC
- Audit logs
- Compliance support
Integrations & Ecosystem
- Oracle applications
- Enterprise SaaS tools
- Cloud systems
- APIs
Support & Community
Strong enterprise support.
10 — Google Cloud Identity
Short description:
Google Cloud Identity provides identity management and access control for Google Cloud environments and enterprise applications.
Key Features
- SSO and MFA
- Device management
- Access control policies
- User lifecycle management
- Directory synchronization
- Security monitoring
- Conditional access
Pros
- Strong Google ecosystem integration
- Easy cloud deployment
- Good scalability
Cons
- Google Cloud dependency
- Limited advanced enterprise customization
Platforms / Deployment
- Cloud
Security & Compliance
- IAM-based security
- Encryption
- Audit logs
Integrations & Ecosystem
- Google Workspace
- Cloud platforms
- SaaS applications
- API systems
Support & Community
Strong Google cloud support ecosystem.
Comparison Table (Top 10)
| Tool | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Okta | Enterprise SaaS IAM | Cloud | Cloud | Strong SSO ecosystem | N/A |
| Microsoft Entra ID | Microsoft ecosystems | Multi | Hybrid | Conditional access | N/A |
| Ping Identity | Enterprises | Multi | Hybrid | Identity orchestration | N/A |
| Auth0 | Developers | Multi | Cloud | Developer-first IAM | N/A |
| OneLogin | SMB & mid-market | Cloud | Cloud | Simple SSO setup | N/A |
| CyberArk | Privileged access | Multi | Hybrid | PAM security | N/A |
| IBM Verify | Large enterprises | Multi | Hybrid | Identity governance | N/A |
| AWS IAM | AWS users | AWS | Cloud | Fine-grained permissions | N/A |
| Oracle Identity | Oracle ecosystems | Cloud | Cloud | Enterprise identity control | N/A |
| Google Cloud Identity | Google ecosystems | Cloud | Cloud | Device + identity control | N/A |
Evaluation & Scoring of IAM Platforms
| Tool | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Total |
|---|---|---|---|---|---|---|---|---|
| Okta | 9 | 9 | 10 | 10 | 9 | 9 | 8 | 9.1 |
| Entra ID | 9 | 7 | 10 | 10 | 9 | 9 | 9 | 8.9 |
| Ping | 9 | 7 | 9 | 10 | 9 | 8 | 7 | 8.4 |
| Auth0 | 9 | 9 | 9 | 9 | 9 | 8 | 8 | 8.7 |
| OneLogin | 8 | 9 | 8 | 9 | 8 | 8 | 9 | 8.4 |
| CyberArk | 10 | 6 | 9 | 10 | 9 | 9 | 7 | 8.6 |
| IBM Verify | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.6 |
| AWS IAM | 9 | 6 | 10 | 10 | 9 | 8 | 9 | 8.5 |
| Oracle IAM | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 7.9 |
| Google Cloud Identity | 8 | 8 | 9 | 9 | 8 | 8 | 9 | 8.4 |
Which IAM Platform Is Right for You?
SMB / Startups
- Auth0
- OneLogin
- Google Cloud Identity
Mid-Market
- Okta
- Ping Identity
- AWS IAM
Enterprise
- Microsoft Entra ID
- CyberArk
- IBM Security Verify
- Oracle Identity
Frequently Asked Questions (FAQs)
1. What is IAM?
IAM stands for Identity & Access Management. It controls user access to systems and applications. It ensures secure authentication and authorization.
2. Why is IAM important?
It reduces unauthorized access risks and strengthens security. It is essential for cloud and enterprise environments.
3. What is SSO in IAM?
Single Sign-On allows users to access multiple applications using one login. It improves usability and security.
4. What is MFA?
Multi-Factor Authentication adds extra security layers beyond passwords. It reduces account compromise risks.
5. Is IAM cloud-based?
Most modern IAM solutions are cloud-based or hybrid. Cloud IAM is widely adopted today.
6. Can IAM manage APIs?
Yes, many IAM platforms support API authentication and access control.
7. What is Zero Trust in IAM?
Zero Trust means no user is trusted by default. Every access request is verified.
8. Is IAM difficult to implement?
Enterprise IAM can be complex. SMB solutions are easier to deploy.
9. What industries use IAM most?
Finance, healthcare, SaaS, government, and large enterprises use IAM extensively.
10. Can IAM prevent cyber attacks?
IAM reduces attack risks but does not replace full cybersecurity systems. It is a foundational layer.
Conclusion
Identity & Access Management platforms are a critical foundation of modern cybersecurity. They ensure secure, controlled, and scalable access to applications, systems, and data across cloud and enterprise environments.
From developer-friendly tools like Auth0 to enterprise leaders like Okta, Microsoft Entra ID, and CyberArk, each IAM platform serves different levels of complexity and organizational needs.
The right choice depends on your ecosystem, security requirements, and scalability goals. A strong IAM strategy ensures secure identity control, reduced risk, and seamless user access across all digital environments.