Introduction
IoT Security Platforms are specialized solutions designed to secure Internet of Things devices, networks, applications, and communication channels across enterprise and industrial environments. As organizations deploy connected devices in manufacturing, healthcare, retail, logistics, smart buildings, and critical infrastructure, the attack surface grows significantly. IoT security platforms help organizations monitor connected assets, detect anomalies, enforce policies, manage vulnerabilities, and respond to threats in real time.
Real-world use cases include securing medical IoT devices in hospitals, protecting industrial control systems in manufacturing facilities, monitoring connected retail sensors, managing smart city infrastructure, detecting unauthorized IoT devices on enterprise networks, and automating compliance reporting for regulated industries. Modern IoT security platforms increasingly use AI-driven analytics, behavioral monitoring, Zero Trust architectures, and automated remediation workflows to manage increasingly complex IoT ecosystems.
Evaluation Criteria for Buyers:
- Device discovery and asset visibility
- Threat detection and anomaly analytics
- Vulnerability and risk management
- Network segmentation and Zero Trust controls
- Integration with SIEM, SOAR, and ITSM platforms
- Scalability across large distributed IoT environments
- Compliance and reporting capabilities
- Real-time monitoring and telemetry visibility
- Ease of deployment and operational management
- Vendor support and ecosystem maturity
Best for: Enterprises, industrial organizations, healthcare providers, smart infrastructure operators, telecom providers, and security teams managing connected devices and edge environments.
Not ideal for: Small businesses with very limited IoT infrastructure, organizations without centralized security operations, or teams relying solely on traditional endpoint security without IoT-specific visibility.
Key Trends in IoT Security Platforms
- AI-assisted anomaly and behavioral threat detection
- Zero Trust security for IoT and OT environments
- Unified IT, OT, and IoT visibility dashboards
- Automated IoT device discovery and classification
- Real-time telemetry and risk scoring
- Secure edge and cloud-to-device communication
- IoT microsegmentation and policy enforcement
- Integration with SIEM, SOAR, and XDR platforms
- Compliance-focused monitoring and reporting
- Container and edge workload security for industrial IoT
How We Selected These Tools (Methodology)
- Evaluated enterprise adoption and market visibility
- Reviewed IoT asset discovery and classification capabilities
- Assessed anomaly detection and AI-driven analytics
- Analyzed scalability across industrial and enterprise environments
- Evaluated integrations with security and observability ecosystems
- Reviewed compliance and reporting functionality
- Compared deployment flexibility and network compatibility
- Assessed operational usability and automation workflows
- Considered vendor support quality and ecosystem maturity
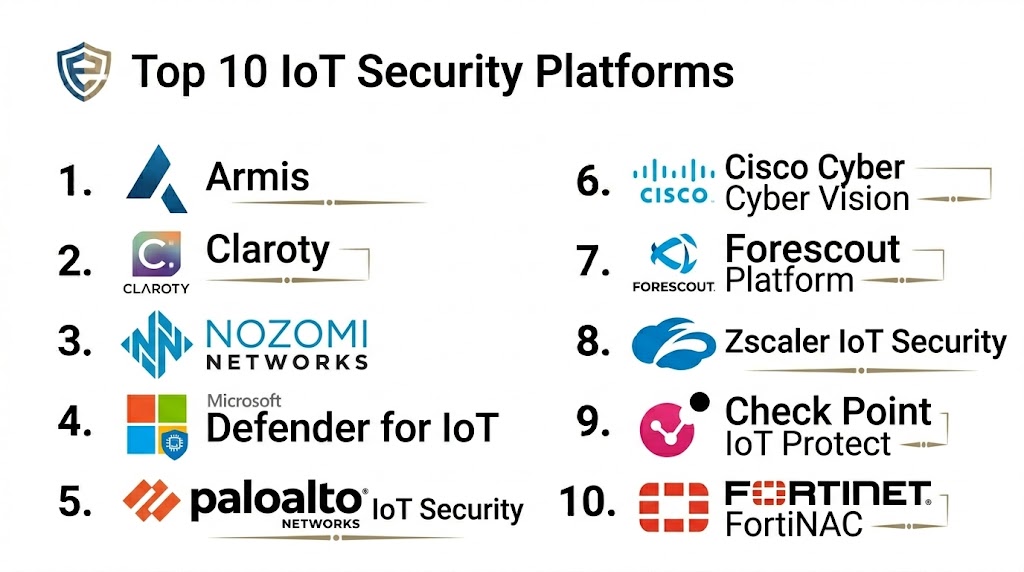
Top 10 IoT Security Platforms
1 — Armis
Short description: Armis provides agentless IoT and OT security with device discovery, behavioral analytics, vulnerability management, and real-time threat detection across connected environments.
Key Features
- Agentless device discovery and classification
- AI-driven behavioral analytics
- Risk and vulnerability management
- Real-time threat detection
- IoT and OT visibility dashboards
- Integration with SIEM and SOAR platforms
Pros
- Strong agentless visibility capabilities
- Excellent IoT and OT device coverage
- Real-time anomaly detection
Cons
- Enterprise-focused pricing
- Advanced deployments require tuning
- May require integration planning
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- RBAC, encryption, audit logging
- Compliance reporting and policy controls
Integrations & Ecosystem
Integrates with SIEM, XDR, and ITSM systems.
- Splunk
- Microsoft Sentinel
- ServiceNow, Palo Alto Networks
Support & Community
Enterprise support, onboarding assistance, and strong documentation ecosystem.
2 — Microsoft Defender for IoT
Short description: Microsoft Defender for IoT delivers agentless IoT and OT threat detection, risk analysis, and network monitoring integrated with Microsoft security ecosystems.
Key Features
- Agentless IoT discovery
- Threat intelligence and analytics
- Network traffic analysis
- Vulnerability management
- OT and industrial visibility
- Integration with Microsoft security stack
Pros
- Strong Microsoft ecosystem integration
- Good industrial network visibility
- AI-assisted threat detection
Cons
- Best suited for Microsoft-centric environments
- Advanced workflows require Azure integration
- Enterprise deployment complexity
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Encryption, RBAC, audit logs
- Microsoft compliance frameworks
Integrations & Ecosystem
Integrates deeply with Microsoft security and cloud platforms.
- Microsoft Sentinel
- Defender XDR
- Azure Security Center
Support & Community
Enterprise support and large Microsoft security community ecosystem.
3 — Claroty
Short description: Claroty focuses on securing industrial IoT and operational technology environments with deep asset visibility, anomaly detection, and threat intelligence.
Key Features
- Industrial IoT and OT asset discovery
- Threat detection and behavioral analytics
- Vulnerability management
- Secure remote access controls
- Risk scoring and prioritization
- Network segmentation support
Pros
- Strong industrial protocol support
- Excellent OT visibility
- Purpose-built for industrial environments
Cons
- Primarily focused on industrial use cases
- Premium enterprise pricing
- Requires industrial network expertise
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Encryption, RBAC, audit logging
- Compliance reporting support
Integrations & Ecosystem
Works with industrial and enterprise security systems.
- Splunk
- Palo Alto Networks
- Industrial SIEM platforms
Support & Community
Industrial cybersecurity expertise and enterprise support services.
4 — Forescout Platform
Short description: Forescout provides device visibility, network access control, compliance monitoring, and IoT threat management for enterprise and industrial environments.
Key Features
- Agentless device discovery
- Network access enforcement
- IoT compliance monitoring
- Automated policy management
- Threat detection and response
- Device risk scoring
Pros
- Strong device visibility
- Network access enforcement capabilities
- Broad ecosystem integrations
Cons
- Complex deployment in large environments
- Enterprise pricing structure
- Advanced policy management requires expertise
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Access controls, encryption, audit logs
- Policy enforcement and compliance reporting
Integrations & Ecosystem
Integrates with SIEM, NAC, and security operations tools.
- Splunk
- ServiceNow
- CrowdStrike, Palo Alto Networks
Support & Community
Enterprise support and mature documentation resources.
5 — Palo Alto Networks IoT Security
Short description: Palo Alto Networks IoT Security provides ML-driven IoT device visibility, policy enforcement, and automated risk management integrated with Prisma and Cortex ecosystems.
Key Features
- AI-based IoT device profiling
- Automated policy recommendations
- Threat detection and anomaly analysis
- Vulnerability assessment
- Integration with Zero Trust architecture
- Cloud-delivered analytics
Pros
- Strong AI-driven analytics
- Excellent integration with Palo Alto security stack
- Automated policy management
Cons
- Best fit for Palo Alto customers
- Premium enterprise pricing
- Requires ecosystem integration for full value
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Encryption, RBAC, audit logging
- Zero Trust policy controls
Integrations & Ecosystem
Works with Palo Alto cloud and security products.
- Cortex XDR
- Prisma Access
- SIEM integrations
Support & Community
Enterprise support and strong security partner ecosystem.
6 — Cisco Cyber Vision
Short description: Cisco Cyber Vision secures industrial IoT and OT networks through asset visibility, threat monitoring, and integration with Cisco networking infrastructure.
Key Features
- Industrial asset visibility
- Real-time network monitoring
- Threat and anomaly detection
- Industrial protocol analysis
- Compliance and reporting
- Integration with Cisco security stack
Pros
- Strong industrial network integration
- Good visibility into OT environments
- Real-time threat analytics
Cons
- Best suited for Cisco environments
- Complex industrial deployment planning
- Enterprise-focused pricing
Platforms / Deployment
- Cloud / Hybrid / On-prem
Security & Compliance
- Encryption, RBAC, audit trails
- Industrial compliance reporting
Integrations & Ecosystem
Integrates with Cisco networking and security systems.
- Cisco SecureX
- Cisco ISE
- SIEM integrations
Support & Community
Cisco enterprise support and industrial networking expertise.
7 — Nozomi Networks
Short description: Nozomi Networks provides IoT and OT threat detection, anomaly monitoring, and asset visibility for industrial and critical infrastructure environments.
Key Features
- Industrial IoT asset discovery
- AI-driven anomaly detection
- Threat intelligence integration
- Risk scoring and vulnerability management
- Operational visibility dashboards
- OT protocol analysis
Pros
- Strong industrial and OT security capabilities
- AI-powered anomaly detection
- Broad protocol coverage
Cons
- Focused heavily on industrial environments
- Premium deployment costs
- Specialized expertise required
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Encryption, policy management, audit logs
- Compliance reporting support
Integrations & Ecosystem
Integrates with industrial and enterprise security ecosystems.
- Splunk
- ServiceNow
- Industrial SIEM systems
Support & Community
Industrial security support and enterprise services.
8 — Trend Micro IoT Security
Short description: Trend Micro provides IoT protection with network monitoring, vulnerability management, and AI-assisted threat intelligence for connected devices.
Key Features
- IoT threat monitoring
- Vulnerability scanning and risk analysis
- Behavioral threat analytics
- Device lifecycle protection
- Integration with XDR ecosystem
- Security policy enforcement
Pros
- Strong threat intelligence capabilities
- Broad security portfolio integration
- Good cloud workload support
Cons
- Less OT-focused than industrial specialists
- Advanced analytics require tuning
- Enterprise licensing structure
Platforms / Deployment
- Cloud / Hybrid
Security & Compliance
- Encryption, RBAC, compliance reporting
- Threat intelligence integration
Integrations & Ecosystem
Works with Trend Micro security products and enterprise tools.
- Trend Vision One
- SIEM integrations
- Cloud security platforms
Support & Community
Enterprise support and established security ecosystem.
9 — Fortinet FortiNAC
Short description: FortiNAC provides IoT visibility, network access control, device profiling, and automated policy enforcement for enterprise IoT security.
Key Features
- IoT device discovery
- Network access control
- Automated segmentation policies
- Threat response workflows
- Compliance monitoring
- Device profiling and classification
Pros
- Strong NAC and segmentation capabilities
- Automated policy enforcement
- Good enterprise network visibility
Cons
- Best within Fortinet ecosystems
- Requires network infrastructure planning
- Complex large-scale deployments
Platforms / Deployment
- Cloud / On-prem / Hybrid
Security & Compliance
- Access controls, RBAC, encryption
- Compliance and policy reporting
Integrations & Ecosystem
Integrates with Fortinet security and network products.
- FortiGate
- FortiAnalyzer
- SIEM and NAC systems
Support & Community
Enterprise support and Fortinet partner ecosystem.
10 — Zscaler IoT Security
Short description: Zscaler IoT Security delivers cloud-native Zero Trust protection for IoT and OT devices with device visibility and policy enforcement.
Key Features
- Cloud-delivered IoT visibility
- Zero Trust access policies
- Device risk scoring
- Threat analytics and monitoring
- Segmentation recommendations
- Secure remote connectivity
Pros
- Strong Zero Trust security architecture
- Cloud-native deployment simplicity
- Good remote and distributed device support
Cons
- Requires Zscaler ecosystem integration
- Advanced workflows require tuning
- Premium pricing for enterprise deployments
Platforms /Deployment
- Cloud
Security & Compliance
- Zero Trust policy enforcement
- Encryption, RBAC, audit logs
Integrations & Ecosystem
Integrates with Zscaler cloud security and enterprise tools.
- Zscaler Internet Access
- SIEM integrations
- Identity provider support
Support & Community
Enterprise support and cloud security documentation ecosystem.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Armis | Enterprise IoT visibility | Enterprise IoT / OT | Cloud / Hybrid | Agentless discovery | N/A |
| Microsoft Defender for IoT | Microsoft environments | IoT / OT networks | Hybrid | Microsoft integration | N/A |
| Claroty | Industrial IoT | OT / Industrial systems | Hybrid | Industrial visibility | N/A |
| Forescout | Enterprise device control | Enterprise IoT | Hybrid | Network access enforcement | N/A |
| Palo Alto IoT Security | Zero Trust IoT | Enterprise IoT | Cloud | AI-driven profiling | N/A |
| Cisco Cyber Vision | Industrial networking | OT / Industrial systems | Hybrid | Cisco integration | N/A |
| Nozomi Networks | Critical infrastructure | Industrial IoT | Hybrid | AI anomaly detection | N/A |
| Trend Micro IoT Security | Cloud-connected IoT | Enterprise IoT | Cloud | Threat intelligence | N/A |
| Fortinet FortiNAC | Network segmentation | Enterprise networks | Hybrid | NAC enforcement | N/A |
| Zscaler IoT Security | Zero Trust cloud security | Distributed IoT | Cloud | Cloud-native Zero Trust | N/A |
Evaluation & Scoring
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Armis | 9 | 8 | 9 | 9 | 9 | 8 | 7 | 8.6 |
| Microsoft Defender for IoT | 9 | 8 | 9 | 9 | 8 | 8 | 7 | 8.5 |
| Claroty | 9 | 7 | 8 | 9 | 8 | 8 | 6 | 8.0 |
| Forescout | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Palo Alto IoT Security | 9 | 7 | 9 | 9 | 8 | 8 | 6 | 8.3 |
| Cisco Cyber Vision | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Nozomi Networks | 9 | 7 | 8 | 9 | 8 | 8 | 6 | 8.0 |
| Trend Micro IoT Security | 8 | 8 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Fortinet FortiNAC | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Zscaler IoT Security | 8 | 8 | 8 | 9 | 8 | 8 | 6 | 8.0 |
Which IoT Security Platform Is Right for You?
Solo / Freelancer
Smaller IoT deployments may benefit from lightweight cloud-based security monitoring tools or managed security services rather than full enterprise IoT security platforms.
SMB
Trend Micro IoT Security and Fortinet FortiNAC provide manageable visibility, policy enforcement, and integration capabilities without requiring highly specialized industrial security teams.
Mid-Market
Forescout, Zscaler IoT Security, and Microsoft Defender for IoT balance visibility, threat detection, and ecosystem integration for growing connected environments.
Enterprise
Armis, Claroty, Palo Alto Networks IoT Security, and Nozomi Networks deliver advanced analytics, industrial protocol visibility, Zero Trust controls, and large-scale IoT threat management.
Budget vs Premium
Budget-conscious organizations may prioritize cloud-native visibility and policy management platforms, while premium enterprise platforms focus on advanced analytics, industrial OT security, and large-scale automation.
Feature Depth vs Ease of Use
Microsoft Defender for IoT and Trend Micro emphasize usability and ecosystem integration, while Claroty and Nozomi Networks provide deeper industrial and OT-focused security visibility.
Integrations & Scalability
Large enterprises should prioritize platforms with strong integrations into SIEM, XDR, Zero Trust, NAC, and observability ecosystems. Armis, Palo Alto Networks, Cisco, and Microsoft perform strongly in enterprise integration scenarios.
Security & Compliance Needs
Organizations in healthcare, industrial, telecom, energy, or critical infrastructure sectors should prioritize agentless visibility, segmentation, audit logging, and compliance-focused monitoring capabilities.
Frequently Asked Questions
1. What is an IoT security platform?
An IoT security platform helps organizations discover, monitor, secure, and manage connected IoT and OT devices across enterprise and industrial environments.
2. Why are IoT security tools important?
IoT devices often lack traditional endpoint protections and can create major attack surfaces. IoT security tools improve visibility, threat detection, and policy enforcement.
3. What types of devices are monitored?
These platforms monitor industrial systems, smart sensors, healthcare devices, retail systems, cameras, gateways, and other connected infrastructure.
4. What is agentless IoT security?
Agentless security means devices are monitored without installing software directly on them, typically using network traffic analysis and passive monitoring.
5. How do these platforms detect threats?
They use behavioral analytics, AI-assisted anomaly detection, threat intelligence, and traffic monitoring to identify suspicious activity.
6. Can IoT security platforms integrate with SIEM tools?
Yes. Most enterprise IoT security platforms integrate with SIEM, SOAR, XDR, NAC, and observability systems for centralized operations.
7. What industries use IoT security platforms the most?
Manufacturing, healthcare, energy, telecom, logistics, retail, transportation, and critical infrastructure sectors are major adopters.
8. How do these tools improve compliance?
They provide audit logs, asset inventories, risk scoring, segmentation controls, and reporting capabilities required for regulatory and internal compliance programs.
9. What is IoT microsegmentation?
Microsegmentation isolates devices or workloads into smaller network zones to reduce lateral movement and limit the impact of cyberattacks.
10. What deployment challenges should organizations expect?
Organizations should prepare for device compatibility issues, network complexity, telemetry scaling, policy tuning, and integration planning with existing security systems.
Conclusion
IoT Security Platforms have become essential for organizations operating connected devices across enterprise, industrial, healthcare, telecom, and smart infrastructure environments. SMBs can benefit from platforms like Trend Micro IoT Security or Fortinet FortiNAC for manageable visibility and policy enforcement, while large enterprises often require advanced analytics, industrial protocol visibility, and Zero Trust security capabilities from Armis, Claroty, Palo Alto Networks, or Nozomi Networks. The right solution depends on device diversity, operational scale, compliance requirements, and integration needs. Organizations should shortlist several platforms, conduct pilot deployments in representative environments, validate telemetry visibility and threat detection workflows, and then scale gradually to strengthen IoT security posture across distributed infrastructures.