Introduction
Single Sign-On (SSO) is an authentication system that allows users to log in once and access multiple applications, systems, or services without needing to sign in again. In simple terms, SSO works like a single digital identity “master key” that unlocks all authorized apps in an organization.
Instead of managing multiple usernames and passwords, users authenticate through a central identity provider, which then grants secure access to connected applications.
SSO is a core component of modern Identity & Access Management (IAM) and is widely used in cloud environments, enterprise IT systems, SaaS platforms, and hybrid infrastructures.
Why SSO matters today
- Reduces password fatigue and login complexity
- Improves security by centralizing authentication
- Supports remote and hybrid workforce environments
- Enhances productivity by reducing login friction
- Helps enforce Zero Trust security models
- Simplifies IT administration and access control
Common use cases
- Enterprise access to SaaS applications
- Employee login to internal systems
- Customer login across multiple services
- Education platforms accessing multiple tools
- Government portals with unified identity access
- Cloud application authentication
Key evaluation criteria
- SSO protocol support (SAML, OAuth, OpenID Connect)
- MFA and adaptive authentication
- User lifecycle management integration
- Directory services compatibility
- Security policy enforcement
- Scalability and performance
- Cloud and hybrid deployment support
- API and developer integration
- Audit logs and compliance readiness
- Ease of configuration and administration
Best for:
SSO platforms are best for enterprises, SaaS companies, government systems, and organizations managing multiple applications and user identities.
Not ideal for:
They are less useful for single-application systems or very small teams with minimal authentication needs.
Key Trends in Single Sign-On (SSO)
- Rapid shift toward passwordless authentication systems
- Strong adoption of Zero Trust identity frameworks
- Increased use of adaptive and risk-based authentication
- Integration with AI-driven anomaly detection
- Expansion of social login and federated identity
- Growth of Identity-as-a-Service (IDaaS) platforms
- Stronger API-first authentication architectures
- Improved session security and token management
- Multi-cloud and hybrid identity federation
- Tighter integration with cybersecurity ecosystems (IAM, PAM, CIAM)
How We Selected These Tools (Methodology)
- Global adoption across enterprise and SaaS ecosystems
- Strength of authentication and federation capabilities
- Protocol support (SAML, OAuth, OpenID Connect)
- Security features like MFA and adaptive authentication
- Scalability across large user bases
- Cloud and hybrid deployment flexibility
- Integration with enterprise systems and apps
- Identity lifecycle management capabilities
- Vendor maturity and reliability
- Real-world enterprise usage performance
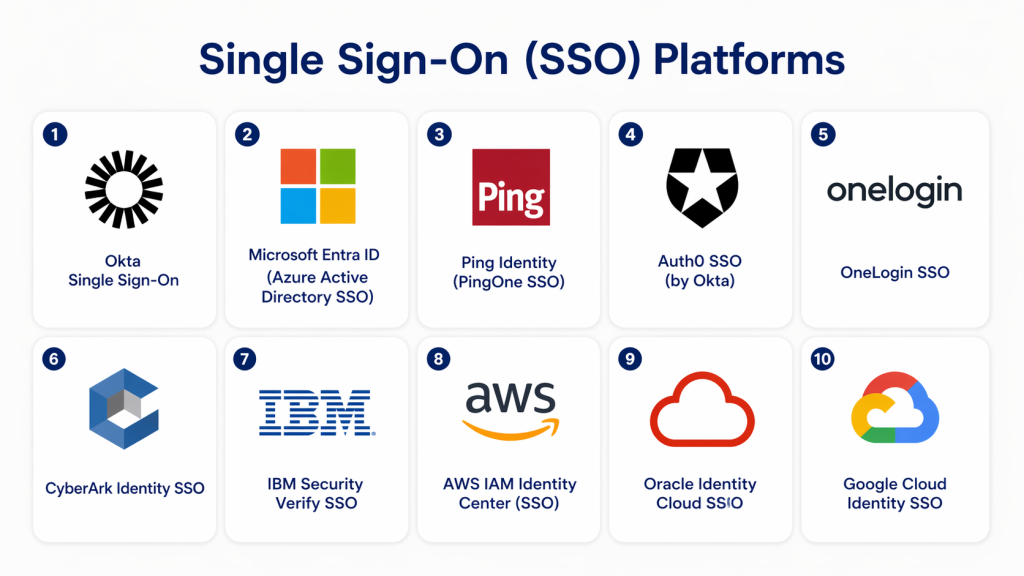
Top 10 Single Sign-On (SSO) Platforms
1 — Okta Single Sign-On
Short description:
Okta is a leading identity platform offering secure SSO, MFA, and lifecycle management across thousands of applications.
Key Features
- Single Sign-On across SaaS applications
- Multi-Factor Authentication (MFA)
- Adaptive authentication policies
- Universal directory integration
- API access management
- Identity federation support
- User lifecycle automation
Pros
- Strong enterprise adoption
- Easy integration with SaaS tools
- Highly scalable architecture
Cons
- Premium pricing
- Advanced configuration requires expertise
Platforms / Deployment
- Cloud
Security & Compliance
- SOC 2 compliance support
- MFA and encryption
- RBAC and audit logs
Integrations & Ecosystem
- SaaS applications
- Cloud platforms
- Security tools
- API systems
Support & Community
Strong global enterprise support and developer ecosystem.
2 — Microsoft Entra ID (Azure Active Directory)
Short description:
Microsoft Entra ID provides enterprise-grade SSO tightly integrated with Microsoft and cloud ecosystems.
Key Features
- SSO across Microsoft and third-party apps
- Conditional access policies
- MFA and passwordless login
- Identity protection and risk detection
- Hybrid identity support
- Device-based access control
- User lifecycle management
Pros
- Deep Microsoft ecosystem integration
- Strong enterprise security controls
- Wide adoption in enterprises
Cons
- Complex licensing
- Best suited for Microsoft environments
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Conditional access policies
- MFA enforcement
- Audit and compliance reporting
Integrations & Ecosystem
- Microsoft 365
- Azure services
- Enterprise SaaS apps
- Security platforms
Support & Community
Strong enterprise Microsoft support ecosystem.
3 — Ping Identity
Short description:
Ping Identity offers flexible SSO and identity federation solutions for enterprise and hybrid environments.
Key Features
- SSO and MFA support
- Identity federation
- Adaptive authentication
- API security
- Identity orchestration
- Directory integration
- Zero Trust identity support
Pros
- Strong hybrid identity support
- High flexibility
- Enterprise-grade security
Cons
- Complex implementation
- Higher cost for enterprise features
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- MFA and encryption
- Audit logging
- Compliance support
Integrations & Ecosystem
- Enterprise applications
- Cloud systems
- APIs
- Security tools
Support & Community
Strong enterprise-focused support.
4 — Auth0 (by Okta)
Short description:
Auth0 is a developer-friendly identity platform that simplifies authentication and SSO implementation.
Key Features
- SSO and MFA
- Social login integration
- Custom login flows
- Passwordless authentication
- API authentication
- Role-based access control
- Token-based security
Pros
- Developer-centric design
- Fast implementation
- Flexible authentication flows
Cons
- Can become expensive at scale
- Requires technical setup
Platforms / Deployment
- Cloud
Security & Compliance
- SOC 2 compliance support
- MFA and encryption
- Secure token management
Integrations & Ecosystem
- Web and mobile apps
- APIs
- Cloud services
- Developer frameworks
Support & Community
Strong developer documentation and community.
5 — OneLogin
Short description:
OneLogin provides cloud-based SSO with strong enterprise authentication and user management features.
Key Features
- Single Sign-On across apps
- Multi-Factor Authentication
- User provisioning automation
- Smart password management
- Directory integration
- Risk-based authentication
- Cloud directory services
Pros
- Easy deployment
- Strong SSO capabilities
- Good SMB and mid-market fit
Cons
- Limited advanced enterprise customization
- Smaller ecosystem
Platforms / Deployment
- Cloud
Security & Compliance
- MFA support
- Encryption
- Audit logs
Integrations & Ecosystem
- SaaS applications
- HR systems
- Cloud platforms
- APIs
Support & Community
Good mid-market support.
6 — CyberArk Identity
Short description:
CyberArk Identity focuses on secure access management with strong privileged access protection and SSO capabilities.
Key Features
- SSO and MFA
- Privileged access management
- Identity lifecycle control
- Adaptive authentication
- Secure password vaulting
- Session monitoring
- Access policies
Pros
- Strong privileged access security
- Enterprise-grade protection
- Strong compliance capabilities
Cons
- Complex setup
- High cost
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Encryption and RBAC
- Audit trails
- Compliance support
Integrations & Ecosystem
- Security platforms
- Enterprise directories
- Cloud systems
- SIEM tools
Support & Community
Strong enterprise security support.
7 — IBM Security Verify
Short description:
IBM Security Verify provides enterprise identity governance, authentication, and SSO capabilities.
Key Features
- SSO and MFA
- Identity lifecycle management
- Risk-based authentication
- Access analytics
- Directory integration
- API authentication
- User provisioning
Pros
- Strong enterprise identity governance
- Advanced analytics
- Scalable architecture
Cons
- Complex configuration
- Enterprise pricing
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC and encryption
- Audit logs
- Compliance reporting
Integrations & Ecosystem
- IBM security suite
- Enterprise applications
- Cloud systems
- APIs
Support & Community
Strong IBM enterprise support.
8 — AWS IAM Identity Center
Short description:
AWS IAM Identity Center provides SSO access management for AWS and connected applications.
Key Features
- Centralized SSO for AWS apps
- Role-based access control
- Identity federation support
- Multi-account management
- Temporary credentials
- Access auditing
- Cloud integration
Pros
- Deep AWS integration
- Highly scalable
- Strong cloud security model
Cons
- AWS ecosystem dependency
- Complex policy structure
Platforms / Deployment
- Cloud (AWS)
Security & Compliance
- IAM policies
- Encryption
- Audit logging
Integrations & Ecosystem
- AWS services
- Cloud apps
- DevOps tools
- Security platforms
Support & Community
Strong AWS documentation support.
9 — Oracle Identity Cloud Service
Short description:
Oracle Identity Cloud Service provides enterprise SSO and identity management for Oracle ecosystems.
Key Features
- SSO and MFA
- User provisioning
- Identity lifecycle management
- Adaptive authentication
- Directory integration
- API security
- Role-based access
Pros
- Strong Oracle ecosystem integration
- Enterprise scalability
- Reliable identity control
Cons
- Best within Oracle systems
- Complex configuration
Platforms / Deployment
- Cloud
Security & Compliance
- Encryption and RBAC
- Audit logs
- Compliance support
Integrations & Ecosystem
- Oracle applications
- Enterprise SaaS tools
- Cloud systems
- APIs
Support & Community
Strong enterprise Oracle support.
10 — Google Cloud Identity
Short description:
Google Cloud Identity provides SSO and access management for Google Workspace and enterprise applications.
Key Features
- SSO and MFA
- Device management
- Identity lifecycle control
- Access policies
- Directory sync
- Security monitoring
- Conditional access
Pros
- Strong Google ecosystem integration
- Easy cloud deployment
- Scalable architecture
Cons
- Google ecosystem dependency
- Limited advanced customization
Platforms / Deployment
- Cloud
Security & Compliance
- IAM-based controls
- Encryption
- Audit logs
Integrations & Ecosystem
- Google Workspace
- Cloud applications
- SaaS tools
- APIs
Support & Community
Strong Google enterprise support.
Comparison Table (Top 10)
| Tool | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Okta | Enterprise SaaS | Multi | Cloud | Strong SSO ecosystem | N/A |
| Microsoft Entra ID | Microsoft ecosystem | Multi | Hybrid | Conditional access | N/A |
| Ping Identity | Enterprises | Multi | Hybrid | Identity orchestration | N/A |
| Auth0 | Developers | Multi | Cloud | Developer-first SSO | N/A |
| OneLogin | SMB/mid-market | Cloud | Cloud | Easy SSO setup | N/A |
| CyberArk | Privileged access | Multi | Hybrid | PAM security | N/A |
| IBM Verify | Large enterprises | Multi | Hybrid | Identity governance | N/A |
| AWS IAM Center | AWS users | AWS | Cloud | Multi-account SSO | N/A |
| Oracle Identity | Oracle ecosystem | Cloud | Cloud | Enterprise identity control | N/A |
| Google Cloud Identity | Google ecosystem | Cloud | Cloud | Device + identity control | N/A |
Evaluation & Scoring of SSO Platforms
| Tool | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Total |
|---|---|---|---|---|---|---|---|---|
| Okta | 9 | 9 | 10 | 10 | 9 | 9 | 8 | 9.1 |
| Entra ID | 9 | 7 | 10 | 10 | 9 | 9 | 9 | 8.9 |
| Ping | 9 | 7 | 9 | 10 | 9 | 8 | 7 | 8.4 |
| Auth0 | 9 | 9 | 9 | 9 | 9 | 8 | 8 | 8.7 |
| OneLogin | 8 | 9 | 8 | 9 | 8 | 8 | 9 | 8.4 |
| CyberArk | 10 | 6 | 9 | 10 | 9 | 9 | 7 | 8.6 |
| IBM Verify | 9 | 7 | 9 | 10 | 9 | 9 | 7 | 8.6 |
| AWS IAM | 9 | 6 | 10 | 10 | 9 | 8 | 9 | 8.5 |
| Oracle Identity | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 7.9 |
| Google Cloud Identity | 8 | 8 | 9 | 9 | 8 | 8 | 9 | 8.4 |
Which SSO Platform Is Right for You?
SMB / Startups
- Auth0
- OneLogin
- Google Cloud Identity
Mid-Market
- Okta
- Ping Identity
- AWS IAM Identity Center
Enterprise
- Microsoft Entra ID
- CyberArk
- IBM Security Verify
- Oracle Identity
Frequently Asked Questions (FAQs)
1. What is Single Sign-On (SSO)?
SSO allows users to log in once and access multiple applications without re-entering credentials. It improves convenience and security.
2. Why is SSO important?
It reduces password fatigue and improves security by centralizing authentication. It also simplifies IT management.
3. Is SSO secure?
Yes, when properly configured with MFA and encryption. It reduces password-related risks significantly.
4. What is the difference between SSO and IAM?
SSO is a part of IAM. IAM manages identities and access, while SSO focuses on login experience.
5. Can SSO be used with MFA?
Yes, most SSO platforms integrate MFA for additional security layers.
6. Does SSO work for mobile apps?
Yes, modern SSO systems support web, mobile, and API authentication.
7. Is SSO cloud-based?
Most modern SSO platforms are cloud-based or hybrid.
8. What is a common SSO protocol?
SAML, OAuth 2.0, and OpenID Connect are widely used protocols.
9. What industries use SSO?
Finance, healthcare, SaaS, education, and government sectors widely use SSO.
10. What is the biggest risk of SSO?
If compromised, a single account can grant access to multiple systems. That is why MFA is critical.
Conclusion
Single Sign-On (SSO) platforms are essential for modern identity security and user experience. They simplify authentication, reduce password-related risks, and enable secure access across multiple applications.
From enterprise leaders like Okta and Microsoft Entra ID to developer-friendly platforms like Auth0, each solution serves different organizational needs.
Choosing the right SSO platform depends on your ecosystem, scale, and security requirements. A strong SSO strategy ensures better user experience, improved security, and centralized identity control across all systems.