Introduction
Cloud Workload Protection Platforms (CWPP) are cybersecurity solutions designed to protect workloads running in cloud environments, including virtual machines, containers, and serverless functions. These platforms continuously monitor, detect, and respond to threats across hybrid and multi-cloud infrastructures.
As organizations increasingly rely on cloud-native applications, workloads become dynamic, distributed, and harder to secure. CWPP tools provide real-time visibility, vulnerability detection, runtime protection, and policy enforcement to ensure workloads remain secure throughout their lifecycle.
Use Cases:
- Protecting virtual machines, containers, and serverless workloads
- Detecting runtime threats and anomalies
- Managing vulnerabilities in cloud workloads
- Enforcing security policies across environments
- Supporting compliance and cloud governance
What buyers should evaluate:
- Multi-cloud and hybrid support
- Runtime protection and threat detection
- Vulnerability management capabilities
- Integration with DevSecOps pipelines
- Ease of deployment (agent vs agentless)
- Automation and remediation features
- Performance and scalability
- Security and compliance capabilities
Best for: Cloud security teams, DevSecOps engineers, enterprises managing multi-cloud environments, and organizations running containerized or serverless workloads.
Not ideal for: Organizations with minimal cloud usage or those relying solely on traditional endpoint security tools.
Key Trends in Cloud Workload Protection Platforms (CWPP)
- Shift toward unified platforms combining CSPM + CWPP (CNAPP)
- Increased adoption of agentless scanning technologies
- AI-driven threat detection and anomaly analysis
- Expansion into container and Kubernetes security
- Integration with DevSecOps and CI/CD pipelines
- Real-time runtime protection and behavior monitoring
- Identity and access risk analysis within workloads
- Automation of remediation workflows
- Multi-cloud and hybrid environment support
- Focus on workload lifecycle security (build → runtime)
How We Selected These Tools (Methodology)
- Market adoption and industry recognition
- Depth of workload protection capabilities
- Runtime security and threat detection strength
- Integration ecosystem and API support
- Security and compliance readiness
- Multi-cloud compatibility
- Ease of deployment and usability
- Scalability across environments
- Innovation in automation and analytics
- Support quality and documentation
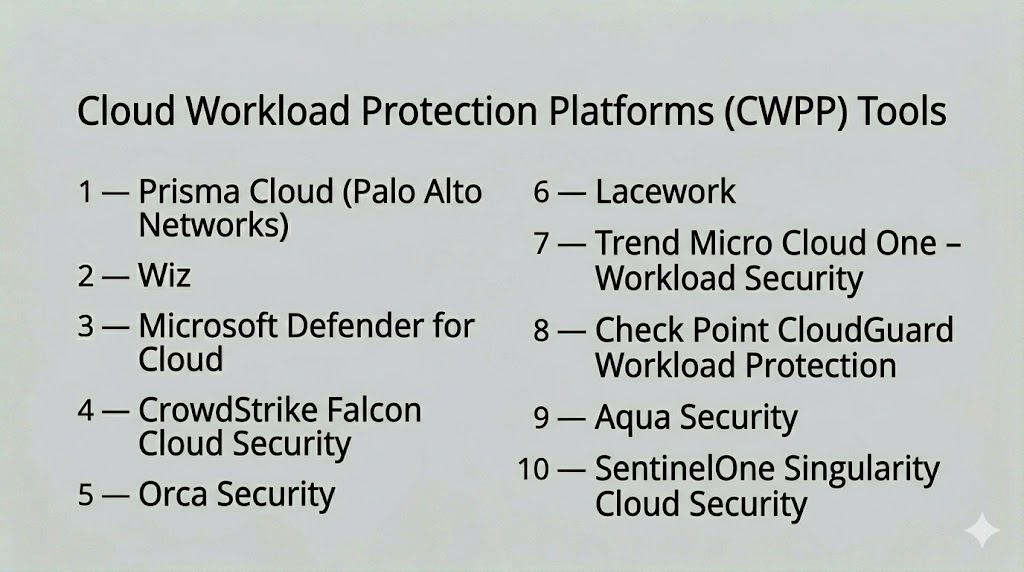
Top 10 Cloud Workload Protection Platforms (CWPP) Tools
#1 — Prisma Cloud (Palo Alto Networks)
Short description: A comprehensive cloud-native security platform offering CWPP capabilities along with workload protection, compliance, and runtime security.
Key Features
- Runtime threat detection
- Container and Kubernetes security
- Vulnerability scanning
- Compliance monitoring
- Risk prioritization
- Multi-cloud visibility
Pros
- Full cloud security coverage
- Strong enterprise features
Cons
- Complex setup
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, RBAC, encryption
- Not publicly stated
Integrations & Ecosystem
- AWS, Azure, GCP
- SIEM, SOAR tools
Support & Community
Enterprise support with strong documentation.
#2 — Wiz
Short description: A cloud-native platform providing agentless workload protection with deep visibility into vulnerabilities, identities, and risks.
Key Features
- Agentless scanning
- Risk prioritization
- Attack path analysis
- Identity insights
- Data security visibility
Pros
- Easy deployment
- Strong analytics
Cons
- Cloud-only focus
- Limited on-prem support
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- DevOps tools
Support & Community
Strong onboarding and support.
#3 — Microsoft Defender for Cloud
Short description: A unified cloud security platform providing CWPP and posture management across Microsoft environments.
Key Features
- Workload protection
- Threat detection
- Security scoring
- Compliance monitoring
- Integration with Azure
Pros
- Strong Microsoft integration
- Unified visibility
Cons
- Limited outside ecosystem
- Requires configuration
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA, RBAC
- Not publicly stated
Integrations & Ecosystem
- Microsoft ecosystem
Support & Community
Enterprise support and documentation.
#4 — CrowdStrike Falcon Cloud Security
Short description: A cloud-native platform offering workload protection, threat detection, and real-time visibility across environments.
Key Features
- Runtime protection
- Threat intelligence integration
- Asset discovery
- Risk prioritization
- Automated response
Pros
- Strong real-time protection
- Integrated ecosystem
Cons
- Requires Falcon platform
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- CrowdStrike ecosystem
- Cloud tools
Support & Community
Enterprise support available.
#5 — Orca Security
Short description: An agentless CWPP platform providing deep visibility into workloads, vulnerabilities, and misconfigurations.
Key Features
- Agentless workload scanning
- Vulnerability detection
- Data exposure analysis
- Risk prioritization
- Compliance monitoring
Pros
- Fast deployment
- Strong visibility
Cons
- Cloud-focused
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- Security tools
Support & Community
Strong support and onboarding.
#6 — Lacework
Short description: A behavior-based cloud security platform that monitors workloads and detects anomalies using analytics.
Key Features
- Behavioral analytics
- Threat detection
- Compliance monitoring
- Automation
- Workload visibility
Pros
- Strong anomaly detection
- Scalable platform
Cons
- Complex dashboards
- Learning curve
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud providers
- Security tools
Support & Community
Good documentation and support.
#7 — Trend Micro Cloud One – Workload Security
Short description: A CWPP solution focused on securing cloud workloads with vulnerability protection and compliance monitoring.
Key Features
- Malware protection
- Vulnerability shielding
- Intrusion detection
- Compliance monitoring
- Automation
Pros
- Strong workload protection
- Easy integration
Cons
- Limited advanced analytics
- Requires tuning
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- Security tools
Support & Community
Reliable support and documentation.
#8 — Check Point CloudGuard Workload Protection
Short description: A platform offering CWPP capabilities with threat prevention and compliance across cloud environments.
Key Features
- Workload protection
- Threat prevention
- Compliance checks
- Risk prioritization
- Multi-cloud support
Pros
- Strong security features
- Multi-cloud capabilities
Cons
- Complex setup
- Requires expertise
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud providers
- Security tools
Support & Community
Enterprise support available.
#9 — Aqua Security Platform
Short description: A cloud-native security platform offering CWPP along with container and Kubernetes security.
Key Features
- Container security
- Runtime protection
- Vulnerability scanning
- Compliance monitoring
- DevSecOps integration
Pros
- Strong container security
- DevOps-friendly
Cons
- Complex setup
- Requires expertise
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Cloud and DevOps tools
Support & Community
Enterprise support and training.
#10 — SentinelOne Singularity Cloud Security
Short description: A platform combining endpoint and cloud workload protection for unified threat detection and response.
Key Features
- Endpoint and workload protection
- Threat detection
- Risk prioritization
- Automation
- Analytics dashboards
Pros
- Strong endpoint integration
- Real-time visibility
Cons
- Focused on endpoint ecosystem
- Requires integration for full coverage
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Endpoint and cloud tools
Support & Community
Enterprise support and documentation.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Prisma Cloud | Enterprise | Web | Cloud | Full cloud security | N/A |
| Wiz | Cloud-first teams | Web | Cloud | Agentless scanning | N/A |
| Defender for Cloud | Enterprise | Web | Cloud | Microsoft integration | N/A |
| CrowdStrike Falcon | Enterprise | Web | Cloud | Real-time protection | N/A |
| Orca Security | Enterprise | Web | Cloud | Agentless visibility | N/A |
| Lacework | Enterprise | Web | Cloud | Behavioral analytics | N/A |
| Trend Micro | SMB/Enterprise | Web | Cloud | Malware protection | N/A |
| CloudGuard | Enterprise | Web | Cloud | Multi-cloud security | N/A |
| Aqua Security | DevSecOps | Web | Cloud | Container security | N/A |
| SentinelOne | Enterprise | Web | Cloud | Endpoint + cloud | N/A |
Evaluation & Scoring of Cloud Workload Protection Platforms (CWPP)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Prisma Cloud | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Wiz | 9 | 8 | 7 | 8 | 9 | 8 | 7 | 8.3 |
| Defender | 8 | 8 | 7 | 8 | 8 | 7 | 7 | 7.9 |
| CrowdStrike | 9 | 7 | 8 | 8 | 9 | 8 | 7 | 8.2 |
| Orca | 9 | 8 | 7 | 8 | 9 | 8 | 7 | 8.3 |
| Lacework | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
| Trend Micro | 7 | 8 | 6 | 7 | 7 | 7 | 7 | 7.2 |
| CloudGuard | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
| Aqua | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
| SentinelOne | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.8 |
Scores are comparative and reflect strengths across functionality, usability, integrations, and value. Higher scores indicate stronger enterprise readiness.
Which Cloud Workload Protection Platform (CWPP) Tool Is Right for You?
Solo / Freelancer
CWPP tools are generally unnecessary unless managing cloud workloads.
SMB
Trend Micro and simplified cloud tools provide easier deployment.
Mid-Market
Wiz and Orca Security offer strong visibility and scalability.
Enterprise
Prisma Cloud, CrowdStrike, and Microsoft Defender provide comprehensive protection.
Budget vs Premium
Budget tools focus on basic workload protection; premium tools provide advanced analytics and automation.
Feature Depth vs Ease of Use
Advanced platforms require expertise, while simpler tools enable faster adoption.
Integrations & Scalability
Choose tools that integrate with your cloud and DevOps ecosystem.
Security & Compliance Needs
Ensure alignment with compliance frameworks and internal policies.
Frequently Asked Questions (FAQs)
What is CWPP?
A CWPP is a platform that protects cloud workloads such as VMs, containers, and serverless functions.
How is CWPP different from CSPM?
CWPP focuses on protecting workloads, while CSPM focuses on cloud misconfigurations.
Does CWPP provide real-time protection?
Yes, most platforms provide continuous monitoring and runtime threat detection.
Is CWPP part of CNAPP?
Yes, CWPP is often a component of broader cloud security platforms.
What workloads does CWPP protect?
Virtual machines, containers, serverless functions, and cloud applications.
Can CWPP detect vulnerabilities?
Yes, CWPP tools scan workloads for vulnerabilities and misconfigurations.
Is CWPP cloud-only?
Primarily yes, but it also supports hybrid environments.
Can CWPP integrate with DevOps?
Yes, many tools integrate with CI/CD pipelines for security automation.
What are common mistakes?
Ignoring runtime protection and relying only on configuration scanning.
Are CWPP tools scalable?
Yes, they are designed for large, dynamic cloud environments.
Conclusion
Cloud Workload Protection Platforms are a critical component of modern cloud security, providing continuous protection for workloads across dynamic environments. They help organizations detect threats, manage vulnerabilities, and enforce security policies throughout the workload lifecycle.
As cloud environments grow more complex, CWPP tools enable security teams to maintain visibility and control without slowing down development. They bridge the gap between infrastructure security and application protection.
Choosing the right CWPP depends on your cloud architecture, workload types, and integration requirements. Enterprise platforms offer deep capabilities, while simpler tools provide faster deployment and ease of use.
The best approach is to shortlist a few platforms, test them in your environment, and ensure they align with your security strategy and operational workflows.