Introduction
Email Encryption Tools are security platforms and technologies designed to protect email communication from unauthorized access, interception, and data leakage. These tools encrypt email content, attachments, and sensitive information during transmission and storage, ensuring only intended recipients can read the messages. Modern email encryption solutions use standards such as S/MIME, PGP, TLS, and end-to-end encryption to secure communication across enterprise and consumer environments.
Organizations rely on Email Encryption Tools to secure financial records, healthcare communications, legal documents, intellectual property, and confidential customer data. Common use cases include regulatory compliance, secure client communication, protection against phishing and spoofing, encrypted file sharing, and secure executive communications. Buyers evaluating Email Encryption Tools should consider encryption standards, ease of deployment, key management, compliance support, integration with email providers, mobile compatibility, scalability, audit logging, automation capabilities, and usability for non-technical users.
Best for: Enterprises, healthcare providers, financial institutions, legal firms, government organizations, and privacy-focused businesses handling sensitive communications.
Not ideal for: Small organizations with minimal compliance requirements or businesses relying only on basic email protection features included with standard email providers.
Key Trends in Email Encryption Tools
- End-to-end encryption adoption is increasing across enterprise environments
- S/MIME and PGP remain the dominant enterprise encryption standards
- AI-powered threat detection is being integrated with email encryption platforms
- Client-side encryption is becoming more common in cloud productivity suites
- Secure email gateways are adding integrated compliance and DLP features
- Passwordless encrypted message delivery is improving usability
- Mobile-first secure email workflows are gaining adoption
- Zero-trust email security strategies are expanding across enterprises
- Encryption platforms are increasingly integrating with Microsoft 365 and Google Workspace
- Privacy-focused encrypted email providers continue to grow in popularity
How We Selected These Tools
- Evaluated market adoption across enterprise and SMB environments
- Assessed support for S/MIME, PGP, TLS, and end-to-end encryption
- Reviewed ease of deployment and key management capabilities
- Analyzed integrations with Microsoft 365, Google Workspace, and enterprise email systems
- Evaluated scalability for large organizations and global deployments
- Assessed compliance support for GDPR, HIPAA, and regulated industries
- Reviewed usability for technical and non-technical users
- Evaluated security controls including MFA, audit logs, and policy enforcement
- Assessed mobile support and cross-platform compatibility
- Considered ecosystem maturity, support quality, and overall value
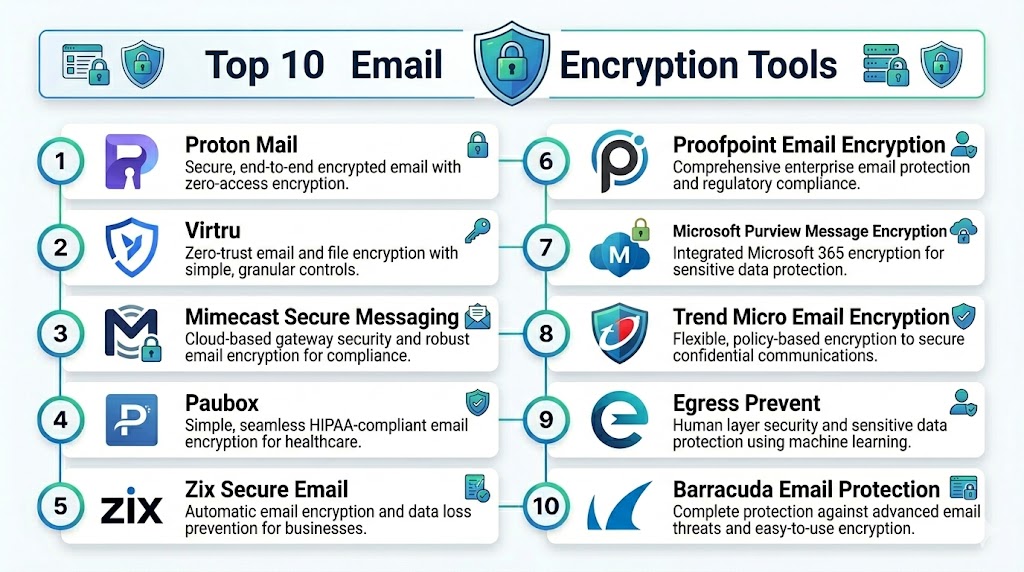
Top 10 Email Encryption Tools
1 — Proofpoint Email Encryption
Short description: Proofpoint Email Encryption is an enterprise-grade secure email platform focused on protecting sensitive communications, preventing data leaks, and supporting regulatory compliance across organizations.
Key Features
- Policy-based email encryption
- Secure message portals
- S/MIME and TLS support
- Data loss prevention integration
- Mobile-friendly encrypted messaging
- Compliance reporting and audit logs
- Automated encryption triggers
Pros
- Strong enterprise compliance capabilities
- Flexible encryption delivery methods
- Deep DLP integration
Cons
- Premium enterprise pricing
- Complex implementation for smaller teams
- Advanced policy management requires expertise
Platforms / Deployment
- Web, Windows, macOS, iOS, Android
- Cloud, Hybrid
Security & Compliance
- SSO, MFA
- HIPAA, GDPR support
- Audit logging
Integrations & Ecosystem
Proofpoint integrates with enterprise email and security ecosystems for centralized communication protection.
- Microsoft 365
- Google Workspace
- Microsoft Exchange
- SIEM platforms
- DLP systems
Support & Community
Enterprise-grade support with extensive implementation and compliance resources.
2 — Mimecast Secure Messaging
Short description: Mimecast Secure Messaging provides encrypted email delivery and secure communication workflows for enterprises managing sensitive information.
Key Features
- Secure email encryption
- Policy-based controls
- Secure web portal delivery
- Attachment encryption
- Data leak prevention
- Threat protection integration
- Compliance auditing
Pros
- Strong enterprise security ecosystem
- Easy encrypted email delivery
- Good compliance support
Cons
- Enterprise pricing structure
- Requires setup planning for advanced policies
- User training may be necessary
Platforms / Deployment
- Web, Windows, macOS, iOS, Android
- Cloud
Security & Compliance
- SSO
- GDPR support
- Threat detection integration
Integrations & Ecosystem
Supports enterprise productivity and security integrations.
- Microsoft 365
- Google Workspace
- Microsoft Exchange
- SIEM systems
Support & Community
Strong enterprise onboarding and technical support ecosystem.
3 — Virtru
Short description: Virtru delivers easy-to-use email encryption focused on secure collaboration for businesses using Gmail and Microsoft 365 environments.
Key Features
- End-to-end email encryption
- Gmail and Outlook integration
- Secure file sharing
- Access revocation controls
- Expiration controls
- Audit trails
- Encryption key management
Pros
- Simple user experience
- Strong Google Workspace integration
- Easy secure collaboration
Cons
- Advanced enterprise governance is limited
- Premium features increase costs
- Less customizable than enterprise-heavy platforms
Platforms / Deployment
- Web, Windows, macOS, iOS, Android
- Cloud
Security & Compliance
- End-to-end encryption
- HIPAA support
- Audit logging
Integrations & Ecosystem
Strong integration with productivity and collaboration ecosystems.
- Gmail
- Outlook
- Google Workspace
- Microsoft 365
Support & Community
Good documentation and responsive support for SMB and enterprise customers.
4 — Proton Mail
Short description: Proton Mail is a privacy-focused encrypted email platform providing end-to-end encrypted communication and secure email hosting for businesses and individuals.
Key Features
- End-to-end encrypted email
- Zero-access encryption
- Password-protected external emails
- Secure calendar integration
- Anonymous email aliases
- Mobile and desktop apps
- Tracking protection
Pros
- Strong privacy-first architecture
- Easy-to-use encrypted communication
- Good cross-platform support
Cons
- Limited enterprise workflow customization
- Advanced admin controls require premium tiers
- Subject lines are not fully encrypted
Platforms / Deployment
- Web, Windows, macOS, Linux, iOS, Android
- Cloud
Security & Compliance
- End-to-end encryption
- Zero-access architecture
- GDPR-focused privacy protections
Integrations & Ecosystem
Focused on privacy-first productivity workflows.
- Proton Calendar
- Proton Drive
- OpenPGP support
Support & Community
Large privacy-focused user community with extensive support resources.
5 — Zix Secure Email
Short description: Zix Secure Email provides policy-based encryption and secure communication workflows designed for regulated industries and enterprise organizations.
Key Features
- Automatic email encryption
- Policy enforcement
- Secure message delivery
- Compliance management
- Threat protection integration
- Encryption gateway support
- Mobile compatibility
Pros
- Strong healthcare and financial compliance support
- Automated encryption workflows
- Good enterprise scalability
Cons
- Legacy interface in some workflows
- Premium pricing
- Complex deployment for hybrid environments
Platforms / Deployment
- Web, Windows, macOS, iOS, Android
- Cloud, Hybrid
Security & Compliance
- HIPAA support
- Audit trails
- Encryption policy enforcement
Integrations & Ecosystem
Supports enterprise email and security environments.
- Microsoft 365
- Microsoft Exchange
- Google Workspace
- Compliance systems
Support & Community
Enterprise-oriented support with strong regulated-industry focus.
6 — Cisco Secure Email Encryption
Short description: Cisco Secure Email Encryption combines email encryption with advanced threat protection and enterprise email security capabilities.
Key Features
- Secure email encryption
- Advanced threat protection
- Secure message portals
- Data loss prevention
- Encryption policy management
- Compliance reporting
- Threat intelligence integration
Pros
- Strong enterprise security ecosystem
- Integrated phishing and malware protection
- Good scalability for large organizations
Cons
- Complex enterprise implementation
- Requires technical expertise
- Higher licensing costs
Platforms / Deployment
- Web, Windows, macOS
- Cloud, Hybrid
Security & Compliance
- SSO
- Threat intelligence integration
- Compliance reporting
Integrations & Ecosystem
Deep integration with Cisco security infrastructure and enterprise email systems.
- Microsoft 365
- Cisco SecureX
- SIEM platforms
- Microsoft Exchange
Support & Community
Large enterprise support ecosystem with extensive documentation.
7 — Microsoft Purview Message Encryption
Short description: Microsoft Purview Message Encryption provides integrated encryption for Microsoft 365 environments using S/MIME and policy-based protection.
Key Features
- S/MIME encryption support
- Policy-based email encryption
- Rights management integration
- Secure message portals
- Mobile compatibility
- Compliance workflows
- Encryption automation
Pros
- Native Microsoft 365 integration
- Strong enterprise scalability
- Simplified administration for Microsoft environments
Cons
- Best suited for Microsoft ecosystems
- Advanced configuration can be complex
- Some features require premium licensing
Platforms / Deployment
- Web, Windows, macOS, iOS, Android
- Cloud
Security & Compliance
- S/MIME support
- Microsoft compliance ecosystem
- Audit logging
Integrations & Ecosystem
Deep integration with Microsoft productivity and security ecosystems.
- Microsoft 365
- Microsoft Exchange
- Microsoft Defender
- Microsoft Purview
Support & Community
Large enterprise ecosystem with extensive technical documentation.
8 — Echoworx
Short description: Echoworx provides enterprise email encryption focused on secure customer communication, compliance, and scalable encryption management.
Key Features
- S/MIME and PGP support
- Secure customer communication portals
- Policy-based encryption
- Multi-language delivery
- Compliance auditing
- Branding customization
- Automated encryption workflows
Pros
- Supports both S/MIME and PGP standards
- Strong enterprise customization
- Flexible secure delivery methods
Cons
- Enterprise-focused pricing
- Complex onboarding for smaller businesses
- Requires setup planning for advanced workflows
Platforms / Deployment
- Web, Windows, macOS
- Cloud, Hybrid
Security & Compliance
- S/MIME and PGP support
- Compliance reporting
- Audit trails
Integrations & Ecosystem
Supports integration with enterprise messaging and compliance ecosystems.
- Microsoft 365
- Google Workspace
- Microsoft Exchange
- CRM systems
Support & Community
Enterprise support with dedicated implementation guidance.
9 — PreVeil
Short description: PreVeil provides end-to-end encrypted email and file sharing designed for highly regulated industries and security-conscious organizations.
Key Features
- End-to-end encrypted email
- Secure file sharing
- Compliance-focused workflows
- Encryption key ownership
- Multi-device support
- Secure collaboration
- Audit logging
Pros
- Strong security and compliance capabilities
- Good support for regulated industries
- Secure collaboration workflows
Cons
- Higher cost compared to SMB-focused tools
- Smaller ecosystem than major enterprise vendors
- Setup may require technical assistance
Platforms / Deployment
- Web, Windows, macOS, iOS, Android
- Cloud
Security & Compliance
- End-to-end encryption
- Compliance-focused architecture
- Audit logging
Integrations & Ecosystem
Supports enterprise productivity and collaboration environments.
- Microsoft Outlook
- File sharing systems
- Enterprise identity providers
Support & Community
Compliance-focused support with enterprise onboarding resources.
10 — Tuta Mail
Short description: Tuta Mail is a secure encrypted email platform designed for privacy-focused communication and secure collaboration across personal and business environments.
Key Features
- End-to-end encrypted email
- Encrypted calendar integration
- Anonymous signup options
- Password-protected external messages
- Mobile and desktop apps
- Open-source clients
- Secure search
Pros
- Strong privacy-first architecture
- Open-source applications
- Easy secure messaging workflows
Cons
- Limited enterprise workflow integration
- Fewer enterprise governance features
- Smaller ecosystem than large providers
Platforms / Deployment
- Web, Windows, macOS, Linux, iOS, Android
- Cloud
Security & Compliance
- End-to-end encryption
- Privacy-focused architecture
- Open-source clients
Integrations & Ecosystem
Focused on secure communication and productivity workflows.
- Calendar integration
- Mobile applications
- Open-source ecosystem
Support & Community
Strong privacy-focused community and documentation resources.
Comparison Table Top 10
| Tool Name | Best For | Platform Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Proofpoint Email Encryption | Enterprise compliance and DLP | Web, Windows, macOS, iOS, Android | Cloud, Hybrid | Policy-based encryption automation | N/A |
| Mimecast Secure Messaging | Enterprise secure messaging | Web, Windows, macOS, iOS, Android | Cloud | Integrated email security ecosystem | N/A |
| Virtru | Secure collaboration in Gmail and Outlook | Web, Windows, macOS, iOS, Android | Cloud | Easy end-to-end encryption | N/A |
| Proton Mail | Privacy-focused encrypted email | Web, Windows, macOS, Linux, iOS, Android | Cloud | Zero-access encryption | N/A |
| Zix Secure Email | Regulated industry compliance | Web, Windows, macOS, iOS, Android | Cloud, Hybrid | Automated encryption workflows | N/A |
| Cisco Secure Email Encryption | Enterprise email security | Web, Windows, macOS | Cloud, Hybrid | Threat protection integration | N/A |
| Microsoft Purview Message Encryption | Microsoft 365 organizations | Web, Windows, macOS, iOS, Android | Cloud | Native S/MIME integration | N/A |
| Echoworx | Enterprise customer communication | Web, Windows, macOS | Cloud, Hybrid | S/MIME and PGP support | N/A |
| PreVeil | Highly regulated industries | Web, Windows, macOS, iOS, Android | Cloud | Secure encrypted collaboration | N/A |
| Tuta Mail | Privacy-focused communication | Web, Windows, macOS, Linux, iOS, Android | Cloud | Open-source encrypted messaging | N/A |
Evaluation & Scoring
| Tool Name | Core 25% | Ease 15% | Integrations 15% | Security 10% | Performance 10% | Support 10% | Value 15% | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Proofpoint Email Encryption | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.40 |
| Mimecast Secure Messaging | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 7.95 |
| Virtru | 8 | 9 | 8 | 8 | 8 | 8 | 8 | 8.15 |
| Proton Mail | 8 | 9 | 6 | 9 | 8 | 8 | 9 | 8.10 |
| Zix Secure Email | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 7.90 |
| Cisco Secure Email Encryption | 9 | 6 | 9 | 9 | 9 | 8 | 6 | 8.00 |
| Microsoft Purview Message Encryption | 9 | 8 | 9 | 9 | 9 | 8 | 8 | 8.55 |
| Echoworx | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.75 |
| PreVeil | 8 | 7 | 7 | 9 | 8 | 7 | 7 | 7.65 |
| Tuta Mail | 7 | 9 | 6 | 9 | 8 | 7 | 9 | 7.95 |
Higher weighted scores indicate stronger balance between encryption capabilities, integrations, usability, compliance readiness, scalability, and overall value. Enterprise organizations generally prioritize governance, automation, and DLP integration, while SMBs often value simplicity and affordability. Organizations should evaluate compatibility with existing email infrastructure, compliance requirements, and user experience before selecting a long-term encryption platform.
Which Tool Is Right for You
Solo / Freelancer
- Proton Mail or Tuta Mail for affordable and privacy-focused encrypted communication
SMB
- Virtru or Zix Secure Email for easy deployment and secure collaboration workflows
Mid-Market
- Mimecast Secure Messaging or Microsoft Purview Message Encryption for stronger integrations and centralized administration
Enterprise
- Proofpoint Email Encryption or Cisco Secure Email Encryption for compliance-heavy and large-scale environments
Budget vs Premium
- Budget-friendly: Proton Mail, Tuta Mail
- Premium: Proofpoint Email Encryption, Cisco Secure Email Encryption
Feature Depth vs Ease of Use
- Advanced enterprise governance: Proofpoint Email Encryption, Microsoft Purview Message Encryption
- Easier usability: Virtru, Proton Mail
Integrations & Scalability
- Deep enterprise integrations: Microsoft Purview Message Encryption, Proofpoint Email Encryption
- Lightweight integrations: Proton Mail, Tuta Mail
Security & Compliance Needs
- Strong enterprise compliance: Proofpoint Email Encryption, Zix Secure Email
- Privacy-first communication: Proton Mail, Tuta Mail
Frequently Asked Questions
1. What are email encryption tools
Email encryption tools protect email content and attachments from unauthorized access by encrypting messages during transmission and storage.
2. What is the difference between S/MIME and PGP
S/MIME uses certificate-based encryption while PGP uses decentralized public and private key encryption. Both are widely used enterprise email encryption standards.
3. Why do organizations use email encryption
Organizations use email encryption to protect sensitive data, comply with regulations, and reduce the risk of phishing, spoofing, and data leakage.
4. Are encrypted emails fully secure
Encrypted emails greatly improve confidentiality, but security also depends on key management, user authentication, and endpoint security practices.
5. Can encrypted email work with Gmail and Outlook
Yes, many platforms integrate directly with Gmail, Outlook, Microsoft 365, and Google Workspace for seamless secure communication.
6. Are email encryption tools required for compliance
Many regulated industries such as healthcare and finance require encrypted communication to support HIPAA, GDPR, and similar compliance standards.
7. What is end-to-end encryption in email
End-to-end encryption ensures that only the sender and recipient can read the email content, preventing providers and intermediaries from accessing the data.
8. Are self-hosted email encryption systems available
Yes, some organizations deploy self-hosted encryption gateways and key management systems for greater control and governance.
9. Which industries benefit most from email encryption
Healthcare, finance, legal services, government, defense, and SaaS companies benefit significantly because they manage confidential communications.
10. How should businesses choose an email encryption tool
Organizations should evaluate encryption standards, compliance support, integrations, usability, scalability, deployment flexibility, and governance features before selecting a platform.
Conclusion
Email Encryption Tools are now essential for organizations that need secure communication, regulatory compliance, and protection against modern cyber threats. SMBs often prioritize ease of use and affordable secure messaging, while enterprises require advanced governance, automated encryption policies, and deep integration with existing productivity ecosystems. Standards such as S/MIME, PGP, and end-to-end encryption continue to dominate secure communication strategies, while cloud-native and privacy-first platforms are making encrypted communication more accessible. Businesses should evaluate compatibility with their existing email systems, compliance requirements, scalability, and user experience before making a decision. The best approach is to shortlist a few platforms, run pilot deployments, validate encryption workflows and governance controls, and ensure alignment with long-term security and compliance strategies before scaling adoption organization-wide.