Introduction
Deception Technology Tools are advanced cybersecurity solutions that use decoys, fake assets, and traps to detect and mislead attackers inside a network. Instead of only blocking threats, these tools actively lure attackers into interacting with false systems—such as fake servers, credentials, or databases—triggering high-confidence alerts when malicious activity occurs.
This approach is gaining importance because traditional defenses often fail to detect attackers who bypass perimeter security. Deception technology provides early detection, reduced false positives, and deep insights into attacker behavior, making it a powerful addition to modern security strategies.
Use Cases:
- Detecting lateral movement inside networks
- Identifying insider threats
- Protecting critical assets and credentials
- Reducing attacker dwell time
- Enhancing threat intelligence and incident response
What buyers should evaluate:
- Types of deception assets (honeypots, honeytokens, credentials)
- Deployment coverage (endpoint, network, cloud)
- Integration with SIEM, SOAR, EDR
- Automation and orchestration capabilities
- Ease of deployment and scalability
- Alert accuracy and false positive reduction
- Threat intelligence insights
- Support and ecosystem
Best for: Enterprises, SOC teams, security analysts, and organizations with mature cybersecurity programs
Not ideal for: Small organizations without dedicated security operations or those lacking foundational security controls
Key Trends in Deception Technology Tools
- Shift from static honeypots to dynamic deception platforms
- Integration with SIEM, XDR, and SOAR ecosystems
- AI-driven deception asset generation
- Expansion into cloud, SaaS, and Kubernetes environments
- Identity-based deception (fake credentials, tokens)
- Automated attack path simulation
- Reduced false positives through high-confidence alerts
- Use in ransomware detection and prevention
- Increased focus on insider threat detection
- Adoption as part of layered defense strategy
How We Selected These Tools (Methodology)
- Market adoption and vendor credibility
- Depth of deception capabilities
- Coverage across environments (cloud, network, endpoint)
- Integration with existing security stack
- Automation and orchestration features
- Alert accuracy and detection quality
- Scalability and performance
- Innovation in deception techniques
- Customer fit across enterprise and mid-market
- Support and documentation quality
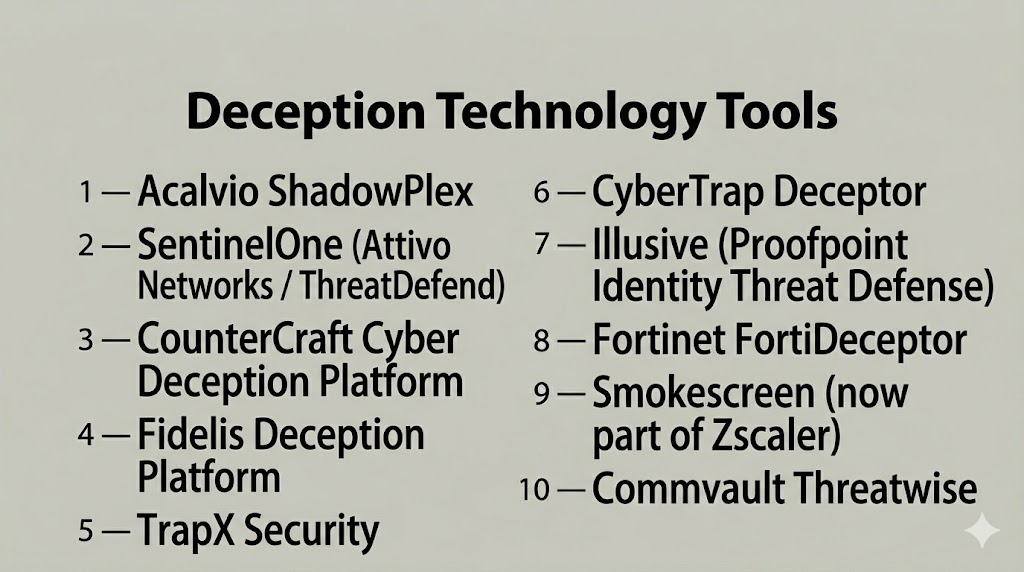
Top 10 Deception Technology Tools
#1 — Acalvio ShadowPlex
Short description: A deception platform focused on active defense using realistic decoys and automated attack detection.
Key Features
- Automated deception deployment
- Attack path analysis
- Threat detection
- Asset discovery
- Risk prioritization
Pros
- Strong automation
- High-fidelity alerts
Cons
- Enterprise-focused
- Requires tuning
Platforms / Deployment
- Web
- Cloud / Hybrid
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
Integrates with SIEM, SOAR, and security platforms
- Cloud and network tools
Support & Community
Enterprise support available
#2 — SentinelOne (Attivo Networks ThreatDefend)
Short description: A deception platform focused on identity-based attacks and endpoint visibility.
Key Features
- Identity deception
- Endpoint detection
- Credential protection
- Threat analytics
- Automated response
Pros
- Strong identity protection
- Integrated with endpoint security
Cons
- Requires SentinelOne ecosystem
- Complex setup
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Endpoint and security tools
Support & Community
Enterprise support
#3 — CounterCraft Cyber Deception Platform
Short description: A deception platform designed to create realistic attacker environments and collect threat intelligence.
Key Features
- Custom deception scenarios
- Threat intelligence collection
- Attack simulation
- Monitoring dashboards
- Automation
Pros
- Strong threat intelligence
- Flexible deployment
Cons
- Requires expertise
- Complex configuration
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security platforms
Support & Community
Vendor support available
#4 — Fidelis Deception Platform
Short description: A deception solution focused on detecting advanced threats and lateral movement.
Key Features
- Network deception
- Threat detection
- Attack path visibility
- Automated alerts
- Integration with SOC tools
Pros
- Strong detection capabilities
- Good integration
Cons
- Complex deployment
- Requires expertise
Platforms / Deployment
- Web
- Cloud / Hybrid
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM, EDR tools
Support & Community
Enterprise support
#5 — TrapX Security
Short description: A deception platform using decoy systems to detect threats across enterprise environments.
Key Features
- Honeypot deployment
- Threat detection
- Asset monitoring
- Automated alerts
- Risk analysis
Pros
- Easy deployment
- Good visibility
Cons
- Limited advanced features
- Smaller ecosystem
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security tools
Support & Community
Vendor support
#6 — CyberTrap Deceptor
Short description: A deception solution focused on detecting insider threats and lateral movement.
Key Features
- Insider threat detection
- Credential traps
- Attack detection
- Monitoring dashboards
- Analytics
Pros
- Strong insider threat focus
- Accurate alerts
Cons
- Limited cloud capabilities
- Requires setup
Platforms / Deployment
- Web
- On-prem / Hybrid
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security tools
Support & Community
Vendor support
#7 — Illusive (Proofpoint Identity Threat Defense)
Short description: A deception platform focused on identity and credential-based attacks.
Key Features
- Credential deception
- Identity protection
- Threat detection
- Risk prioritization
- Analytics
Pros
- Strong identity focus
- Advanced analytics
Cons
- Enterprise-focused
- Requires integration
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, MFA
- Not publicly stated
Integrations & Ecosystem
- Identity and security tools
Support & Community
Enterprise support
#8 — Fortinet FortiDeceptor
Short description: A deception platform integrated with Fortinet’s security ecosystem.
Key Features
- Network deception
- Threat detection
- Automated alerts
- Asset monitoring
- Integration with Fortinet tools
Pros
- Strong ecosystem integration
- Flexible deployment
Cons
- Requires Fortinet ecosystem
- Complex setup
Platforms / Deployment
- Web
- On-prem / Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Fortinet ecosystem
Support & Community
Enterprise support
#9 — Smokescreen (Zscaler Deception)
Short description: A deception platform focused on endpoint and identity-based deception.
Key Features
- Endpoint deception
- Credential traps
- Threat detection
- Monitoring tools
- Automation
Pros
- Strong endpoint coverage
- Lightweight deployment
Cons
- Limited ecosystem
- Requires tuning
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Security tools
Support & Community
Vendor support
#10 — Commvault Threatwise
Short description: A deception-based ransomware detection platform.
Key Features
- Decoy data deployment
- Ransomware detection
- Automated alerts
- Data protection
- Monitoring tools
Pros
- Strong ransomware detection
- Easy deployment
Cons
- Limited broader deception features
- Niche use case
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Backup and security tools
Support & Community
Vendor support
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Acalvio | Enterprise | Web | Hybrid | Automated deception | N/A |
| SentinelOne | Enterprise | Web | Cloud | Identity protection | N/A |
| CounterCraft | Enterprise | Web | Cloud | Threat intelligence | N/A |
| Fidelis | Enterprise | Web | Hybrid | Network deception | N/A |
| TrapX | SMB/Enterprise | Web | Cloud | Easy deployment | N/A |
| CyberTrap | Enterprise | Web | Hybrid | Insider detection | N/A |
| Illusive | Enterprise | Web | Cloud | Credential deception | N/A |
| FortiDeceptor | Enterprise | Web | Hybrid | Ecosystem integration | N/A |
| Smokescreen | SMB/Enterprise | Web | Cloud | Endpoint deception | N/A |
| Threatwise | SMB/Enterprise | Web | Cloud | Ransomware detection | N/A |
Evaluation & Scoring of Deception Technology Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Acalvio | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.3 |
| SentinelOne | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.3 |
| CounterCraft | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Fidelis | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| TrapX | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.4 |
| CyberTrap | 7 | 7 | 6 | 8 | 7 | 7 | 7 | 7.2 |
| Illusive | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| FortiDeceptor | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Smokescreen | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.4 |
| Threatwise | 7 | 8 | 6 | 7 | 7 | 7 | 8 | 7.4 |
Scores are comparative and reflect strengths in deception depth, usability, integrations, and value.
Which Deception Technology Tool Is Right for You?
Solo / Freelancer
Not typically required unless working in advanced security environments.
SMB
TrapX and Smokescreen offer simpler deployment and cost efficiency.
Mid-Market
Fidelis and CounterCraft provide balanced capabilities.
Enterprise
Acalvio, SentinelOne, and Illusive deliver advanced deception strategies.
Budget vs Premium
Budget tools focus on basic traps; premium tools provide full deception ecosystems.
Feature Depth vs Ease of Use
Advanced tools require expertise but offer deeper visibility.
Integrations & Scalability
Choose tools that integrate with SIEM, EDR, and SOC workflows.
Security & Compliance Needs
Ensure alignment with enterprise security and compliance strategies.
Frequently Asked Questions (FAQs)
1.What is deception technology?
It is a cybersecurity approach that uses decoys to detect attackers early.
2.How does deception technology work?
It deploys fake assets that trigger alerts when accessed.
3.Why is it important?
It provides early detection and reduces attacker dwell time.
4.Is deception technology proactive?
Yes, it actively lures attackers instead of only blocking them.
5.Does it reduce false positives?
Yes, interactions with decoys are highly indicative of threats.
6.Can it detect insider threats?
Yes, unauthorized access to decoys indicates suspicious behavior.
7.Is it cloud-compatible?
Yes, modern tools support cloud and hybrid environments.
8.Can it integrate with SIEM?
Yes, most platforms integrate with SIEM and SOC tools.
9.What are common mistakes?
Poor deployment and lack of integration with existing tools.
10.Is it a replacement for other security tools?
No, it works best as an additional layer of defense.
Conclusion
Deception Technology Tools represent a shift from passive defense to proactive cybersecurity, allowing organizations to detect attackers early and gather valuable intelligence. By deploying realistic decoys and traps, these tools create an environment where attackers reveal themselves quickly.
They are particularly effective in reducing false positives and improving incident response, making them a valuable addition to modern SOC operations. As threats become more sophisticated, deception provides a strategic advantage by misleading attackers and exposing their tactics.
However, these tools are not standalone solutions—they work best when integrated with existing security systems such as SIEM, EDR, and XDR. Organizations should carefully evaluate their needs, infrastructure, and maturity before implementation.