Introduction
OTA Firmware Update Platforms help organizations remotely deliver firmware, software, configuration, and security updates to connected devices without physically accessing them. These platforms are especially important for IoT devices, embedded systems, gateways, smart appliances, industrial devices, healthcare devices, automotive systems, and edge hardware deployed in the field.
Real-world use cases include fixing firmware bugs, deploying security patches, rolling out new device features, updating Linux-based gateways, managing MCU firmware, controlling staged rollouts, recovering failed updates, and tracking device version history. Buyers should evaluate rollback support, secure update delivery, device compatibility, fleet targeting, deployment scheduling, observability, integration APIs, scalability, audit logs, and operational reliability.
Best for: IoT product teams, embedded engineering teams, DevOps teams, device manufacturers, industrial IoT teams, automotive platforms, smart device companies, and enterprises managing connected device fleets.
Not ideal for: Very small prototypes, offline-only devices, teams without firmware release discipline, or products where updates are rarely required after deployment.
Key Trends in OTA Firmware Update Platforms
- Secure firmware signing and verification are becoming standard requirements.
- Staged rollouts help reduce the risk of failed mass deployments.
- Rollback and A/B update mechanisms are critical for production safety.
- OTA is expanding beyond firmware into containers, files, AI models, and configuration updates.
- Device observability is being combined with OTA to detect failures faster.
- Cloud-native fleet management is replacing manual update workflows.
- Embedded Linux, RTOS, and MCU support are becoming key differentiators.
- Compliance, audit logs, and deployment history matter for regulated industries.
- Edge and industrial devices need offline-tolerant update strategies.
- API-driven OTA workflows are becoming important for DevOps automation.
How We Selected These Tools
- Market adoption and recognition in IoT and embedded device management
- OTA reliability, rollback support, and update safety controls
- Support for Linux, RTOS, MCU, gateways, and edge devices
- Security capabilities such as signing, encryption, access control, and audit logs
- Integration with cloud, DevOps, CI/CD, and device management workflows
- Scalability for small fleets, mid-sized fleets, and enterprise deployments
- Reporting, observability, and fleet visibility capabilities
- Ease of deployment and developer experience
- Suitability for industrial, consumer, healthcare, and enterprise IoT use cases
- Support, documentation, ecosystem maturity, and implementation flexibility
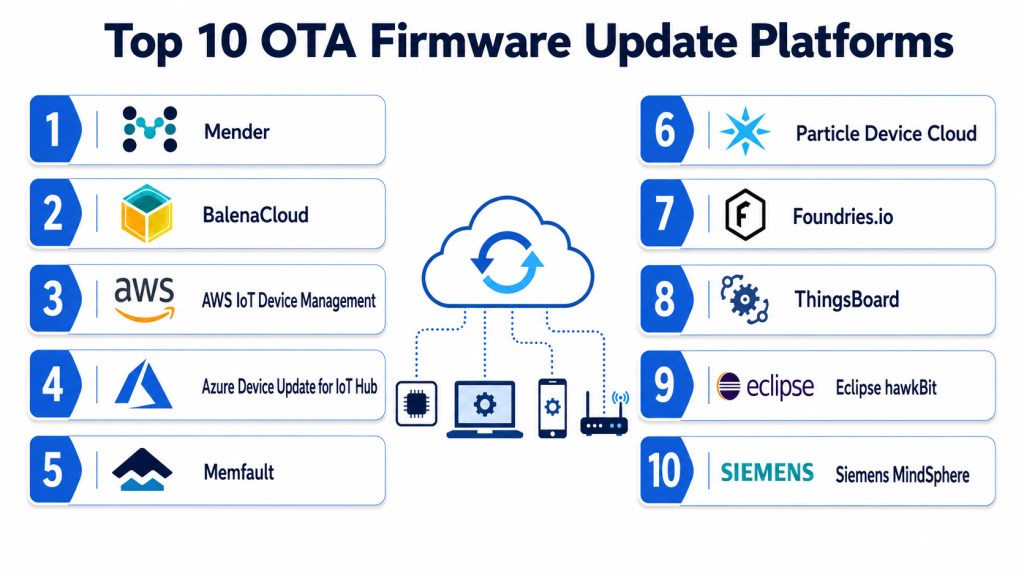
Top 10 OTA Firmware Update Platforms
#1 — Mender
Short description: Mender is a dedicated OTA software update platform for connected devices, especially embedded Linux and IoT fleets. It focuses on secure, reliable, and scalable update delivery with rollback support and deployment control. Mender is well suited for teams that need production-grade firmware and software updates without building the full OTA stack themselves. It supports both managed and self-hosted deployment models, making it flexible for enterprise and regulated environments.
Key Features
- Secure OTA firmware and software updates
- A/B update and rollback support
- Deployment scheduling and phased rollouts
- Device grouping and fleet targeting
- Support for embedded Linux and related environments
- Audit-ready deployment tracking
- API-driven update automation
Pros
- Strong focus on OTA reliability
- Good fit for embedded Linux devices
- Self-hosted and managed options available
- Suitable for enterprise and regulated deployments
Cons
- Requires device-side integration effort
- Advanced capabilities may need higher plans
- Less ideal for very simple consumer prototypes
- MCU support may require careful architecture planning
Platforms / Deployment
Linux / Embedded Linux / IoT Devices
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports secure update delivery, access controls, and deployment tracking. Specific certifications and compliance coverage should be verified during procurement.
Integrations & Ecosystem
Mender works well in engineering-led IoT environments where firmware releases are managed through structured pipelines and device fleets need reliable update control.
- CI/CD pipelines
- Device management workflows
- Embedded Linux build systems
- Cloud infrastructure
- Monitoring and logging tools
- APIs for automation
Support & Community
Mender offers documentation, developer resources, enterprise support options, and an active embedded systems ecosystem.
#2 — Memfault
Short description: Memfault combines OTA firmware updates with device observability, crash reporting, logs, metrics, and fleet health monitoring. It is especially useful for teams that want to deploy updates and immediately understand whether the update improved or harmed device reliability. Memfault works well for embedded, MCU, RTOS, Linux, and Android-based device fleets. It is a strong choice for teams that care about both firmware delivery and post-deployment diagnostics.
Key Features
- OTA firmware update management
- Device observability and fleet health monitoring
- Crash reports, logs, metrics, and traces
- Staged rollouts and release monitoring
- Device cohort targeting
- Firmware version performance comparison
- Alerts for regressions and device issues
Pros
- Combines OTA with observability
- Strong for embedded engineering teams
- Helps detect bad releases quickly
- Useful for debugging production device issues
Cons
- May be more than teams need if they only want basic OTA
- Requires SDK or agent integration
- Pricing may vary by device scale and features
- Teams need processes to act on observability insights
Platforms / Deployment
MCU / RTOS / Linux / Android / IoT Devices
Cloud
Security & Compliance
Supports secure OTA workflows and access management. Audit logging and advanced controls may depend on plan and configuration.
Integrations & Ecosystem
Memfault is strong for firmware engineering workflows where release health, crash diagnostics, and OTA delivery are connected.
- Embedded firmware toolchains
- CI/CD pipelines
- Device telemetry workflows
- Cloud dashboards
- Alerting tools
- Engineering debugging processes
Support & Community
Memfault provides documentation, technical guides, engineering-focused support, and strong resources for embedded development teams.
#3 — balenaCloud
Short description: balenaCloud is a fleet management platform for connected Linux devices, with strong support for container-based application updates. It is useful for teams deploying software to edge devices, gateways, kiosks, industrial systems, and IoT products. Rather than focusing only on firmware images, balenaCloud helps teams manage containers, device state, remote access, and fleet operations. It is a strong fit for Linux-based edge fleets.
Key Features
- Container-based OTA application updates
- Fleet and device group management
- Remote device access and diagnostics
- Linux-based device management
- Release tracking and deployment control
- Device environment variables and configuration management
- Monitoring and fleet visibility
Pros
- Excellent for Linux edge devices
- Strong container-based deployment workflow
- Developer-friendly platform
- Good for distributed device fleets
Cons
- Less suitable for low-level MCU firmware updates
- Works best with balena ecosystem patterns
- Requires containerized application architecture
- Some advanced fleet controls may require planning
Platforms / Deployment
Linux / Edge Devices / IoT Gateways
Cloud / Hybrid
Security & Compliance
Supports secure device communication, access control, and managed deployment workflows. Specific compliance details should be verified directly.
Integrations & Ecosystem
balenaCloud fits well with modern DevOps-style edge deployments where applications are packaged and updated through containers.
- Docker-based workflows
- Git-based deployment processes
- Edge gateways
- Remote access tools
- Monitoring dashboards
- API-based automation
Support & Community
balena has strong developer documentation, community resources, tutorials, and commercial support options.
#4 — Particle
Short description: Particle provides an IoT platform with device connectivity, fleet management, cloud services, and OTA firmware updates. It is especially popular for connected products, prototypes, and production IoT deployments using Particle hardware and ecosystem tools. Particle helps teams manage firmware releases, device state, messaging, and fleet visibility from one platform. It is a strong option for teams that want hardware, connectivity, and OTA management together.
Key Features
- OTA firmware updates
- Fleet management dashboard
- Device cloud connectivity
- Device groups and product management
- Firmware version tracking
- Messaging and event handling
- Hardware and software ecosystem support
Pros
- Strong end-to-end IoT ecosystem
- Good for connected product teams
- Simplifies device connectivity and OTA
- Useful for fast development and production scaling
Cons
- Best value inside Particle ecosystem
- Less flexible for completely custom hardware stacks
- Enterprise requirements may need careful review
- Advanced controls may depend on plan
Platforms / Deployment
Particle Devices / IoT Hardware / Embedded Devices
Cloud
Security & Compliance
Supports secure device-cloud communication and access controls. Specific compliance certifications should be verified directly.
Integrations & Ecosystem
Particle works well for teams that want device hardware, connectivity, firmware updates, and cloud management in one connected ecosystem.
- Particle hardware
- Particle cloud
- Webhooks and APIs
- Cloud services
- Mobile and web applications
- Device event workflows
Support & Community
Particle has strong documentation, developer forums, tutorials, community support, and commercial support options.
#5 — AWS IoT Device Management
Short description: AWS IoT Device Management helps organizations onboard, organize, monitor, and manage IoT devices at scale, including software and firmware update workflows through the AWS IoT ecosystem. It is best suited for teams already using AWS for cloud infrastructure, device messaging, analytics, and security. AWS provides flexible building blocks rather than a narrowly dedicated OTA-only solution. It works well for enterprise IoT teams with cloud engineering capacity.
Key Features
- Device fleet organization and management
- Remote actions and update workflows
- Integration with AWS IoT services
- Device indexing and fleet visibility
- Secure device identity and access management
- Rules, messaging, and event-driven workflows
- Scalable cloud infrastructure
Pros
- Strong cloud scalability
- Deep AWS ecosystem integration
- Flexible for complex enterprise IoT architectures
- Good for teams already using AWS services
Cons
- Requires cloud engineering expertise
- OTA workflows may need additional configuration
- Pricing can become complex at scale
- Not as simple as dedicated OTA-only platforms
Platforms / Deployment
IoT Devices / Linux / Embedded Systems / Gateways
Cloud
Security & Compliance
Uses AWS security controls such as IAM, encryption, certificates, access policies, logging, and monitoring. Compliance coverage depends on AWS service configuration and customer architecture.
Integrations & Ecosystem
AWS IoT Device Management fits well into broader AWS-based device, data, analytics, and automation ecosystems.
- AWS IoT Core
- AWS Lambda
- Amazon CloudWatch
- Amazon S3
- AWS IAM
- CI/CD and DevOps workflows
Support & Community
AWS provides extensive documentation, enterprise support plans, training, architecture guidance, and a large cloud community.
#6 — Azure IoT Hub Device Update
Short description: Azure IoT Hub Device Update provides managed update capabilities for IoT devices connected through Azure IoT services. It supports structured update deployment, device grouping, reporting, and integration with Microsoft cloud services. It is best suited for organizations already using Azure for IoT, identity, analytics, security, and device operations. It works well for enterprise teams that need cloud-native OTA control inside the Microsoft ecosystem.
Key Features
- Managed OTA update deployment
- Device grouping and update targeting
- Integration with Azure IoT Hub
- Update compliance and reporting
- Deployment history and monitoring
- Cloud-native fleet update orchestration
- Enterprise identity and access integration
Pros
- Strong fit for Azure-based IoT teams
- Managed update service reduces custom work
- Good reporting and deployment visibility
- Scales with Microsoft cloud infrastructure
Cons
- Best value inside Azure ecosystem
- Requires Azure IoT architecture knowledge
- Device-side compatibility must be planned
- May be complex for smaller teams
Platforms / Deployment
IoT Devices / Linux / Edge Devices / Embedded Systems
Cloud
Security & Compliance
Uses Azure security controls such as identity management, encryption, role-based access, and monitoring. Compliance coverage depends on Microsoft cloud configuration and customer requirements.
Integrations & Ecosystem
Azure IoT Hub Device Update is strongest for teams already using Microsoft cloud, identity, analytics, and enterprise IT systems.
- Azure IoT Hub
- Azure IoT Edge
- Azure Monitor
- Microsoft Entra ID
- DevOps pipelines
- Cloud analytics services
Support & Community
Microsoft provides documentation, enterprise support, partner ecosystem, and cloud architecture guidance.
#7 — Golioth
Short description: Golioth is an IoT cloud platform designed for connected devices, especially embedded and constrained devices. It supports device management, messaging, data routing, and OTA firmware updates for modern IoT product teams. Golioth is a strong fit for teams building embedded devices that need cloud connectivity and device lifecycle management without building everything from scratch. It is especially relevant for Zephyr-based and embedded development workflows.
Key Features
- OTA firmware update support
- Device management and fleet visibility
- Secure device communication
- Data routing and messaging
- Support for embedded development workflows
- API-based cloud integration
- Device credential and identity management
Pros
- Strong fit for embedded IoT teams
- Developer-friendly platform
- Useful for constrained devices
- Good cloud-device integration model
Cons
- Smaller ecosystem than hyperscale cloud providers
- May require embedded development expertise
- Advanced enterprise features should be verified
- Best fit depends on device architecture
Platforms / Deployment
Embedded Devices / RTOS / IoT Devices
Cloud
Security & Compliance
Supports secure device identity and communication. Specific certifications, audit logs, and compliance coverage should be verified directly.
Integrations & Ecosystem
Golioth works well for engineering teams building connected embedded products that need OTA, telemetry, messaging, and cloud APIs.
- Embedded SDKs
- Zephyr-based workflows
- Cloud APIs
- Data routing tools
- Device telemetry systems
- Firmware release pipelines
Support & Community
Golioth provides documentation, developer resources, technical support, and community content for embedded teams.
#8 — FoundriesFactory
Short description: FoundriesFactory helps teams build, deploy, update, and manage secure Linux-based IoT and edge devices. It combines embedded Linux, CI/CD, security, and fleet update workflows into one platform. It is especially useful for organizations that want production-grade Linux device platforms with secure update delivery. FoundriesFactory fits teams managing smart gateways, industrial devices, edge appliances, and Linux-based hardware products.
Key Features
- Secure Linux OTA updates
- CI/CD-driven device software delivery
- Fleet management and deployment tracking
- Secure boot and device security support
- Container and application update workflows
- Edge device lifecycle management
- Production-focused Linux platform tooling
Pros
- Strong for Linux-based edge devices
- Good DevOps and CI/CD alignment
- Security-focused platform approach
- Suitable for production device fleets
Cons
- Best suited for Linux device products
- Requires embedded Linux expertise
- May be too advanced for simple IoT projects
- Ecosystem is more specialized than large cloud providers
Platforms / Deployment
Linux / Edge Devices / IoT Gateways
Cloud / Hybrid
Security & Compliance
Supports secure update workflows and Linux device security patterns. Specific compliance certifications should be verified directly.
Integrations & Ecosystem
FoundriesFactory is useful for teams that want secure embedded Linux delivery connected with modern DevOps pipelines.
- Linux build systems
- CI/CD pipelines
- Container workflows
- Edge device fleets
- Security tooling
- Cloud integrations
Support & Community
FoundriesFactory provides technical documentation, engineering support, onboarding resources, and specialized Linux device expertise.
#9 — Eclipse hawkBit
Short description: Eclipse hawkBit is an open-source framework for managing software updates to connected devices. It is often used by teams that want more control over OTA infrastructure and are comfortable building or self-hosting update workflows. hawkBit is useful for industrial, embedded, and enterprise environments where customization and open-source flexibility are important. It is best suited for teams with engineering resources to operate and extend the platform.
Key Features
- Open-source OTA update management
- Software rollout control
- Device targeting and deployment tracking
- API-based update workflows
- Campaign and rollout management
- Integration-friendly architecture
- Suitable for self-hosted deployments
Pros
- Open-source flexibility
- Good for custom OTA architectures
- Strong control over deployment logic
- Useful for self-hosted environments
Cons
- Requires engineering and operations expertise
- Less turnkey than managed platforms
- Support depends on internal capability or partners
- Device-side integration must be planned carefully
Platforms / Deployment
IoT Devices / Embedded Systems / Linux / Gateways
Self-hosted / Hybrid
Security & Compliance
Security depends heavily on deployment architecture, access controls, signing workflow, and operational setup. Compliance is not publicly stated as a managed platform claim.
Integrations & Ecosystem
hawkBit fits organizations that want to build a custom OTA architecture around open APIs and self-managed infrastructure.
- Custom device agents
- CI/CD pipelines
- Self-hosted infrastructure
- Enterprise middleware
- Industrial IoT systems
- API-based automation
Support & Community
Community resources, open-source documentation, and partner support may be available depending on implementation approach.
#10 — ThingsBoard
Short description: ThingsBoard is an IoT platform that supports device management, telemetry, dashboards, rules, and OTA update workflows. It is useful for organizations that want broader IoT platform capabilities along with firmware update management. ThingsBoard can support both cloud and self-hosted models, making it flexible for different deployment needs. It is a good fit for teams that want dashboards, device data, and OTA in a single platform.
Key Features
- Device management and provisioning
- OTA update workflows
- Telemetry collection and visualization
- Rules engine and automation
- Dashboards and reporting
- Multi-tenant architecture
- Cloud and self-hosted deployment options
Pros
- Broader IoT platform capabilities
- Flexible deployment options
- Useful dashboards and rules engine
- Good for teams needing OTA plus telemetry
Cons
- OTA may not be as deep as dedicated platforms
- Requires configuration for production workflows
- Advanced scalability needs planning
- Some enterprise capabilities may require paid editions
Platforms / Deployment
IoT Devices / Gateways / Linux / Embedded Systems
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports access controls and secure communication features. Specific certifications and compliance claims should be verified based on edition and deployment model.
Integrations & Ecosystem
ThingsBoard works well where OTA update management needs to be connected with dashboards, telemetry, rules, and IoT operations.
- IoT gateways
- MQTT and device protocols
- Rule engine workflows
- Cloud services
- Dashboards and analytics
- APIs and custom integrations
Support & Community
ThingsBoard provides documentation, community resources, commercial support options, and an active IoT user ecosystem.
Comparison Table
| Tool Name | Best For | Platform Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Mender | Embedded Linux OTA | Linux / IoT Devices | Cloud / Self-hosted / Hybrid | A/B updates and rollback | N/A |
| Memfault | OTA plus observability | MCU / RTOS / Linux / Android | Cloud | OTA with device diagnostics | N/A |
| balenaCloud | Linux edge fleets | Linux / Edge Devices | Cloud / Hybrid | Container-based updates | N/A |
| Particle | Connected product teams | Particle / IoT Devices | Cloud | Hardware-to-cloud OTA ecosystem | N/A |
| AWS IoT Device Management | AWS-based IoT fleets | IoT / Linux / Gateways | Cloud | Scalable cloud fleet management | N/A |
| Azure IoT Hub Device Update | Azure IoT teams | IoT / Linux / Edge Devices | Cloud | Managed Azure OTA workflow | N/A |
| Golioth | Embedded IoT teams | RTOS / Embedded Devices | Cloud | Developer-friendly embedded OTA | N/A |
| FoundriesFactory | Secure Linux edge devices | Linux / Edge Devices | Cloud / Hybrid | CI/CD-driven Linux updates | N/A |
| Eclipse hawkBit | Open-source OTA control | IoT / Embedded / Linux | Self-hosted / Hybrid | Open-source rollout management | N/A |
| ThingsBoard | IoT platform plus OTA | IoT / Gateways / Linux | Cloud / Self-hosted / Hybrid | OTA with telemetry dashboards | N/A |
Evaluation & Scoring
| Tool Name | Core 25% | Ease 15% | Integrations 15% | Security 10% | Performance 10% | Support 10% | Value 15% | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Mender | 9 | 8 | 8 | 8.5 | 8.5 | 8 | 8 | 8.4 |
| Memfault | 9 | 8 | 8.5 | 8 | 8.5 | 8 | 8 | 8.4 |
| balenaCloud | 8.5 | 8.5 | 8 | 8 | 8 | 8 | 8 | 8.2 |
| Particle | 8 | 8.5 | 8 | 8 | 8 | 8 | 8 | 8.1 |
| AWS IoT Device Management | 8.5 | 7 | 9 | 9 | 9 | 8 | 7.5 | 8.3 |
| Azure IoT Hub Device Update | 8.5 | 7.5 | 9 | 9 | 8.5 | 8 | 7.5 | 8.3 |
| Golioth | 8 | 8 | 7.5 | 8 | 8 | 7.5 | 8 | 7.9 |
| FoundriesFactory | 8.5 | 7.5 | 8 | 8.5 | 8 | 7.5 | 7.5 | 8.0 |
| Eclipse hawkBit | 8 | 6.5 | 8 | 7 | 7.5 | 6.5 | 8.5 | 7.4 |
| ThingsBoard | 7.5 | 7.5 | 8 | 7.5 | 7.5 | 7.5 | 8 | 7.7 |
These scores are comparative and should be used as a starting point, not as a universal ranking. A tool with a slightly lower total may still be the best fit if it supports your device architecture, rollback model, update size, cloud stack, or compliance workflow. Dedicated OTA platforms usually score higher for firmware reliability, while broader IoT platforms may offer stronger telemetry, dashboards, and device lifecycle features.
Which OTA Firmware Update Platform Is Right for You?
Solo / Freelancer
For prototypes and small projects, Particle, Golioth, or ThingsBoard can be practical depending on the device stack. If the goal is quick IoT development with managed connectivity, Particle is simple and integrated. If the product is embedded and developer-led, Golioth can be a strong option. For users who want dashboards and device data along with OTA, ThingsBoard may be useful.
SMB
SMBs should prioritize ease of deployment, update reliability, rollback controls, and support. Mender is a strong choice for embedded Linux fleets, while balenaCloud is useful for container-based Linux devices. Memfault is ideal if the team wants observability and OTA together. SMBs should avoid building OTA from scratch unless they have strong embedded security and DevOps expertise.
Mid-Market
Mid-market teams often need staged rollouts, fleet segmentation, version tracking, and incident response workflows. Mender, Memfault, balenaCloud, Golioth, and FoundriesFactory can be strong options depending on device architecture. Teams should evaluate how updates are signed, how rollback works, how failures are detected, and how deployment history is audited.
Enterprise
Enterprises should evaluate OTA platforms based on security, scalability, compliance, observability, and integration with existing cloud or IT operations. AWS IoT Device Management and Azure IoT Hub Device Update are strong for organizations already invested in those cloud ecosystems. Mender and Memfault are strong dedicated OTA choices. FoundriesFactory is suitable for secure Linux edge device programs.
Budget vs Premium
Budget-conscious teams may consider open-source or self-hosted options such as Eclipse hawkBit or ThingsBoard, but they should account for engineering and operations effort. Premium managed platforms reduce operational burden and provide stronger support, reporting, and deployment controls. The lowest license cost is not always the lowest total cost if failed updates cause device downtime or field service costs.
Feature Depth vs Ease of Use
Memfault and Mender offer deep OTA reliability features, while Particle and balenaCloud are easier for teams that fit their ecosystems. AWS and Azure provide powerful building blocks but require cloud architecture knowledge. Eclipse hawkBit offers customization but needs internal engineering resources. Teams should choose based on device complexity, team skill, and production risk.
Integrations & Scalability
OTA platforms should connect with CI/CD pipelines, device identity systems, cloud infrastructure, monitoring tools, and fleet dashboards. For large fleets, APIs, deployment automation, device grouping, update history, and alerting are essential. Teams should test the platform with real firmware images, real connectivity conditions, and real rollback scenarios before wide deployment.
Security & Compliance Needs
Security is one of the most important OTA buying factors. Buyers should verify image signing, secure boot compatibility, encrypted transport, device authentication, role-based access, audit logs, rollback protection, and release approval workflows. Regulated industries should also validate compliance documentation, deployment history, and operational controls before production rollout.
Frequently Asked Questions
1. What is an OTA Firmware Update Platform?
An OTA Firmware Update Platform allows teams to remotely deliver firmware, software, or configuration updates to connected devices. It helps avoid manual field servicing and keeps devices secure and functional after deployment. These platforms are widely used in IoT, embedded systems, industrial devices, and smart products.
2. Why are OTA updates important for IoT devices?
OTA updates allow teams to fix bugs, patch vulnerabilities, improve performance, and add features after devices are already deployed. Without OTA, organizations may need expensive physical servicing or device recalls. Reliable OTA is essential for long-term device lifecycle management.
3. What is rollback in OTA firmware updates?
Rollback allows a device to return to a previous working firmware version if a new update fails. This is important because failed updates can make devices unusable. A/B partitioning, recovery partitions, and version validation are common rollback strategies.
4. Which OTA platform is best for embedded Linux?
Mender, balenaCloud, FoundriesFactory, and AWS or Azure IoT services can be strong choices for embedded Linux depending on architecture. Mender is often preferred for image-based updates and rollback. balenaCloud is strong for container-based Linux edge deployments.
5. Which OTA platform is best for MCU or RTOS devices?
Memfault and Golioth are strong options for MCU and RTOS-focused device teams. Particle can also be a good fit for teams using its hardware and cloud ecosystem. The best choice depends on memory limits, bootloader strategy, connectivity, security model, and firmware release workflow.
6. Are OTA updates secure?
OTA updates can be secure when platforms support firmware signing, device authentication, encrypted transport, access control, and audit logging. Security also depends on device bootloader design and key management. Buyers should verify security architecture before production rollout.
7. Can OTA platforms support staged rollouts?
Yes, many OTA platforms support staged rollouts, device groups, cohorts, or deployment waves. This allows teams to update a small group first, monitor results, and then expand deployment. Staged rollout reduces the risk of fleet-wide failures.
8. Can OTA updates work with poor connectivity?
Some OTA platforms support resumable downloads, deployment retry logic, bandwidth controls, and update scheduling. Devices with poor connectivity need careful update design. Teams should test update behavior under weak networks, power loss, and interrupted downloads.
9. What integrations matter most for OTA platforms?
Important integrations include CI/CD pipelines, cloud infrastructure, device identity systems, monitoring tools, alerting systems, and analytics dashboards. API access is also important for automating releases. For enterprise teams, integration with security and compliance workflows is also valuable.
10. Should companies build OTA in-house?
Building OTA in-house may work for highly specialized teams with strong embedded, security, and DevOps expertise. However, it can be risky because update failures may brick devices or create security issues. Most production teams benefit from using a proven OTA platform or framework.
Conclusion
OTA Firmware Update Platforms are essential for connected device teams that need secure, reliable, and scalable update delivery after products are deployed in the field. The best platform depends on device type, firmware architecture, connectivity model, security needs, rollout risk, and team expertise. Mender and Memfault are strong dedicated OTA choices, balenaCloud and FoundriesFactory are excellent for Linux and edge fleets, while AWS and Azure suit enterprises already invested in cloud ecosystems. Particle, Golioth, Eclipse hawkBit, and ThingsBoard serve different needs across embedded, open-source, and broader IoT platform use cases. Buyers should shortlist two or three platforms, test them with real devices, validate rollback and security controls, and run staged pilots before scaling OTA across the full fleet.