Introduction
DDoS Protection Tools are cybersecurity solutions designed to detect, mitigate, and block Distributed Denial of Service (DDoS) attacks. These attacks attempt to overwhelm a target application, server, or network with massive traffic from multiple sources, making services slow or completely unavailable.
In modern digital environments, DDoS attacks are becoming more frequent, larger in scale, and more sophisticated. Attackers now use botnets, IoT devices, and multi-vector strategies to bypass traditional defenses. Because of this, organizations need advanced DDoS protection systems that can respond in real time and absorb massive traffic spikes without disrupting legitimate users.
These tools are widely used to:
- Protect websites and APIs from traffic overload attacks
- Ensure uptime for critical applications and services
- Detect abnormal traffic patterns using AI/ML
- Provide global traffic scrubbing and mitigation
- Secure cloud, hybrid, and on-prem infrastructure
- Prevent downtime-related financial losses
Key evaluation criteria
When choosing a DDoS protection tool, organizations typically consider:
- Layer 3, 4, and 7 attack mitigation capabilities
- Real-time traffic monitoring and detection speed
- Global network capacity and scrubbing centers
- Integration with cloud platforms and CDNs
- Automation and AI-based threat detection
- Latency impact on legitimate traffic
- Scalability during large attack spikes
- API and DevOps integration support
- Reporting and forensic analysis tools
- Ease of deployment and management
Best for:
DDoS protection tools are best for enterprises, SaaS platforms, fintech companies, e-commerce platforms, gaming services, and any internet-facing application requiring high availability.
Not ideal for:
They are less necessary for offline systems or internal applications that are not exposed to the internet.
Key Trends in DDoS Protection Tools
- Increasing use of AI-driven anomaly detection systems
- Growth of cloud-based scrubbing networks for large-scale mitigation
- Rise in multi-vector and application-layer (Layer 7) attacks
- Integration with Zero Trust security frameworks
- Edge-based DDoS mitigation through CDN platforms
- Automated attack response and traffic rerouting
- Improved protection for APIs and microservices
- Hybrid protection models (cloud + on-prem)
- Real-time threat intelligence sharing between networks
- Focus on low-latency mitigation without user impact
How We Selected These Tools (Methodology)
The tools in this list were selected based on:
- Global adoption and enterprise usage
- Ability to mitigate large-scale volumetric attacks
- Layer 7 application security capabilities
- Cloud-native and hybrid deployment support
- Performance under real attack conditions
- Integration with security ecosystems (SIEM, CDN, cloud)
- Scalability across global traffic loads
- Automation and AI-driven detection capabilities
- Vendor reliability and infrastructure maturity
- Real-world protection effectiveness
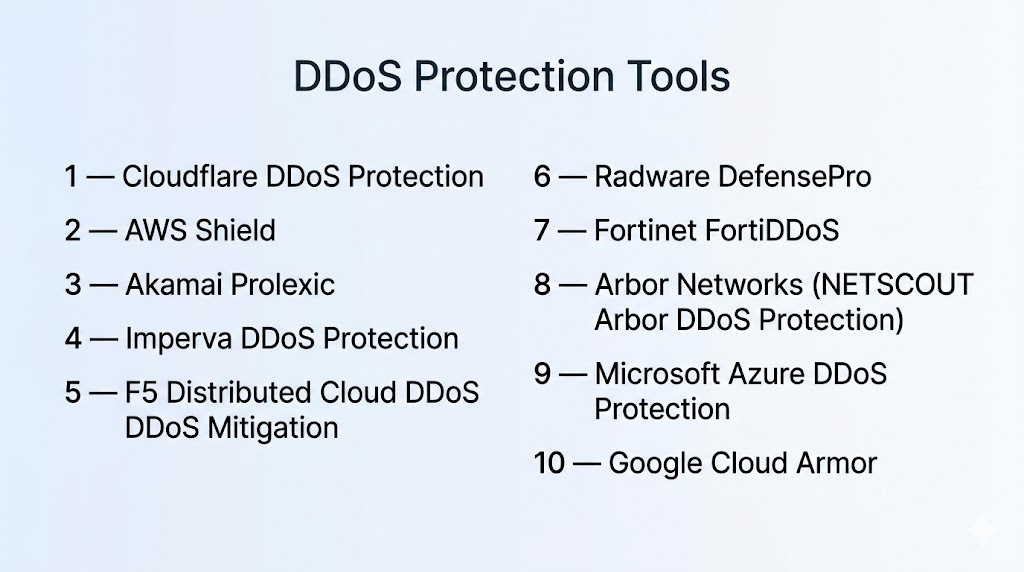
Top 10 DDoS Protection Tools
1 — Cloudflare DDoS Protection
Short description:
Cloudflare provides one of the largest global DDoS protection networks, offering always-on mitigation at the edge with minimal latency impact.
Key Features
- Global edge-based mitigation network
- Layer 3, 4, and 7 attack protection
- Always-on DDoS filtering
- Real-time traffic analysis
- Bot mitigation and rate limiting
- CDN-based traffic absorption
- API protection capabilities
Pros
- Extremely large global network
- Fast mitigation with minimal latency impact
- Easy deployment via DNS
Cons
- Advanced features require higher plans
- Limited deep customization in basic tiers
Platforms / Deployment
- Cloud / Edge
Security & Compliance
- Encryption in transit
- Traffic logging and analytics
- RBAC support (varies by plan)
Integrations & Ecosystem
- CDN and performance tools
- SIEM platforms
- API-based integrations
- Cloud providers
Support & Community
Strong global support and extensive user community.
2 — AWS Shield
Short description:
AWS Shield is a managed DDoS protection service designed for applications running on AWS infrastructure.
Key Features
- Always-on detection and mitigation
- Layer 3, 4, and 7 protection
- Integration with AWS services
- Real-time attack visibility
- Automatic mitigation for common attacks
- Advanced threat detection (premium tier)
- Cloud-native scalability
Pros
- Seamless AWS ecosystem integration
- Highly scalable protection
- Minimal configuration required
Cons
- Limited outside AWS ecosystem
- Advanced features require premium tier
Platforms / Deployment
- Cloud (AWS)
Security & Compliance
- IAM-based access control
- Encryption support
- Logging via AWS monitoring tools
Integrations & Ecosystem
- CloudFront
- Elastic Load Balancing
- API Gateway
- Security Hub
Support & Community
Strong AWS documentation and enterprise support.
3 — Akamai Prolexic
Short description:
Akamai Prolexic provides enterprise-grade DDoS protection using one of the largest global scrubbing networks.
Key Features
- Global traffic scrubbing network
- Layer 3–7 DDoS mitigation
- Real-time attack detection
- Hybrid deployment support
- Advanced threat intelligence
- Traffic rerouting mechanisms
- Application-layer protection
Pros
- Massive global mitigation capacity
- Excellent for enterprise-scale attacks
- Strong reliability
Cons
- Premium pricing model
- Complex configuration
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Enterprise-grade compliance support
- Encryption and monitoring
- Detailed forensic reporting
Integrations & Ecosystem
- CDN services
- Cloud providers
- SIEM tools
- API integrations
Support & Community
Strong enterprise-level support.
4 — Imperva DDoS Protection
Short description:
Imperva offers integrated DDoS protection with strong application-layer security and global mitigation capacity.
Key Features
- Layer 3–7 attack mitigation
- Always-on DDoS protection
- Bot mitigation system
- API protection
- Global scrubbing centers
- Real-time traffic analysis
- Security dashboards
Pros
- Strong application-layer defense
- High reliability for enterprise apps
- Integrated security ecosystem
Cons
- Higher cost structure
- Requires onboarding effort
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- PCI DSS support
- RBAC and audit logs
- Encryption support
Integrations & Ecosystem
- SIEM tools
- Cloud platforms
- API gateways
- Security orchestration tools
Support & Community
Enterprise-focused support services.
5 — F5 Distributed Cloud DDoS Mitigation
Short description:
F5 provides distributed cloud-based DDoS protection with strong application security capabilities.
Key Features
- Global distributed mitigation network
- Layer 7 attack protection
- API security controls
- Traffic anomaly detection
- Multi-cloud protection
- Adaptive security policies
- Real-time monitoring
Pros
- Strong enterprise security integration
- Good multi-cloud support
- Advanced application-layer defense
Cons
- Complex configuration
- Enterprise-focused pricing
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC and logging
- Encryption support
- Compliance reporting
Integrations & Ecosystem
- Cloud platforms
- SIEM systems
- DevOps tools
- API gateways
Support & Community
Strong enterprise support ecosystem.
6 — Radware DefensePro
Short description:
Radware DefensePro provides real-time DDoS protection using behavioral-based detection and mitigation.
Key Features
- Behavioral attack detection
- Layer 3–7 protection
- Automatic mitigation
- Real-time traffic analysis
- Bot detection
- Application security controls
- Threat intelligence integration
Pros
- Strong real-time protection
- Effective behavioral analysis
- Good enterprise fit
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
- On-prem / Cloud / Hybrid
Security & Compliance
- Compliance support
- Encryption and RBAC
- Audit logs
Integrations & Ecosystem
- SIEM platforms
- Cloud environments
- Security tools
- APIs
Support & Community
Enterprise-grade vendor support.
7 — Fortinet FortiDDoS
Short description:
FortiDDoS provides high-performance DDoS protection integrated into the Fortinet security ecosystem.
Key Features
- Hardware-accelerated mitigation
- Layer 3–7 attack protection
- Real-time anomaly detection
- Automated response system
- Traffic baseline analysis
- High-throughput protection
- Security analytics dashboard
Pros
- High performance hardware support
- Strong Fortinet integration
- Effective volumetric attack mitigation
Cons
- Best within Fortinet ecosystem
- Hardware dependency
Platforms / Deployment
- On-prem / Hybrid
Security & Compliance
- RBAC and logging
- Encryption support
- Compliance reporting
Integrations & Ecosystem
- Fortinet security products
- SIEM tools
- Cloud integrations
- APIs
Support & Community
Strong enterprise vendor support.
8 — NETSCOUT Arbor DDoS Protection
Short description:
NETSCOUT Arbor provides large-scale DDoS mitigation with deep network visibility and analytics.
Key Features
- Advanced traffic analysis
- Real-time DDoS mitigation
- Layer 3–7 protection
- Threat intelligence integration
- Behavioral anomaly detection
- Global scrubbing capabilities
- Reporting dashboards
Pros
- Strong network visibility
- High-scale mitigation capability
- Trusted enterprise solution
Cons
- Complex deployment
- Enterprise pricing
Platforms / Deployment
- On-prem / Cloud / Hybrid
Security & Compliance
- Audit logging
- RBAC support
- Encryption capabilities
Integrations & Ecosystem
- SIEM platforms
- Network infrastructure tools
- Cloud systems
- APIs
Support & Community
Strong enterprise-level support.
9 — Microsoft Azure DDoS Protection
Short description:
Azure DDoS Protection secures Azure-hosted applications from distributed attacks with built-in cloud scalability.
Key Features
- Always-on traffic protection
- Layer 3–7 mitigation
- Automatic attack detection
- Integration with Azure services
- Real-time analytics
- Adaptive tuning
- Attack reporting dashboards
Pros
- Native Azure integration
- Easy deployment for cloud apps
- Scalable infrastructure
Cons
- Azure-only dependency
- Limited cross-cloud flexibility
Platforms / Deployment
- Cloud (Azure)
Security & Compliance
- Azure security framework
- RBAC and IAM
- Encryption support
Integrations & Ecosystem
- Azure services
- SIEM tools
- DevOps pipelines
- Monitoring systems
Support & Community
Strong Microsoft enterprise support.
10 — Google Cloud Armor
Short description:
Google Cloud Armor provides DDoS protection for applications running on Google Cloud infrastructure.
Key Features
- Layer 3–7 DDoS protection
- Global edge security
- IP-based filtering
- Adaptive protection policies
- Traffic inspection
- Load balancing integration
- Real-time monitoring
Pros
- Strong Google Cloud integration
- High scalability
- Low latency protection
Cons
- Google Cloud dependency
- Requires configuration knowledge
Platforms / Deployment
- Cloud (Google Cloud)
Security & Compliance
- IAM-based security
- Encryption support
- Logging and monitoring
Integrations & Ecosystem
- Google Cloud services
- Load balancing systems
- SIEM tools
- API integrations
Support & Community
Strong cloud documentation and enterprise support.
Comparison Table (Top 10)
| Tool | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Cloudflare | Global web apps | Cloud | Edge | Global mitigation network | N/A |
| AWS Shield | AWS apps | AWS | Cloud | Native AWS integration | N/A |
| Akamai Prolexic | Enterprises | Cloud | Hybrid | Massive scrubbing network | N/A |
| Imperva | Enterprise apps | Multi | Hybrid | Application security focus | N/A |
| F5 | Multi-cloud enterprises | Multi | Hybrid | App-layer protection | N/A |
| Radware | Enterprise networks | Multi | Hybrid | Behavioral detection | N/A |
| Fortinet | Security ecosystems | Multi | Hybrid | Hardware acceleration | N/A |
| NETSCOUT Arbor | Large enterprises | Multi | Hybrid | Deep traffic visibility | N/A |
| Azure DDoS | Azure apps | Azure | Cloud | Native cloud protection | N/A |
| Google Cloud Armor | GCP apps | GCP | Cloud | Edge-based protection | N/A |
Evaluation & Scoring of DDoS Protection Tools
| Tool | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Total |
|---|---|---|---|---|---|---|---|---|
| Cloudflare | 10 | 9 | 9 | 9 | 10 | 9 | 9 | 9.4 |
| AWS Shield | 9 | 8 | 9 | 9 | 9 | 8 | 8 | 8.6 |
| Akamai | 10 | 7 | 9 | 10 | 10 | 9 | 6 | 8.8 |
| Imperva | 9 | 7 | 8 | 10 | 9 | 9 | 7 | 8.5 |
| F5 | 9 | 6 | 9 | 10 | 9 | 9 | 7 | 8.4 |
| Radware | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.2 |
| Fortinet | 8 | 7 | 8 | 9 | 9 | 8 | 8 | 8.1 |
| NETSCOUT | 9 | 6 | 8 | 9 | 9 | 9 | 7 | 8.3 |
| Azure DDoS | 8 | 8 | 9 | 9 | 9 | 8 | 8 | 8.4 |
| Google Cloud Armor | 8 | 8 | 9 | 9 | 9 | 8 | 8 | 8.4 |
Which DDoS Protection Tool Is Right for You?
SMB / Startups
- Cloudflare
- Sucuri (if website-focused)
- AWS Shield (light usage)
Mid-Market
- Fortinet FortiDDoS
- Radware
- Azure DDoS Protection
Enterprise
- Akamai Prolexic
- Imperva
- F5 Distributed Cloud
- NETSCOUT Arbor
Frequently Asked Questions (FAQs)
1. What is a DDoS attack?
A DDoS attack floods a system with traffic from multiple sources to make it unavailable. It targets websites, APIs, and servers. The goal is to disrupt normal operations.
2. How do DDoS protection tools work?
They detect abnormal traffic patterns and filter malicious requests. They use scrubbing centers and AI-based detection. They ensure legitimate users can still access services.
3. Do small businesses need DDoS protection?
Not always, but any internet-facing business is at risk. Even small websites can be attacked. Basic protection is recommended.
4. What layers do DDoS tools protect?
They protect Layer 3 (network), Layer 4 (transport), and Layer 7 (application). Modern tools cover all three layers.
5. Can DDoS protection stop all attacks?
No system is 100% immune, but modern tools can mitigate most attacks effectively. Large-scale enterprise tools handle massive traffic spikes.
6. Are cloud-based DDoS tools better?
Cloud-based tools offer scalability and global coverage. They are easier to deploy. Many organizations prefer them today.
7. Do DDoS tools affect website speed?
Most modern tools use edge networks that reduce latency. Some can even improve performance using CDNs.
8. Can DDoS tools protect APIs?
Yes, modern platforms include API-level protection. This is important for SaaS and microservices.
9. What is the biggest mistake in DDoS protection?
Not configuring proper thresholds and policies. Poor tuning can lead to false positives or missed attacks.
10. Are DDoS tools expensive?
Costs vary widely based on traffic volume and features. Enterprise-grade tools are more expensive. Cloud-based models offer flexible pricing.
Conclusion
DDoS Protection Tools are essential in today’s hyper-connected digital environment where downtime can result in financial loss, reputational damage, and service disruption. These tools provide a critical defense layer against large-scale traffic attacks that target availability.
From cloud-native solutions like Cloudflare and AWS Shield to enterprise-grade platforms like Akamai, Imperva, and F5, organizations have a wide range of options depending on scale and complexity.