Introduction
Software Composition Analysis (SCA) Tools are solutions that analyze an application’s open‑source and third‑party dependencies to identify known vulnerabilities, license risks, and outdated components. As modern software increasingly relies on open‑source libraries, managing associated risks has become a critical part of secure development practices.
SCA tools help teams understand what components are used in a codebase, identify security vulnerabilities (often from public vulnerability databases), track license compliance issues, and automate remediation suggestions. In regulated industries and security‑focused workflows, SCA is a mandatory step to reduce risk early in the development process.
Common use cases include:
- Detecting known security vulnerabilities in open‑source dependencies
- Tracking license compliance risks
- Generating SBOMs (Software Bill of Materials) for audits
- Automating dependency updates and remediation
- Integrating scans into CI/CD pipelines
Buyers should evaluate:
- Language and ecosystem coverage
- Vulnerability database breadth and update frequency
- License compliance detection and reporting
- CI/CD and DevOps pipeline integration
- False positive management and remediation suggestions
- Scalability and performance for large codebases
- Reporting and audit trail capabilities
- Pricing and licensing model
Best for: Developers, security teams, DevOps engineers, and organizations with significant use of open‑source or third‑party dependencies.
Not ideal for: Very small or hobby projects with minimal dependencies; lightweight dependency checks may suffice.
Key Trends in Software Composition Analysis (SCA) Tools
- Native SBOM generation and export formats
- Deeper integration with CI/CD and DevOps workflows
- AI‑assisted vulnerability prioritization
- License compliance automation for legal risk
- Real‑time dependency monitoring and alerts
- Support for container images and infrastructure artifacts
- API‑first scanning and automation hooks
- Integration with code review workflows
- Consolidated dashboards for risk posture
- Support for multi‑ecosystem polyglot applications
How We Selected These Tools (Methodology)
- Evaluated coverage across programming language ecosystems
- Assessed vulnerability database quality and update frequency
- Reviewed CI/CD integration capabilities
- Evaluated license compliance detection
- Considered ease of onboarding and developer adoption
- Included both open‑source and commercial tools
- Analyzed reporting and risk prioritization features
- Reviewed scalability for enterprise codebases
- Examined automation and remediation support
- Focused on real‑world usability in secure SDLC workflows
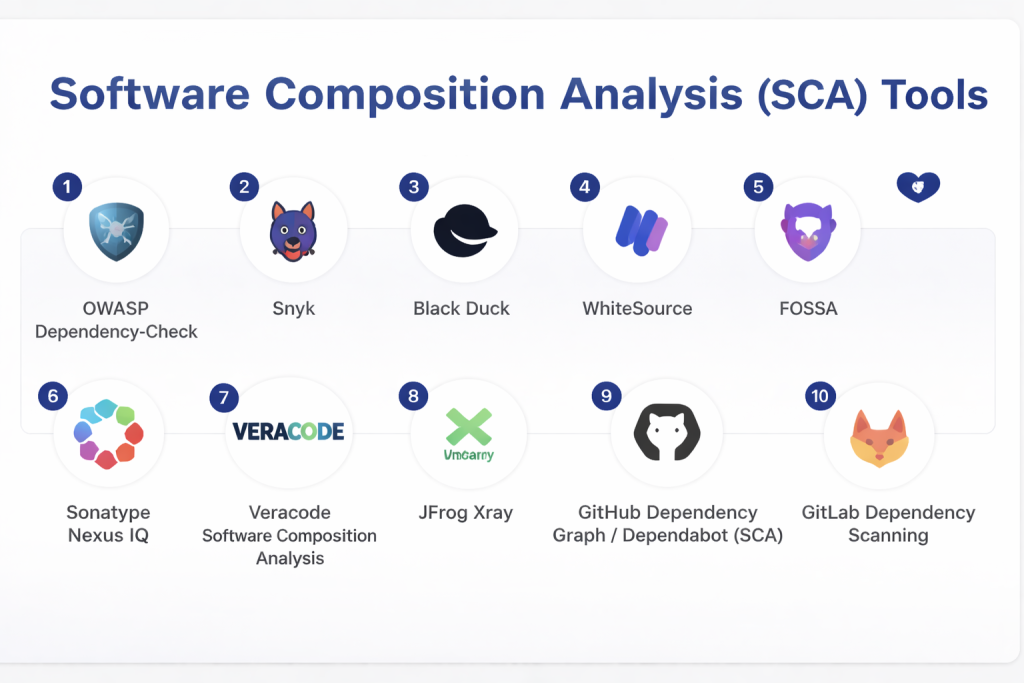
Top 10 Software Composition Analysis (SCA) Tools
#1 — OWASP Dependency‑Check
Short description: Open‑source SCA tool that scans project dependencies for known vulnerabilities using public vulnerability databases.
Key Features
- Dependency scanning
- CVE vulnerability reporting
- Generates HTML/XML reports
- Multiple language ecosystem support
- CI/CD integration plugins
- Command‑line interface
Pros
- Free and open‑source
- Broad ecosystem support
Cons
- Manual setup required
- Noise/false positives without tuning
Platforms / Deployment
- Cross‑platform (CLI)
Security & Compliance
- Uses public vulnerability feeds
Integrations & Ecosystem
- CI/CD tools, build tools, IDEs
Support & Community
Community support and documentation.
#2 — Snyk
Short description: Developer‑friendly SCA platform that finds vulnerabilities and suggests fixes for open‑source dependencies.
Key Features
- Dependency scanning
- Real‑time alerts
- Fix suggestions/patches
- License risk detection
- CI/CD integration
- IDE and VCS integrations
Pros
- Easy to onboard developers
- Automated fix suggestions
Cons
- Paid plans for advanced features
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- License compliance and risk reporting
Integrations & Ecosystem
- GitHub, GitLab, CI/CD tools, IDEs
Support & Community
Commercial support with documentation.
#3 — Black Duck
Short description: Enterprise SCA tool with deep vulnerability intelligence and compliance reporting.
Key Features
- Vulnerability and license risk detection
- Policy enforcement
- SBOM generation
- Continuous monitoring
- Detailed reporting
- CI/CD integration
Pros
- Comprehensive enterprise risk coverage
- Deep vulnerability intelligence
Cons
- Complex pricing and setup
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- License compliance and audit capabilities
Integrations & Ecosystem
- CI/CD tools, DevOps pipelines, IDEs
Support & Community
Enterprise support and training.
#4 — WhiteSource
Short description: SCA solution that automatically detects vulnerabilities and enforces license policies across open‑source dependencies.
Key Features
- Auto detection of open‑source components
- Vulnerability alerts
- License compliance enforcement
- Patch and remediation suggestions
- SBOM export
- CI/CD integration
Pros
- Automated detection and alerts
- Strong compliance tooling
Cons
- Paid solution
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- Powerful license and risk reporting
Integrations & Ecosystem
- GitHub, GitLab, CI/CD tools
Support & Community
Vendor support and resources.
#5 — FOSSA
Short description: SCA platform focused on security and license compliance for open‑source software.
Key Features
- Dependency scanning
- Continuous monitoring
- License compliance reporting
- Automated remediation
- SBOM generation
- CI/CD pipelines
Pros
- Strong license compliance
- Developer‑friendly alerts
Cons
- Enterprise pricing
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- License risk enforcement
- Security vulnerability detection
Integrations & Ecosystem
- IDEs, SCM, CI/CD tools
Support & Community
Commercial support.
#6 — Sonatype Nexus IQ
Short description: SCA and governance tool that enforces open‑source policies and security checks across development workflows.
Key Features
- Policy enforcement
- Vulnerability and license risk detection
- Continuous monitoring
- SBOM and reports
- Integrations with build systems
- Automated alerts
Pros
- Enterprise‑grade governance
- Deep integration with build pipelines
Cons
- Paid and complex
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- Policy and governance reporting
Integrations & Ecosystem
- Maven, Gradle, CI/CD tools
Support & Community
Vendor support.
#7 — Veracode Software Composition Analysis
Short description: Security‑focused SCA tool from Veracode that identifies vulnerabilities and risks in dependencies.
Key Features
- Vulnerability detection
- License risk analysis
- Risk scoring
- CI/CD integration
- Developer feedback tools
- Reporting dashboards
Pros
- Strong security posture
- Integrated risk analytics
Cons
- Paid platform
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Enterprise risk and compliance reporting
Integrations & Ecosystem
- IDEs, CI/CD tools, DevOps workflows
Support & Community
Commercial support resources.
#8 — JFrog Xray
Short description: Universal artifact scanning tool that includes SCA for components stored in artifact repositories.
Key Features
- Deep binary component scanning
- Vulnerability and license analysis
- Integration with JFrog Artifactory
- Impact analysis
- Continuous monitoring
- Reports and alerts
Pros
- Binary‑level SCA
- Great for artifact pipelines
Cons
- Tied to JFrog ecosystem
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- License and vulnerability reporting
Integrations & Ecosystem
- Artifactory, CI/CD tools, SCM
Support & Community
Commercial support.
#9 — GitHub Dependency Graph / Dependabot (SCA)
Short description: GitHub feature that builds a dependency graph and raises alerts for vulnerable components, with automated pull requests for updates.
Key Features
- Dependency graph visualization
- Vulnerability alerts
- Automated dependency updates
- License risk insights
- CI/CD integration
- GitHub native workflows
Pros
- Native GitHub experience
- Automated fix PRs
Cons
- Limited outside GitHub repos
Platforms / Deployment
- Cloud (GitHub)
Security & Compliance
- Vulnerability and license alerts
Integrations & Ecosystem
- GitHub Actions, issue tracking
Support & Community
GitHub documentation and community support.
#10 — GitLab Dependency Scanning
Short description: GitLab’s built‑in SCA feature that scans dependencies for vulnerabilities and license risks.
Key Features
- Dependency scanning
- Vulnerability and license alerts
- Integration with pipelines
- Auto‑generated reports
- Policy enforcement
- CI/CD integration
Pros
- Native GitLab integration
- Automated pipeline feedback
Cons
- Limited outside GitLab ecosystem
Platforms / Deployment
- Cloud / Self‑hosted
Security & Compliance
- Vulnerability and license reporting
Integrations & Ecosystem
- GitLab pipelines, package registries
Support & Community
Official documentation and community.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| OWASP Dependency‑Check | Open‑source users | Cross‑platform | CLI / Cloud | Vulnerability scanning | N/A |
| Snyk | Dev teams | Cross‑platform | Cloud/Hybrid | Fix suggestions | N/A |
| Black Duck | Enterprise | Cross‑platform | Cloud/Hybrid | Deep risk analysis | N/A |
| WhiteSource | Compliance & security | Cross‑platform | Cloud/Hybrid | License enforcement | N/A |
| FOSSA | License & security | Cross‑platform | Cloud/Hybrid | Continuous monitoring | N/A |
| Nexus IQ | Governance | Cross‑platform | Cloud/Hybrid | Policy enforcement | N/A |
| Veracode SCA | Secure SDLC | Cross‑platform | Cloud/Hybrid | Risk scoring | N/A |
| JFrog Xray | Artifact pipelines | Cross‑platform | Cloud/Hybrid | Binary scanning | N/A |
| GitHub Dependabot | GitHub repos | Cloud | Cloud | Auto PR updates | N/A |
| GitLab Dependency Scanning | GitLab users | Cloud/Self‑hosted | Hybrid | Native pipeline scanning | N/A |
Evaluation & Scoring of Software Composition Analysis (SCA) Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Dependency‑Check | 8 | 7 | 7 | 8 | 7 | 7 | 9 | 7.9 |
| Snyk | 9 | 9 | 9 | 8 | 8 | 8 | 8 | 8.7 |
| Black Duck | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.3 |
| WhiteSource | 9 | 8 | 9 | 9 | 8 | 8 | 8 | 8.4 |
| FOSSA | 8 | 8 | 8 | 8 | 7 | 7 | 8 | 8.0 |
| Nexus IQ | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.3 |
| Veracode SCA | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.1 |
| JFrog Xray | 8 | 8 | 8 | 8 | 8 | 7 | 8 | 8.0 |
| GitHub Dependabot | 8 | 9 | 8 | 7 | 7 | 8 | 9 | 8.3 |
| GitLab Dependency Scanning | 8 | 8 | 8 | 8 | 7 | 8 | 8 | 8.1 |
Which Software Composition Analysis (SCA) Tool Is Right for You?
Solo / Freelancer
OWASP Dependency‑Check or GitHub Dependabot for lightweight, free scanning.
SMB
Snyk or WhiteSource for developer‑friendly scanning and remediation.
Mid‑Market
Black Duck or Nexus IQ for governance and compliance coverage.
Enterprise
Veracode SCA, WhiteSource, or Black Duck for deep security and risk reporting.
Budget vs Premium
- Budget: Dependency‑Check, GitHub Dependabot
- Premium: Black Duck, Veracode SCA
Feature Depth vs Ease of Use
- Easy: Snyk, GitHub Dependabot
- Deep: Black Duck, Nexus IQ
Integrations & Scalability
- Enterprise‑grade: WhiteSource, Nexus IQ, Veracode SCA
Security & Compliance Needs
- Choose tools with robust reporting and SBOM support for regulated environments.
Frequently Asked Questions (FAQs)
1. What is Software Composition Analysis?
It’s analyzing software dependencies to detect vulnerabilities and license risks.
2. Why use SCA tools?
To catch known vulnerabilities and compliance issues early in development.
3. Are SCA tools free?
Some open‑source options exist; advanced enterprise tools are paid.
4. Do they integrate with CI/CD?
Yes, most integrate with pipelines for automated scanning.
5. What languages are covered?
Support varies; many cover multiple ecosystems like JavaScript, Python, Java.
6. What is an SBOM?
A Software Bill of Materials listing all dependencies and components.
7. Can tools auto‑fix dependencies?
Some, like Snyk and Dependabot, can generate update PRs.
8. Are license risks important?
Yes—illegal licensing can expose legal risks.
9. Do SCA tools detect runtime vulnerabilities?
They detect known issues via vulnerability databases.
10. Can SCA replace other security tests?
No, it complements dynamic and functional security testing.
Conclusion
Software Composition Analysis tools are essential for understanding and mitigating risks introduced by third‑party and open‑source dependencies. From open‑source options like OWASP Dependency‑Check and GitHub Dependabot to enterprise‑grade tools like Black Duck and WhiteSource, there’s an SCA tool for every scale and security need. Teams should evaluate language support, integration with CI/CD, and reporting capabilities to choose a solution that fits their secure development practices.